This article includes a list ofgeneral references,butit lacks sufficient correspondinginline citations.(February 2015) |
Incomputer science,hierarchical protection domains,[1][2]often calledprotection rings,are mechanisms to protect data and functionality from faults (by improvingfault tolerance) and malicious behavior (by providingcomputer security).
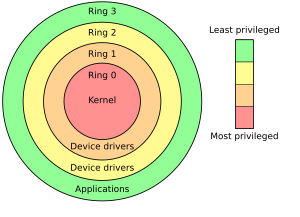
Computer operating systems provide different levels of access to resources. A protection ring is one of two or more hierarchicallevelsorlayersofprivilegewithin the architecture of acomputer system.This is generally hardware-enforced by someCPUarchitecturesthat provide differentCPU modesat the hardware ormicrocodelevel.Rings are arranged in a hierarchy from most privileged (most trusted, usually numbered zero) to least privileged (least trusted, usually with the highest ring number). On most operating systems, Ring 0 is the level with the most privileges and interacts most directly with the physical hardware such as certain CPU functionality (e.g. the control registers) and I/O controllers.
Special mechanisms are provided to allow an outer ring to access an inner ring's resources in a predefined manner, as opposed to allowing arbitrary usage. Correctly gating access between rings can improve security by preventing programs from one ring or privilege level from misusing resources intended for programs in another. For example,spywarerunning as a user program in Ring 3 should be prevented from turning on a web camera without informing the user, since hardware access should be a Ring 1 function reserved fordevice drivers.Programs such as web browsers running in higher numbered rings must request access to the network, a resource restricted to a lower numbered ring.
X86S, a recently published Intel architecture, has only ring 0 and ring 3. Ring 1 and 2 will be removed under X86S since modern OSes never utilize them.[3]
Implementations
editMultiple rings of protection were among the most revolutionary concepts introduced by theMulticsoperating system, a highly secure predecessor of today'sUnixfamily of operating systems. TheGE 645mainframe computer did have some hardware access control, including the same two modes that the other GE-600 series machines had, and segment-level permissions in itsmemory management unit( "Appending Unit" ), but that was not sufficient to provide full support for rings in hardware, so Multics supported them by trapping ring transitions in software;[4]its successor, theHoneywell 6180,implemented them in hardware, with support for eight rings;[5]Protection rings in Multics were separate from CPU modes; code in all rings other than ring 0, and some ring 0 code, ran in slave mode.[6]
However, most general-purpose systems use only two rings, even if the hardware they run on provides moreCPU modesthan that. For example, Windows 7 and Windows Server 2008 (and their predecessors) use only two rings, with ring 0 corresponding tokernel modeand ring 3 touser mode,[7]because earlier versions of Windows NT ran on processors that supported only two protection levels.[8]
Many modern CPU architectures (including the popularIntelx86architecture) include some form of ring protection, although theWindows NToperating system, like Unix, does not fully utilize this feature.OS/2does, to some extent, use three rings:[9]ring 0 for kernel code and device drivers, ring 2 for privileged code (user programs with I/O access permissions), and ring 3 for unprivileged code (nearly all user programs). UnderDOS,the kernel, drivers and applications typically run on ring 3 (however, this is exclusive to the case where protected-mode drivers or DOS extenders are used; as a real-mode OS, the system runs with effectively no protection), whereas 386 memory managers such asEMM386run at ring 0. In addition to this,DR-DOS' EMM386 3.xx can optionally run some modules (such asDPMS) on ring 1 instead.OpenVMSuses four modes called (in order of decreasing privileges) Kernel, Executive, Supervisor and User.
A renewed interest in this design structure came with the proliferation of theXenVMMsoftware,ongoing discussiononmonolithicvs.micro-kernels(particularly inUsenetnewsgroups andWeb forums), Microsoft'sRing-1design structure as part of theirNGSCBinitiative, andhypervisorsbased onx86 virtualizationsuch asIntel VT-x(formerly Vanderpool).
The original Multics system had eight rings, but many modern systems have fewer. The hardware remains aware of the current ring of the executing instructionthreadat all times, with the help of a special machine register. In some systems, areas ofvirtual memoryare instead assigned ring numbers in hardware. One example is theData General Eclipse MV/8000,in which the top three bits of theprogram counter (PC)served as the ring register. Thus code executing with the virtual PC set to 0xE200000, for example, would automatically be in ring 7, and calling a subroutine in a different section of memory would automatically cause a ring transfer.
