A20 line
TheA20,oraddress line 20,is one of theelectricallines that make up thesystem busof anx86-based computer system. The A20 line in particular is used to transmit the 21st bit on theaddress bus.
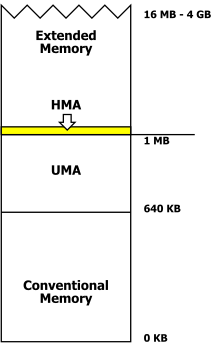
A microprocessor typically has a number ofaddress linesequal to the base-twologarithmof the number ofwordsin its physicaladdress space.For example, a processor with 4 GB ofbyte-addressablephysical space requires 32 lines (log2(4 GB) = log2(232B) = 32), which are named A0 through A31. The lines are named after the zero-based number of the bit in the address that they are transmitting. Theleast significant bitis first and is therefore numbered bit 0 and signaled on line A0. A20 transmits bit 20 (the 21st bit) and becomes active once addresses reach 1 MB, or 220.
Overview[edit]
TheIntel 8086,Intel 8088,andIntel 80186processors had 20 address lines, numbered A0 to A19; with these, the processor can access 220bytes, or 1 MB. Internal address registers of such processors only had 16 bits. To access a 20-bit address space, an external memory reference was made up of a 16-bitoffsetaddress added to a 16-bitsegmentnumber, shifted 4 bits to the left so as to produce a 20-bit physical address. The resulting address is equal tosegment× 16 +offset.[1]There are many combinations of segment and offset that produce the same 20-bit physical address. Therefore, there were various ways to address the same byte in memory.[2]For example, here are four of the 4096 different segment:offset combinations, all referencing the byte whose physical address is 0x000FFFFF (the last byte in 1 MB-memory space):
- F000:FFFF
- FFFF:000F
- F555:AAAF
- F800:7FFF
Referenced the last way, an increase of one in the offset yields F800:8000, which is a proper address for the processor, but since it translates to the physical address 0x00100000 (the first byte over 1 MB), the processor would need another address line for actual access to that byte. Since there is no such line on the 8086 line of processors, the 21st bit above, while set, gets dropped, causing the address F800:8000 to "wrap around"[1]and to actually point to the physical address 0x00000000.
WhenIBMdesigned theIBM PC AT(1984) machine, it decided to use the new higher-performanceIntel 80286microprocessor. The 80286 could address up to 16 MB of system memory inprotected mode.However, the CPU was supposed to emulate an 8086's behavior inreal mode,its startup mode, so that it could run operating systems and programs that were not written for protected mode. The 80286 did not force the A20 line to zero in real mode, however. Therefore, the combination F800:8000 would no longer point to the physical address 0x00000000, but to the address 0x00100000. As a result, programs relying on the address wrap around would no longer work. To remain compatible with such programs, IBM decided to correct the problem on themotherboard.
That was accomplished by inserting alogic gateon the A20 line between the processor and system bus, which got namedGate-A20.Gate-A20 can be enabled or disabled by software to allow or prevent the address bus from receiving a signal from A20. It is set to non-passing for the execution of older programs that rely on the wrap-around. At boot time, theBIOSfirst enables Gate-A20 when it counts and tests all of the system memory, and then disables it before transferring control to the operating system.
Originally, the logic gate was a gate connected to theIntel 8042keyboard controller.[1]Controlling it was a relatively slow process. Other methods have since been added to allow more efficient multitasking of programs that require this wrap-around with programs that access all of the system memory. There are multiple methods to control the A20 line.[3]
Disconnecting A20 would not wrapallmemory accesses above 1 MB, just those in the 1–2 MB, 3–4 MB, 5–6 MB, etc. ranges.Real-modesoftware cared only about the area slightly above 1 MB, so the Gate-A20 line was enough.
Enabling the Gate-A20 line is one of the first steps that aprotected-modex86operating systemdoes in the bootup process, often before control has been passed to the kernel from thebootstrap(in the case of Linux, for example).
