Error correction code
Incomputing,telecommunication,information theory,andcoding theory,forward error correction(FEC) orchannel coding[1][2][3]is a technique used forcontrolling errorsindata transmissionover unreliable or noisycommunication channels.
The central idea is that the sender encodes the message in aredundantway, most often by using anerror correction codeorerror correcting code(ECC).[4][5]The redundancy allows the receiver not only todetect errorsthat may occur anywhere in the message, but often to correct a limited number of errors. Therefore areverse channelto request re-transmission may not be needed. The cost is a fixed, higher forward channel bandwidth.
The American mathematicianRichard Hammingpioneered this field in the 1940s and invented the first error-correcting code in 1950: theHamming (7,4) code.[5]
FEC can be applied in situations where re-transmissions are costly or impossible, such as one-way communication links or when transmitting to multiple receivers inmulticast.
Long-latency connections also benefit; in the case of satellites orbiting distant planets, retransmission due to errors would create a delay of several hours. FEC is also widely used inmodemsand incellular networks.
FEC processing in a receiver may be applied to a digital bit stream or in the demodulation of a digitally modulated carrier. For the latter, FEC is an integral part of the initialanalog-to-digital conversionin the receiver. TheViterbi decoderimplements asoft-decision algorithmto demodulate digital data from an analog signal corrupted by noise. Many FEC decoders can also generate abit-error rate(BER) signal which can be used as feedback to fine-tune the analog receiving electronics.
FEC information is added tomass storage(magnetic, optical and solid state/flash based) devices to enable recovery of corrupted data, and is used asECCcomputer memoryon systems that require special provisions for reliability.
The maximum proportion of errors or missing bits that can be corrected is determined by the design of the ECC, so different forward error correcting codes are suitable for different conditions. In general, a stronger code induces more redundancy that needs to be transmitted using the available bandwidth, which reduces the effective bit-rate while improving the received effectivesignal-to-noise ratio.Thenoisy-channel coding theoremofClaude Shannoncan be used to compute the maximum achievable communication bandwidth for a given maximum acceptable error probability. This establishes bounds on the theoretical maximum information transfer rate of a channel with some given base noise level. However, the proof is not constructive, and hence gives no insight of how to build a capacity achieving code. After years of research, some advanced FEC systems likepolar code[3]come very close to the theoretical maximum given by the Shannon channel capacity under the hypothesis of an infinite length frame.
Method
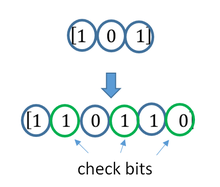
[edit]ECC is accomplished by addingredundancyto the transmitted information using an algorithm. A redundant bit may be a complicated function of many original information bits. The original information may or may not appear literally in the encoded output; codes that include the unmodified input in the output aresystematic,while those that do not arenon-systematic.
A simplistic example of ECC is to transmit each data bit 3 times, which is known as a (3,1)repetition code.Through a noisy channel, a receiver might see 8 versions of the output, see table below.
| Triplet received | Interpreted as |
|---|---|
| 000 | 0 (error-free) |
| 001 | 0 |
| 010 | 0 |
| 100 | 0 |
| 111 | 1 (error-free) |
| 110 | 1 |
| 101 | 1 |
| 011 | 1 |
This allows an error in any one of the three samples to be corrected by "majority vote", or "democratic voting". The correcting ability of this ECC is:
- Up to 1 bit of triplet in error, or
- up to 2 bits of triplet omitted (cases not shown in table).
Though simple to implement and widely used, thistriple modular redundancyis a relatively inefficient ECC. Better ECC codes typically examine the last several tens or even the last several hundreds of previously received bits to determine how to decode the current small handful of bits (typically in groups of 2 to 8 bits).
Averaging noise to reduce errors
[edit]ECC could be said to work by "averaging noise"; since each data bit affects many transmitted symbols, the corruption of some symbols by noise usually allows the original user data to be extracted from the other, uncorrupted received symbols that also depend on the same user data.
- Because of this "risk-pooling" effect, digital communication systems that use ECC tend to work well above a certain minimumsignal-to-noise ratioand not at all below it.
- Thisall-or-nothing tendency– thecliff effect– becomes more pronounced as stronger codes are used that more closely approach the theoreticalShannon limit.