The hardware severely restricts the ways in which control can be passed from one ring to another, and also enforces restrictions on the types of memory access that can be performed across rings. Using x86 as an example, there is a special[clarification needed]gatestructure which is referenced by thecallinstruction that transfers control in a secure way[clarification needed]towards predefined entry points in lower-level (more trusted) rings; this functions as asupervisor callin many operating systems that use the ring architecture. The hardware restrictions are designed to limit opportunities for accidental or malicious breaches of security. In addition, the most privileged ring may be given special capabilities (such as real memory addressing that bypasses the virtual memory hardware).
ARMversion 7 architecture implements three privilege levels: application (PL0), operating system (PL1), and hypervisor (PL2). Unusually, level 0 (PL0) is the least-privileged level, while level 2 is the most-privileged level.[10]ARM version 8 implements four exception levels: application (EL0), operating system (EL1), hypervisor (EL2), and secure monitor / firmware (EL3), for AArch64[11]: D1-2454 and AArch32.[11]: G1-6013
Ring protection can be combined withprocessor modes(master/kernel/privileged/supervisor modeversus slave/unprivileged/user mode) in some systems. Operating systems running on hardware supporting both may use both forms of protection or only one.
Effective use of ring architecture requires close cooperation between hardware and the operating system.[why?]Operating systems designed to work on multiple hardware platforms may make only limited use of rings if they are not present on every supported platform. Often the security model is simplified to "kernel" and "user" even if hardware provides finer granularity through rings.
Modes
editSupervisor mode
editIn computer terms,supervisor modeis a hardware-mediated flag that can be changed by code running in system-level software. System-level tasks or threads may[a]have this flag set while they are running, whereas user-level applications will not. This flag determines whether it would be possible to execute machine code operations such as modifying registers for various descriptor tables, or performing operations such as disabling interrupts. The idea of having two different modes to operate in comes from "with more power comes more responsibility" – a program in supervisor mode is trusted never to fail, since a failure may cause the whole computer system to crash.
Supervisor mode is "an execution mode on some processors which enables execution of all instructions, including privileged instructions. It may also give access to a different address space, to memory management hardware and to other peripherals. This is the mode in which the operating system usually runs."[12]
In a monolithickernel,the operating system runs in supervisor mode and the applications run in user mode. Other types ofoperating systems,like those with anexokernelormicrokernel,do not necessarily share this behavior.
Some examples from the PC world:
- Linux,macOSandWindowsare three operating systems that use supervisor/user mode. To perform specialized functions, user mode code must perform asystem callinto supervisor mode or even to the kernel space where trusted code of the operating system will perform the needed task and return the execution back to the userspace. Additional code can be added into kernel space through the use ofloadable kernel modules,but only by a user with the requisite permissions, as this code is not subject to the access control and safety limitations of user mode.
- DOS(for as long as no 386 memory manager such asEMM386is loaded), as well as other simple operating systems and many embedded devices run in supervisor mode permanently, meaning that drivers can be written directly as user programs.
Most processors have at least two different modes. Thex86-processors have four different modes divided into four different rings. Programs that run in Ring 0 can doanythingwith the system, and code that runs in Ring 3 should be able to fail at any time without impact to the rest of the computer system. Ring 1 and Ring 2 are rarely used, but could be configured with different levels of access.
In most existing systems, switching from user mode to kernel mode has an associated high cost in performance. It has been measured, on the basic requestgetpid,to cost 1000–1500 cycles on most machines. Of these just around 100 are for the actual switch (70 from user to kernel space, and 40 back), the rest is "kernel overhead".[13][14]In theL3 microkernel,the minimization of this overhead reduced the overall cost to around 150 cycles.[13]
Maurice Wilkeswrote:[15]
... it eventually became clear that the hierarchical protection that rings provided did not closely match the requirements of the system programmer and gave little or no improvement on the simple system of having two modes only. Rings of protection lent themselves to efficient implementation in hardware, but there was little else to be said for them. [...] The attractiveness of fine-grained protection remained, even after it was seen that rings of protection did not provide the answer... This again proved a blind alley...