Virtual 8086 mode,introduced with theIntel 80386,allows the A20 wrap-around to be simulated by using thevirtual memoryfacilities of the processor; physical memory may be mapped to multiple virtual addresses. Thus, the memory mapped at the first megabyte of virtual memory may be mapped again in the second megabyte of virtual memory. The operating system may intercept changes to Gate A20 and make corresponding changes to the virtual-memory address space, which also makes irrelevant the efficiency of Gate-A20 line toggling.
A20 gate[edit]
Controlling the A20 line was an important feature at one stage in the growth of the IBM PC architecture, as it added access to an additional 65,520 bytes (64 KB − 16 bytes) of memory inreal mode,without significant software changes.
In what was arguably a "hack", the A20 gate was originally part of the keyboard controller on the motherboard, which could open or close it depending on what behavior was desired.[4]
In order to keep full compatibility with theIntel 8086,the A20 gate was still present in Intel CPUs until 2008.[5]As the gate was initially closed right after boot,protected-modeoperating systems typically opened the A20 gate early during the boot process to never close it again. Such operating systems had no compatibility reasons for keeping it closed, and they gained access to the full range of physical addresses available by opening it.
TheIntel 80486andPentiumadded a special pin namedA20M#,which when asserted low forces bit 20 of the physical address to be zero for all on-chip cache- or external-memory accesses. It was necessary, since the 80486 introduced an on-chip cache and so masking this bit in external logic was no longer possible. Software still needs to manipulate the gate and must still deal with external peripherals (thechipset) for that.[6]
The PC System Design GuidePC 2001removes compatibility for the A20 line: "If A20M# generation logic is still present in the system, this logic must be terminated such that software writes to I/O port 92, bit 1, do not result in A20M# being asserted to the processor."[7]
Support for the A20 gate was changed in theNehalem microarchitecture(some sources incorrectly claim that A20 support was removed). Rather than the CPU having a dedicated A20M# pin that receives the signal whether or not to mask the A20 bit, it has been virtualized so that the information is sent from the peripheral hardware to the CPU using special bus cycles.[citation needed]From a software point of view, the mechanism works exactly as before, and an operating system must still program external hardware (which in-turn sends the aforementioned bus cycles to the CPU) to disable the A20 masking.[citation needed]
Intel no longer supports the A20 gate, starting withHaswell.Page 271 of the Intel System Programmers Manual Vol. 3A from June 2013 states: "The functionality of A20M# is used primarily by older operating systems and not used by modern operating systems. On newer Intel 64 processors, A20M# may be absent."[8]
A20 handler[edit]
TheA20 handlerisIBM PCmemory managersoftware that controls access to thehigh memory area(HMA).Extended-memorymanagers usually provide this functionality. A20 handlers are named after the 21st address line of the microprocessor, the A20 line.
InDOS,HMA managers such asHIMEM.SYShave the "extra task" of managing A20. HIMEM.SYS provided anAPIfor opening/closing A20. DOS itself could use the area for some of its storage needs, thereby freeing up more conventional memory for programs. That functionality was enabled by theDOS=HIGHorHIDOS=ONdirectives in theCONFIG.SYSconfiguration file.