- Interleaving ECC coded data can reduce the all or nothing properties of transmitted ECC codes when the channel errors tend to occur in bursts. However, this method has limits; it is best used on narrowband data.
Most telecommunication systems use a fixedchannel codedesigned to tolerate the expected worst-casebit error rate,and then fail to work at all if the bit error rate is ever worse. However, some systems adapt to the given channel error conditions: some instances ofhybrid automatic repeat-requestuse a fixed ECC method as long as the ECC can handle the error rate, then switch toARQwhen the error rate gets too high; adaptive modulation and codinguses a variety of ECC rates, adding more error-correction bits per packet when there are higher error rates in the channel, or taking them out when they are not needed.
Types
[edit]
The two main categories of ECC codes areblock codesandconvolutional codes.
- Block codes work on fixed-size blocks (packets) of bits or symbols of predetermined size. Practical block codes can generally be hard-decoded inpolynomial timeto their block length.
- Convolutional codes work on bit or symbol streams of arbitrary length. They are most often soft decoded with theViterbi algorithm,though other algorithms are sometimes used. Viterbi decoding allows asymptotically optimal decoding efficiency with increasing constraint length of the convolutional code, but at the expense ofexponentiallyincreasing complexity. A convolutional code that is terminated is also a 'block code' in that it encodes a block of input data, but the block size of a convolutional code is generally arbitrary, while block codes have a fixed size dictated by their algebraic characteristics. Types of termination for convolutional codes include "tail-biting" and "bit-flushing".
There are many types of block codes;Reed–Solomon codingis noteworthy for its widespread use incompact discs,DVDs,andhard disk drives.Other examples of classical block codes includeGolay,BCH,Multidimensional parity,andHamming codes.
Hamming ECC is commonly used to correctNAND flashmemory errors.[6] This provides single-bit error correction and 2-bit error detection. Hamming codes are only suitable for more reliablesingle-level cell(SLC) NAND. Densermulti-level cell(MLC) NAND may use multi-bit correcting ECC such as BCH or Reed–Solomon.[7][8]NOR Flash typically does not use any error correction.[7]
Classical block codes are usually decoded usinghard-decisionalgorithms,[9]which means that for every input and output signal a hard decision is made whether it corresponds to a one or a zero bit. In contrast, convolutional codes are typically decoded usingsoft-decisionalgorithms like the Viterbi, MAP orBCJRalgorithms, which process (discretized) analog signals, and which allow for much higher error-correction performance than hard-decision decoding.
Nearly all classical block codes apply the algebraic properties offinite fields.Hence classical block codes are often referred to as algebraic codes.
In contrast to classical block codes that often specify an error-detecting or error-correcting ability, many modern block codes such asLDPC codeslack such guarantees. Instead, modern codes are evaluated in terms of their bit error rates.
Mostforward error correctioncodes correct only bit-flips, but not bit-insertions or bit-deletions. In this setting, theHamming distanceis the appropriate way to measure thebit error rate. A few forward error correction codes are designed to correct bit-insertions and bit-deletions, such as Marker Codes and Watermark Codes. TheLevenshtein distanceis a more appropriate way to measure the bit error rate when using such codes. [10]
Code-rate and the tradeoff between reliability and data rate
[edit]The fundamental principle of ECC is to add redundant bits in order to help the decoder to find out the true message that was encoded by the transmitter. The code-rate of a given ECC system is defined as the ratio between the number of information bits and the total number of bits (i.e., information plus redundancy bits) in a given communication package. The code-rate is hence a real number. A low code-rate close to zero implies a strong code that uses many redundant bits to achieve a good performance, while a large code-rate close to 1 implies a weak code.
The redundant bits that protect the information have to be transferred using the same communication resources that they are trying to protect. This causes a fundamental tradeoff between reliability and data rate.[11]In one extreme, a strong code (with low code-rate) can induce an important increase in the receiver SNR (signal-to-noise-ratio) decreasing the bit error rate, at the cost of reducing the effective data rate. On the other extreme, not using any ECC (i.e., a code-rate equal to 1) uses the full channel for information transfer purposes, at the cost of leaving the bits without any additional protection.