To gain performance and determinism, some systems place functions that would likely be viewed as application logic, rather than as device drivers, in kernel mode; security applications (access control,firewalls,etc.) and operating system monitors are cited as examples. At least one embedded database management system,eXtremeDB Kernel Mode,has been developed specifically for kernel mode deployment, to provide a local database for kernel-based application functions, and to eliminate thecontext switchesthat would otherwise occur when kernel functions interact with a database system running in user mode.[16]
Functions are also sometimes moved across rings in the other direction. The Linux kernel, for instance, injects into processes avDSOsection which contains functions that would normally require a system call, i.e. a ring transition. Instead of doing a syscall these functions use static data provided by the kernel. This avoids the need for a ring transition and so is more lightweight than a syscall. The function gettimeofday can be provided this way.
Hypervisor mode
editRecent CPUs from Intel and AMD offerx86 virtualizationinstructions for ahypervisorto control Ring 0 hardware access. Although they are mutually incompatible, bothIntel VT-x(codenamed "Vanderpool" ) andAMD-V(codenamed "Pacifica" ) allow a guest operating system to run Ring 0 operations natively without affecting other guests or the host OS.
Beforehardware-assisted virtualization,guest operating systems ran under ring 1. Any attempt that requires a higher privilege level to perform (ring 0) will produce an interrupt and then be handled using software; this is called "Trap and Emulate".
To assist virtualization and reduce overhead caused by the reason above, VT-x and AMD-V allow the guest to run under Ring 0. VT-x introduces VMX Root/Non-root Operation: The hypervisor runs in VMX Root Operation mode, possessing the highest privilege. Guest OS runs in VMX Non-Root Operation mode, which allows them to operate at ring 0 without having actual hardware privileges. VMX non-root operation and VMX transitions are controlled by a data structure called a virtual-machine control.[17]These hardware extensions allow classical "Trap and Emulate" virtualization to perform on x86 architecture but now with hardware support.
Privilege level
editAprivilege levelin thex86instruction setcontrols the access of the program currently running on the processor to resources such as memory regions, I/O ports, and special instructions. There are 4 privilege levels ranging from 0 which is the most privileged, to 3 which is least privileged. Most modern operating systems use level 0 for the kernel/executive, and use level 3 for application programs. Any resource available to level n is also available to levels 0 to n, so the privilege levels are rings. When a lesser privileged process tries to access a higher privileged process, ageneral protection faultexception is reported to the OS.
It is not necessary to use all four privilege levels. Currentoperating systemswith wide market share includingMicrosoft Windows,macOS,Linux,iOSandAndroidmostly use apagingmechanism with only one bit to specify the privilege level as either Supervisor or User (U/S Bit).Windows NTuses the two-level system.[18] The real mode programs in 8086 are executed at level 0 (highest privilege level) whereas virtual mode in 8086 executes all programs at level 3.[19]
Potential future uses for the multiple privilege levels supported by the x86 ISA family includecontainerizationandvirtual machines.A host operating system kernel could use instructions with full privilege access (kernel mode), whereas applications running on the guest OS in a virtual machine or container could use the lowest level of privileges in user mode. The virtual machine and guest OS kernel could themselves use an intermediate level of instruction privilege to invoke andvirtualizekernel-mode operations such assystem callsfrom the point of view of the guest operating system.[20]
IOPL
editTheIOPL(I/O Privilege level) flag is a flag found on all IA-32 compatiblex86 CPUs.It occupies bits 12 and 13 in theFLAGS register.Inprotected modeandlong mode,it shows the I/O privilege level of the current program or task. The Current Privilege Level (CPL) (CPL0, CPL1, CPL2, CPL3) of the task or program must be less than or equal to the IOPL in order for the task or program to accessI/O ports.
The IOPL can be changed usingPOPF(D)andIRET(D)only when the current privilege level is Ring 0.
Besides IOPL, theI/O Port Permissionsin the TSS also take part in determining the ability of a task to access an I/O port.