Affected programs[edit]
Since 1980, the address wrap was internally used by86-DOSandMS-DOSto implement the DOS CALL 5 entry point at offset +5 to +9 (which emulates theCP/M-80-styleCALL 5BDOSAPIentry point at offset +5 to +7) in theProgram Segment Prefix(PSP) (which partially resembles CP/M-80'szero page).[9][10]This was, in particular, utilized by programsmachine-translatedfrom CP/M-80 throughassembly language translators[9]likeSeattle Computer Products'TRANS86.[11]The CALL 5 handler this entry point refers to resides at the machine's physical address 0x000000C0 (thereby overlapping the four bytes of theinterrupt service routineentry point reserved for INT 30h and the first byte of INT 31h in the x86real modeinterrupt vector table).[12][13][14]However, by the design of CP/M-80, which loaded the operating system immediately above the memory available for the application program to run in, the8080/Z8016-bit target address stored at offset +6 to +7 in the zero page could deliberately also be interpreted as the size of the first memory segment.[9]In order to emulate this in DOS with its 8086 segment:offset addressing scheme, the far call entry point's 16-bit offset had to match this segment size (i.e. 0xFEF0), which is stored at offset +6 to +7 in the PSP, overlapping parts of the CALL 5.[13][14]The only way to reconcile these requirements was to choose a segment value that, when added to 0xFEF0, results in an address of 0x001000C0, which, on an 8086, wraps around to 0x000000C0.[15][12][14]
A20 had to be disabled for the wraparound to occur and DOS programs using this interface to work. Newer DOS versions which can relocate parts of themselves into the HMA, typically craft a copy of the entry point at FFFF:00D0 in the HMA (which again resolves to physical 0x001000C0), so that the interface can work without regard to the state of A20.[14][16]
One program known to use the CALL 5 interface is the DOS version of theSmall-Ccompiler.[17]Also, the SPELL utility in Microsoft'sWord 3.0(1987) is one of the programs depending on the CALL 5 interface to be set up correspondingly.[18]Sun Microsystems'PC-NFS(1993) requires the CALL 5 fix-up as well.[16]
Also, to save program space,[1]a trick was used by someBIOSand DOS programmers, for example, to have one segment that has access to program data (such as from F800:0000 to F800:7FFF, pointing to the physical addresses 0x000F8000–0x000FFFFF), as well as the I/O data (such as the keyboard buffer) that was located in the first memory segment (with addresses F800:8000 to F800:FFFF pointing to the physical addresses 0x00000000 to 0x00007FFF).
This trick works for as long as the code isn't executed inlow memory,the first 64 KB of RAM, a condition that was always true in older DOS versions without load-high capabilities.
With the DOS kernel relocated into higher memory areas, low memory increasingly became available for programs, causing those depending on the wraparound to fail.[19]The executable loaders in newer versions of DOS attempt to detect some common types of affected programs and either patch them on-the-fly to function also in low memory[20]or load them above the first 64 KB before passing execution on to them.[20]For programs, which are not detected automatically,LOADFIX[21]orMEMMAX-L[21]can be used to force programs to be loaded above the first 64 KB.
The trick was utilized byIBM/Microsoft Pascalitself as well as by programs compiled with it,[22][23][10][17]including Microsoft'sMASM.[17]Other commonly used development utilities using this wereexecutable compressorslike Realia'sSpacemaker[20](written byRobert B. K. Dewarin 1982 and used to compress early versions of theNorton Utilities[24][25][26][27]) and Microsoft'sEXEPACK[19][20][1][28][17](written byReuben Bormanin 1985) as well as the equivalent /E[XEPACK] option in Microsoft's LINK 3.02 and higher.[19][1][28][26]Programs processed with EXEPACK would display a "Packed file is corrupt" error message.[1][20][28]
Various third-party utilities exist to modify compressed executables either replacing the problematic uncompression routine(s) through restubbing, or attempting to expand and restore the original file.
ModernLegacy BIOSboot loaders (such asGNU GRUB) use the A20 line.[3]UEFI boot loaders use 32-bitprotected modeor 64-bitlong mode.
See also[edit]
- Bug compatibility
- Computer storage
- High memory area(HMA)
- LOADFIX (CONFIG.SYS directive)(PTS-DOS)
- Incomplete address decoding
- Boot loaders
References[edit]
- ^abcdefgPaul, Matthias R. (2002-02-02)."Treiber dynamisch nachladen (Intra-Segment-Offset-Relokation zum Laden von TSRs in die HMA)"[Loading drivers dynamically (Intra-segment offset relocation to load TSRs into the HMA)] (in German).Newsgroup:de.comp.os.msdos.Archivedfrom the original on 2017-09-09.Retrieved2017-07-02.(NB. Gives a comprehensive overview on the history and "nature" of theHMAand the non-obvious design constraints to be observed when developing resident system extensions to be loaded into the HMA, some of which are caused by the A20 gate. It also describes how to address these issues usingstubs,backdoors, andintra-segment offset relocation,a method used byDR-DOSdrivers capable of relocating into the HMA and similar to a (more sophisticated) method used as the basis for thedynamic dead code eliminationin the author's FreeKEYB driver.)