One interesting question is the following: how efficient in terms of information transfer can an ECC be that has a negligible decoding error rate? This question was answered by Claude Shannon with his second theorem, which says that the channel capacity is the maximum bit rate achievable by any ECC whose error rate tends to zero:[12]His proof relies on Gaussian random coding, which is not suitable to real-world applications. The upper bound given by Shannon's work inspired a long journey in designing ECCs that can come close to the ultimate performance boundary. Various codes today can attain almost the Shannon limit. However, capacity achieving ECCs are usually extremely complex to implement.
The most popular ECCs have a trade-off between performance and computational complexity. Usually, their parameters give a range of possible code rates, which can be optimized depending on the scenario. Usually, this optimization is done in order to achieve a low decoding error probability while minimizing the impact to the data rate. Another criterion for optimizing the code rate is to balance low error rate and retransmissions number in order to the energy cost of the communication.[13]
Concatenated ECC codes for improved performance
[edit]Classical (algebraic) block codes and convolutional codes are frequently combined inconcatenatedcoding schemes in which a short constraint-length Viterbi-decoded convolutional code does most of the work and a block code (usually Reed–Solomon) with larger symbol size and block length "mops up" any errors made by the convolutional decoder. Single pass decoding with this family of error correction codes can yield very low error rates, but for long range transmission conditions (like deep space) iterative decoding is recommended.
Concatenated codes have been standard practice in satellite and deep space communications sinceVoyager 2first used the technique in its 1986 encounter withUranus.TheGalileocraft used iterative concatenated codes to compensate for the very high error rate conditions caused by having a failed antenna.
Low-density parity-check (LDPC)
[edit]Low-density parity-check(LDPC) codes are a class of highly efficient linear block codes made from many single parity check (SPC) codes. They can provide performance very close to thechannel capacity(the theoretical maximum) using an iterated soft-decision decoding approach, at linear time complexity in terms of their block length. Practical implementations rely heavily on decoding the constituent SPC codes in parallel.
LDPC codes were first introduced byRobert G. Gallagerin his PhD thesis in 1960, but due to the computational effort in implementing encoder and decoder and the introduction ofReed–Solomoncodes, they were mostly ignored until the 1990s.
LDPC codes are now used in many recent high-speed communication standards, such asDVB-S2(Digital Video Broadcasting – Satellite – Second Generation),WiMAX(IEEE 802.16estandard for microwave communications), High-Speed Wireless LAN (IEEE 802.11n),[14]10GBase-T Ethernet(802.3an) andG.hn/G.9960(ITU-T Standard for networking over power lines, phone lines and coaxial cable). Other LDPC codes are standardized for wireless communication standards within3GPPMBMS(seefountain codes).
Turbo codes
[edit]Turbo codingis an iterated soft-decoding scheme that combines two or more relatively simple convolutional codes and an interleaver to produce a block code that can perform to within a fraction of a decibel of theShannon limit.PredatingLDPC codesin terms of practical application, they now provide similar performance.
One of the earliest commercial applications of turbo coding was theCDMA2000 1x(TIA IS-2000) digital cellular technology developed byQualcommand sold byVerizon Wireless,Sprint,and other carriers. It is also used for the evolution of CDMA2000 1x specifically for Internet access,1xEV-DO(TIA IS-856). Like 1x, EV-DO was developed byQualcomm,and is sold byVerizon Wireless,Sprint,and other carriers (Verizon's marketing name for 1xEV-DO isBroadband Access,Sprint's consumer and business marketing names for 1xEV-DO arePower VisionandMobile Broadband,respectively).
Local decoding and testing of codes
[edit]Sometimes it is only necessary to decode single bits of the message, or to check whether a given signal is a codeword, and do so without looking at the entire signal. This can make sense in a streaming setting, where codewords are too large to be classically decoded fast enough and where only a few bits of the message are of interest for now. Also such codes have become an important tool incomputational complexity theory,e.g., for the design ofprobabilistically checkable proofs.
Locally decodable codesare error-correcting codes for which single bits of the message can be probabilistically recovered by only looking at a small (say constant) number of positions of a codeword, even after the codeword has been corrupted at some constant fraction of positions.Locally testable codesare error-correcting codes for which it can be checked probabilistically whether a signal is close to a codeword by only looking at a small number of positions of the signal.