Miscellaneous
editIn x86 systems, the x86 hardware virtualization (VT-xandSVM) is referred as "ring −1", theSystem Management Modeis referred as "ring −2", theIntel Management EngineandAMD Platform Security Processorare sometimes referred as "ring −3".[21]
Use of hardware features
editMany CPU hardware architectures provide far more flexibility than is exploited by theoperating systemsthat they normally run. Proper use of complex CPU modes requires very close cooperation between the operating system and the CPU, and thus tends to tie the OS to the CPU architecture. When the OS and the CPU are specifically designed for each other, this is not a problem (although some hardware features may still be left unexploited), but when the OS is designed to be compatible with multiple, different CPU architectures, a large part of the CPU mode features may be ignored by the OS. For example, the reason Windows uses only two levels (ring 0 and ring 3) is that some hardware architectures that were supported in the past (such asPowerPCorMIPS) implemented only two privilege levels.[7]
Multicswas an operating system designed specifically for a special CPU architecture (which in turn was designed specifically for Multics), and it took full advantage of the CPU modes available to it. However, it was an exception to the rule. Today, this high degree of interoperation between the OS and the hardware is not often cost-effective, despite the potential advantages for security and stability.
Ultimately, the purpose of distinct operating modes for the CPU is to provide hardware protection against accidental or deliberate corruption of the system environment (and corresponding breaches of system security) by software. Only "trusted" portions of system software are allowed to execute in the unrestricted environment of kernel mode, and then, in paradigmatic designs, only when absolutely necessary. All other software executes in one or more user modes. If a processor generates a fault or exception condition in a user mode, in most cases system stability is unaffected; if a processor generates a fault or exception condition in kernel mode, most operating systems will halt the system with an unrecoverable error. When a hierarchy of modes exists (ring-based security), faults and exceptions at one privilege level may destabilize only the higher-numbered privilege levels. Thus, a fault in Ring 0 (the kernel mode with the highest privilege) will crash the entire system, but a fault in Ring 2 will only affect Rings 3 and beyond and Ring 2 itself, at most.
Transitions between modes are at the discretion of the executingthreadwhen the transition is from a level of high privilege to one of low privilege (as from kernel to user modes), but transitions from lower to higher levels of privilege can take place only through secure, hardware-controlled "gates" that are traversed by executing special instructions or when external interrupts are received.
Microkerneloperating systems attempt to minimize the amount of code running in privileged mode, for purposes ofsecurityandelegance,but ultimately sacrificing performance.
See also
edit- Call gate (Intel)
- Memory segmentation
- Protected mode– available on x86-compatible 80286 CPUs and newer
- IOPL (CONFIG.SYS directive)– an OS/2 directive to run DLL code at ring 2 instead of at ring 3
- Segment descriptor
- Supervisor Call instruction
- System Management Mode(SMM)
- Principle of least privilege
Notes
editReferences
edit- ^Karger, Paul A.; Herbert, Andrew J. (1984).An Augmented Capability Architecture to Support Lattice Security and Traceability of Access.1984 IEEE Symposium on Security and Privacy. p. 2.doi:10.1109/SP.1984.10001.ISBN0-8186-0532-4.S2CID14788823.
- ^Binder, W. (2001). "Design and implementation of the J-SEAL2 mobile agent kernel".Proceedings 2001 Symposium on Applications and the Internet.pp. 35–42.doi:10.1109/SAINT.2001.905166.ISBN0-7695-0942-8.S2CID11066378.
- ^"Envisioning a Simplified Intel Architecture for the Future".Intel.Retrieved28 May2024.
- ^"A Hardware Architecture for Implementing Protection Rings".Communications of the ACM.15(3). March 1972.Retrieved27 September2012.
- ^"Multics Glossary - ring".Retrieved27 September2012.
- ^The Multics Virtual Memory, part 2(PDF).Honeywell Information Systems. June 1972. pp. 160–161.
- ^abRussinovich, Mark E.; David A. Solomon (2005).Microsoft Windows Internals(4 ed.). Microsoft Press. pp.16.ISBN978-0-7356-1917-3.
- ^Russinovich, Mark (2012).Windows Internals Part 1(6th ed.). Redmond, Washington: Microsoft Press. p. 17.ISBN978-0-7356-4873-9.
The reason Windows uses only two levels is that some hardware architectures that were supported in the past (such asCompaq AlphaandSilicon Graphics MIPS) implemented only two privilege levels.
- ^"Presentation Device Driver Reference for OS/2 – 5. Introduction to OS/2 Presentation Drivers".Archived fromthe originalon 15 June 2015.Retrieved13 June2015.
- ^ARM Architecture Reference Manual ARMv7-A and ARMv7-R edition.Arm Ltd.p. B1-1136.
- ^abArm Architecture Reference Manual Armv8, for A-profile architecture.Arm Ltd.