- ^Paul, Matthias R. (2002-04-11)."Re: [fd-dev] ANNOUNCE: CuteMouse 2.0 alpha 1".freedos-dev.Archivedfrom the original on 2020-02-21.Retrieved2020-02-21.
- ^ab"A20 Line".OSDev Wiki.2021-07-19.Archivedfrom the original on 2021-11-30.Retrieved2021-07-19.
- ^Shanley, Tom; Anderson, Don (1995). Swindle, John (ed.).ISA System Architecture(3 ed.). Mindshare, Inc. /Addison-Wesley Publishing Company.pp.79–80.ISBN0-201-40996-8.ISBN978-0-201-40996-3.[1]
- ^"Envisioning a Simplified Intel Architecture for the Future".intel.com.Intel.Retrieved2023-05-22.
- ^Shanley, Tom (1996).Protected mode software architecture.Taylor & Francis.p. 60.ISBN0-201-55447-X.
- ^"Chapter 3 PC System".PC 2001 System Design Guide(PDF).Intel Corporation and Microsoft Corporation. p. 52.Retrieved2023-06-03.
SYS–0047. A20M# is always de-asserted (pulled high) at the processor
- ^Intel System Programmers Manual Vol. 3A from June 2013.
- ^abc86-DOS - Disk Operating System for the 8086 - Programmer's Manual(PDF).Version 0.3 (Preliminary ed.). Seattle, Washington, USA:Seattle Computer Products, Inc.1980. pp. 7, 17. Archived fromthe original(PDF)on 2019-06-23.Retrieved2011-09-13.
[…] This form is provided to simplifytranslation of 8080/Z80 programs into 8086 code,and is not recommended for new programs. […] Memory size. This is the number of bytes available in the program segment. […]
(41 pages) - ^abLetwin, James (1985-04-10)."Method and operating system for executing programs in a multi-mode microprocessor".Microsoft.US06722052, US4779187A. Archived from the original on 2018-09-23.Retrieved2018-09-23.
[…] Some programs written for the 8086 rely on [address wrap-around] to run properly. Unfortunately, memory locations extend above 1 megabyte in the real mode of the 80286 and are not wrapped to low memory locations. Consequently, programs including those written inMicroSoft PASCALand programs which use the "Call 5" feature of MS-DOS will fail on the standard 80286 system. […] For example, no PASCAL programs are loaded intomemory below 64K,and a special instruction is placed in the lower memory locations above 1 megabyte–for example, address 100000h or 100010h. […]
{{cite web}}:CS1 maint: bot: original URL status unknown (link) - ^Taylor, Roger; Lemmons, Phil (June 1982)."Upward migration - Part 1: Translators - Using translation programs to move CP/M-86 programs to CP/M and MS-DOS"[Using translation programs to move CP/M programs to CP/M-86 and MS-DOS](PDF).BYTE.Vol. 7, no. 6.BYTE Publications Inc.pp. 321–322, 324, 326, 328, 330, 332, 334, 336, 338, 340, 342, 344 [342, 344].ISSN0360-5280.CODENBYTEDJ.Archived(PDF)from the original on 2020-01-16.Retrieved2020-01-15.
[…] Gaining Access toCP/M-86[…] Gaining access to CP/M-86 requires placing the function code in the CL register, placing the byte parameter in the DL register or placing the word parameter in the DX register, placing the data segment in the DS register (the data segment is usually not changed for a converted program), and executing a software interrupt,INT #224.The result is returned in the AL register if it is a byte value; if the result is a word value, it is returned in both the AX and BX registers. Double-word values are returned with the offset in the BX registers and the segment in the ES register. Conversion of programs fromCP/M-80to CP/M-86, then, requires replacing the call to location 5 with the software interrupt INT #224. Another necessary change involves thewarm boot.Under CP/M-80, the warm boot may be accessed by a system call with a function code of 0 for a jump to location 0. CP/M-86, however, does not support the jump to location 0. As a result, you must change this program exit in the translated program if the program is to run correctly. Provided that the call to location 5 is replaced with INT #224, that the warm boot change is made, and that the registers are mapped correctly, there should be little problem in getting the translated program to access the CP/M-86 system functions. […] Gaining Access toMS-DOS[…] Although MS-DOS has a "preferred" mechanism through a soft-ware interrupt,INT #33,for accessing the system, an additional mechanism is provided for "preexisting" programs that is compatible with CP/M-80 calling conventions, at least for functions in the range of 0-36. As far as system calls within the allowed function range are concerned, the programmer doesn't have to do anything to translated programs to get them to run under MS-DOS other than to correctly map the registers. MS-DOS also supports the warm boot function of CP/M-80. A jump to location 0 under MS-DOS executes a software interrupt,INT #32,which is functionally a program end and the normal way to exit from a program. […]
[2][3][4][5][6][7][8][9][10][11][12][13][14][15](13 pages) - ^abSchäpers, Arne (1991). "Kapitel 5: EXEC im Detail - Program Segment Prefix (PSP)".DOS 5 für Programmierer: Die endgültige Referenz(in German) (1 ed.).Addison Wesley (Deutschland) GmbH.pp. 148–151, 971–972 [149, 971–972].ISBN3-89319-350-2.(1123+v pages, foldout, 5.25 "-floppy)
- ^ab"Format of Program Segment Prefix (PSP)".INTER61.2000.Archivedfrom the original on 2020-02-17.Retrieved2019-12-19.
- ^abcdNecasek, Michal (2011-09-13)."Who needs the address wraparound, anyway?".OS/2 Museum.Archivedfrom the original on 2020-02-19.Retrieved2020-02-19.
[…]86-DOS,and hencePC DOS/MS-DOS,used a clever trick. The byte at offset 5 of thePSPcontained a far call opcode (9Ah); the word at offset 6 of the PSP contained the appropriate value to indicate program segment size, and also the offset part of the far call. The word at offset 8, which served as the segment part of the far call, was crafted such that when combined with the offset, it would wrap around (a well understood feature of the8086CPU) and point to address 0:C0h, which contains interrupt vector 30h. […] A problem with the compatibility interface occurs when the loaded program has in fact less than 64KB available. If that happens, the word at PSP offset 6 may not contain the correct value, but the CALL 5 interface will still work; the instruction at offset 5 will be CALL 0:C0h, making the reported program segment size C0h. It is unclear why DOS does that; it appears to be a bug in DOS 5.0 and later, as DOS 4.0 and earlier versions simply adjust the segment portion so that it wraps around to 0:C0h. That works as long as the program segment size is paragraph aligned, and it will be. […]
- ^Norton, Peter(1985).The Peter Norton Programmer's Guide to the IBM PC(Illustrated ed.).Microsoft Corporation.ISBN0-91484546-2.ISBN978-0-91484546-1.p. 263:
[…] By a process too bizarre and complicated to explain, the segmented address is set so that it serves two purposes. Not only does it point to the DOS function dispatcher, but the offset part also indicates how much of the code segment we can use (up to hex FFF0, 16 bytes short of 64K). The offset part of the address, the part we are interested in, is located at offset 6 within the PSP, following the instruction's op-code at offset 5. The upshot of this is that if DOS has less than 64K to give our programs, we can use this field to learn how many bytes are available — a technique that should work with most or all windowing and multitasking systems. […]
(426 pages) - ^ab"Caldera OpenDOS Machine Readable Source Kit (M.R.S) 7.01".Caldera, Inc.1997-05-01 [1997-04-16].Archivedfrom the original on 2021-08-07.Retrieved2022-01-02.
[…] BIOSINIT.A86 1.40 93/11/11 12:25:29 […]VDISKheader changes […] BIOSINIT.A86 1.39 93/11/08 23:19:22 […] SetupHMA does CALL5 initialisation […] now fixup JMPF inhi-memoryfor CALL5 link forPC-NFS[…]
[16](NB.OpenDOS 7.01M.R.S.: IBMBIO\BIOSINIT.A86 SetupHMA ) - ^abcdNecasek, Michal (2018-03-16)."The A20-Gate: It Wasn't WordStar".OS/2 Museum.Archivedfrom the original on 2018-09-23.Retrieved2018-09-23.