- ^"supervisor mode".FOLDOC.15 February 1995.
- ^abJochen Liedtke(December 1995)."On µ-Kernel Construction".Proc. 15th ACM Symposium on Operating System Principles (SOSP).
- ^Ousterhout, J. K.(1990).Why aren't operating systems getting faster as fast as hardware?.Usenix Summer Conference A. naheim, CA. pp. 247–256.
- ^Maurice Wilkes(April 1994)."Operating systems in a changing world".ACM SIGOPS Operating Systems Review.28(2): 9–21.doi:10.1145/198153.198154.ISSN0163-5980.S2CID254134.
- ^Gorine, Andrei; Krivolapov, Alexander (May 2008)."Kernel Mode Databases: A DBMS Technology For High-Performance Applications".Dr. Dobb's Journal.
- ^Intel® 64 and IA-32 Architectures Software Developer's Manual, Volume 3C(PDF).Intel Cooperation (published September 2016). 2016. pp. 1–3.
- ^Russinovich, Mark E.; Solomon, David A. (2005).Microsoft Windows Internals(4th ed.). Microsoft Press. p. 16.ISBN978-0-7356-1917-3.
- ^Sunil Mathur.Microprocessor 8086: Architecture, Programming and Interfacing(Eastern Economy ed.). PHI Learning.
- ^Anderson, Thomas; Dahlin, Michael (21 August 2014). "2.2".Operating Systems: Principles and Practice(2nd ed.). Recursive Books.ISBN978-0985673529.
- ^De Gelas, Johan."Hardware Virtualization: the Nuts and Bolts".AnandTech.Retrieved13 March2021.
- Intel 80386 Programmer's Reference
Further reading
edit- David T. Rogers (June 2003).A framework for dynamic subversion(PDF)(MSc).Naval Postgraduate School.hdl:10945/919.
- William J. Caelli (2002)."Relearning" Trusted Systems "in an Age of NIIP: Lessons from the Past for the Future".Archived fromthe original(PDF)on 20 April 2015.
- Haruna R. Isa; William R. Shockley; Cynthia E. Irvine (May 1999)."A Multi-threading Architecture for Multilevel Secure Transaction Processing"(PDF).Proceedings of the 1999 IEEE Symposium on Security and Privacy.Oakland, CA. pp. 166–179.hdl:10945/7198.
- Ivan Kelly (8 May 2006)."Porting MINIX to Xen"(PDF).Archived fromthe original(PDF)on 27 August 2006.
- Paul Barham; Boris Dragovic; Keir Fraser; Steven Hand; Tim Harris; Alex Ho; Rolf Neugebauer; Ian Pratt; Andrew Warfield (2003)."Xen and the Art of Virtualization"(PDF).
- Marcus Peinado; Yuqun Chen; Paul England; John Manferdelli."NGSCB: A Trusted Open System"(PDF).Archived fromthe original(PDF)on 4 March 2005.
- Michael D. Schroeder;Jerome H. Saltzer(1972)."A Hardware Architecture for Implementing Protection Rings".
- "Intel Architecture Software Developer's Manual Volume 3: System Programming (Order Number 243192)"(PDF).Chapter 4 "Protection"; section 4.5 "Privilege levels". Archived fromthe original(PDF)on 19 February 2009.
- Tzi-cker Chiueh; Ganesh Venkitachalam; Prashant Pradhan (December 1999). "Integrating segmentation and paging protection for safe, efficient and transparent software extensions".Proceedings of the seventeenth ACM symposium on Operating systems principles.Section 3: Protection hardware features in Intel X86 architecture; subsection 3.1 Protection checks.doi:10.1145/319151.319161.ISBN1581131402.S2CID9456119.
- Takahiro Shinagawa; Kenji Kono; Takashi Masuda (17 May 2000)."Exploiting Segmentation Mechanism for Protecting Against Malicious Mobile Code"(PDF).Chapter 3 Implementation; section 3.2.1 Ring Protection. Archived fromthe original(PDF)on 10 August 2017.Retrieved2 April2018.
- Boebert, William Earl; R. Kain (1985).A Practical Alternative to Hierarchical Integrity Policies.8th National Computer Security Conference.
- Gorine, Andrei; Krivolapov, Alexander (May 2008)."Kernel Mode Databases: A DBMS technology for high-performance applications".Dr. Dobb's Journal.