- ^Parsons, Jeff (2018-05-27) [1987-12-01, 1987-08-02]."Somebody Put a SPELL On Me".PCjs.Archivedfrom the original on 2019-01-29.Retrieved2019-04-21.
- ^abcSchulman, Andrew;Brown, Ralf D.;Maxey, David; Michels, Raymond J.; Kyle, Jim (1994) [November 1993]. Williams, Andrew (ed.).Undocumented DOS: A programmer's guide to reserved MS-DOS functions and data structures - expanded to include MS-DOS 6, Novell DOS and Windows 3.1.The Andrew Schulman Programming Series (1st printing, 2nd ed.). Reading, Massachusetts, USA:Addison Wesley Publishing Company.pp.349–350.ISBN0-201-63287-X.ISBN978-0-201-63287-3.
[…] Leaving the A20 line enabled causes problems with programs that expect wraparound to occur […] One such program was the unpacking routineMicrosoft's own linker originally included with any file that had beenEXEPACKedto reduce its size! According to Phillip Gardner, author of the shareware DOSMAXUMBmaintenance utility and a veteran in the DOS disassembly area, the notorious "Packed File Corrupt" error message than began appearing everywhere shortly after the introduction of DOS 5.0 is directly due to the fact that the A20 line is enabled, and the original unpacking routine depended on the segment wraparound effect to properly expand the compressed files. […]
(xviii+856+vi pages, 3.5 "-floppy[17]) Errata:[18][19](NB. On page 350, the book has a detailed description of the inner workings of the problematic EXEPACK uncompression routine.) - ^abcdePaul, Matthias R. (2002-10-07) [2000]."Re: masm.com (PSP) related trouble".Newsgroup:alt.lang.asm.Archivedfrom the original on 2017-09-03.Retrieved2017-09-03.
[…]DR Concurrent DOS 386(since 1988-07-08) will loadEXEPACKedprograms above the 64K mark, that is, outside "lowest memory",by extending the memory block containing the program's environment […]DR DOS 5.0+ always loads.EXE-format programs with no fixups, and (since 1990-05-25) also.COM-format programs compressed withSpaceMaker- and therefore starting with 9Ch 55h (PUSHF/PUSH BP) - above the 64K mark to avoid the EXEPACK wrap around bug. It does this by extending the memory block containing the program's environment, since 1989-12-14 it will even allocate multiple fillers when necessary. This environment expansion code is disabled if the name of the parent program as stored in the MCB is "WIN" to improve performance whenWIN.COMstarts KERNEL.EXE (0 relocation items). […] theMS-DOS/PC DOS 5.0+[…] kernel scans for a variety of code sequences in.EXE format executables and applies patches for various versions of EXEPACKed files in order to let them run in lowest memory (when DOS is in theHMA), that is, a load segment < 64 Kb. Otherwise they would display "Packed file corrupt". The code checks that the code's entry point […] is not < 0002h […] and then reads the WORD immediately preceding the entry point […] If this WORD reads 5242h ( "RB" ), the file is assumed to be EXEPACKed. The code then looks for one of several combinations of code sequences at offsets from this "RB" signature. […] the MS-DOS 5.0+[…] kernel scans for an unknown class of.COMexecutables. If their signatures are found in the file, the A20 countdown variable at offset 18h in the disk buffer info table (see Table "DOS 5.0-6.0 disk buffer info" ) will be set to 10, which will cause A20 to be disabled after INT 21h calls for this count of INT 21h calls to follow. Presumably this class of programs requires A20 to be disabled for some time after it begins execution. (Similar actions occur on entry into INT 21h/AH=25h and AH=49h.) […]
- ^abPaul, Matthias R. (1997-07-30) [1996-06-18, 1994-05-01]. "V.4. Bessere Speicherausnutzung mit selbsthochladenden Programmen".NWDOS-TIPs — Tips & Tricks rund um Novell DOS 7, mit Blick auf undokumentierte Details, Bugs und Workarounds.Release 157 (in German) (3 ed.).Archivedfrom the original on 2016-11-04.Retrieved2014-08-06.
{{cite book}}:|work=ignored (help)(NB. The provided link points to a HTML-converted version of theNWDOSTIP.TXT,which is part of theMPDOSTIP.ZIPcollection.)[20] - ^Pascal Compiler(PDF).Personal Computer Computer Language Series (1 ed.).International Business Machines Corporation.August 1981.Archived(PDF)from the original on 2020-05-29.Retrieved2018-09-23.
- ^"NAME ENTX - Microsoft MS-DOS Computer Pascal runtime system control".Version 1.00.Microsoft Corp.1981.Archivedfrom the original on 2020-02-23.Retrieved2020-02-23.
[…] DX is final DS (may be negative) […] final DS value (may be negative) […]
- ^"Expert Report of Robert B. K. Dewar In Response To The Report Of Kenneth D. Crews".Cambridge University Press et al v. Patton et al, Filing 124, Supplemental Initial Disclosures by Cambridge University Press, Oxford University Press, Inc., Sage Publications, Inc. - Cambridge University Press, Oxfort University Press, Inc., and Sage Publications, Inc. v. Mark P. Becker, Georgia State University President, et al, Civil Action No. 1:08-CV-1425-ODE(Court document). United States District Court For The Northern District Of Georgia, Atlanta Division. p. 18. Exhibit A.Archivedfrom the original on 2018-05-01.Retrieved2019-04-23.
[…]SPACEMAKERand TERMULATOR, commodity software for IBM PC (PC DOSfile compression utility andVT-100emulator), being marketed by Realia, Inc.R.B.K. Dewar(1982-1983), 8088 assembly language, 8,000 lines […]
- ^Realia, Inc. (January 1983)."If you use DOS, you need this program".PC Magazine(advertisement).2(9).Ziff-Davis Publishing:417.Archivedfrom the original on 2019-04-22.Retrieved2019-04-22.
- ^abDewar, Robert Berriedale Keith(1984-03-13)."DOS 3.1 ASMB (Another Silly Microsoft Bug)".[email protected].Archivedfrom the original on 2018-05-01.Retrieved2019-04-23.
[…] The /E option of the linker should generate an EXE file which is logically equivalent to the uncompressed EXE file. The current version […] results in AX being clobbered. AX on entry to an EXE file has a definite meaning (it indicates drive validity for the parameters), thus it should be passed through to the uncompressed image. Given this one very obvious violation of the interface rules, there may be others, I have not bothered to investigate further […] I did write theRealia SpaceMakerprogram which does a similar sort of thing to theEXEPACKoption (but needless to say does not have this particular […]
- ^Necasek, Michal (2018-04-30)."Realia SpaceMaker".OS/2 Museum.Archivedfrom the original on 2019-01-27.Retrieved2019-02-22.
- ^abcNecasek, Michal (2018-03-23)."EXEPACK and the A20-Gate".OS/2 Museum.Archivedfrom the original on 2018-11-13.Retrieved2019-04-20.
Further reading[edit]
- Brouwer, Andries Evert(2001)."A20 - a pain from the past".Archivedfrom the original on 2017-09-09.Retrieved2017-09-09.
- Collins, Robert R. (2001)."A20/Reset Anomalies".Archivedfrom the original on 2017-09-09.Retrieved2017-09-09.
- Necasek, Michal (2018-01-30) [2018-01-28, 2018-01-26]."WordStar Again".OS/2 Museum.Archivedfrom the original on 2019-07-28.Retrieved2019-07-28.
- Ingenoso, Tony (1998-12-20). "Chapter 13 - The A20 gate and the HMA".Making Code Work Better - How to minimize the size of 80x86 code and sometimes make it faster(e-book).Archivedfrom the original on 2019-11-18.Retrieved2019-11-18.
- Ludloff, Christian (2011)."x86 architecture legacy stuff: KBC, PS/2, and A20M#".sandpile.org.Archivedfrom the original on 2021-08-15.Retrieved2022-01-02.