Not all testing codes are locally decoding and testing of codes
Not all locally decodable codes (LDCs) are locally testable codes (LTCs)[15]neither locally correctable codes (LCCs),[16]q-query LCCs are bounded exponentially[17][18]while LDCs can havesubexponentiallengths.[19][20]
Interleaving
[edit]
Interleaving is frequently used in digital communication and storage systems to improve the performance of forward error correcting codes. Manycommunication channelsare not memoryless: errors typically occur inburstsrather than independently. If the number of errors within acode wordexceeds the error-correcting code's capability, it fails to recover the original code word. Interleaving alleviates this problem by shuffling source symbols across several code words, thereby creating a moreuniform distributionof errors.[21]Therefore, interleaving is widely used forburst error-correction.
The analysis of modern iterated codes, liketurbo codesandLDPC codes,typically assumes an independent distribution of errors.[22]Systems using LDPC codes therefore typically employ additional interleaving across the symbols within a code word.[23]
For turbo codes, an interleaver is an integral component and its proper design is crucial for good performance.[21][24]The iterative decoding algorithm works best when there are not short cycles in thefactor graphthat represents the decoder; the interleaver is chosen to avoid short cycles.
Interleaver designs include:
- rectangular (or uniform) interleavers (similar to the method using skip factors described above)
- convolutional interleavers
- random interleavers (where the interleaver is a known random permutation)
- S-random interleaver (where the interleaver is a known random permutation with the constraint that no input symbols within distance S appear within a distance of S in the output).[25]
- a contention-free quadraticpermutation polynomial(QPP).[26]An example of use is in the3GPP Long Term Evolutionmobile telecommunication standard.[27]
In multi-carriercommunication systems, interleaving across carriers may be employed to provide frequencydiversity,e.g., to mitigatefrequency-selective fadingor narrowband interference.[28]
Example
[edit]Transmission without interleaving:
Error-free message: aaaabbbbccccddddeeeeffffgggg Transmission with a burst error: aaaabbbbccc____deeeeffffgggg
Here, each group of the same letter represents a 4-bit one-bit error-correcting codeword. The codeword cccc is altered in one bit and can be corrected, but the codeword dddd is altered in three bits, so either it cannot be decoded at all or it might bedecoded incorrectly.
With interleaving:
Error-free code words: aaaabbbbccccddddeeeeffffgggg Interleaved: abcdefgabcdefgabcdefgabcdefg Transmission with a burst error: abcdefgabcd____bcdefgabcdefg Received code words after deinterleaving: aa_abbbbccccdddde_eef_ffg_gg
In each of the codewords "aaaa", "eeee", "ffff", and "gggg", only one bit is altered, so one-bit error-correcting code will decode everything correctly.
Transmission without interleaving:
Original transmitted sentence: ThisIsAnExampleOfInterleaving Received sentence with a burst error: ThisIs______pleOfInterleaving
The term "AnExample" ends up mostly unintelligible and difficult to correct.
With interleaving:
Transmitted sentence: ThisIsAnExampleOfInterleaving... Error-free transmission: TIEpfeaghsxlIrv.iAaenli.snmOten. Received sentence with a burst error: TIEpfe______Irv.iAaenli.snmOten. Received sentence after deinterleaving: T_isI_AnE_amp_eOfInterle_vin_...
No word is completely lost and the missing letters can be recovered with minimal guesswork.
Disadvantages of interleaving
[edit]Use of interleaving techniques increases total delay. This is because the entire interleaved block must be received before the packets can be decoded.[29]Also interleavers hide the structure of errors; without an interleaver, more advanced decoding algorithms can take advantage of the error structure and achieve more reliable communication than a simpler decoder combined with an interleaver[citation needed].An example of such an algorithm is based onneural network[30]structures.
Software for error-correcting codes
[edit]Simulating the behaviour of error-correcting codes (ECCs) in software is a common practice to design, validate and improve ECCs. The upcoming wireless 5G standard raises a new range of applications for the software ECCs: theCloud Radio Access Networks (C-RAN)in aSoftware-defined radio (SDR)context. The idea is to directly use software ECCs in the communications. For instance in the 5G, the software ECCs could be located in the cloud and the antennas connected to this computing resources: improving this way the flexibility of the communication network and eventually increasing the energy efficiency of the system.
In this context, there are various available Open-source software listed below (non exhaustive).
- AFF3CT(A Fast Forward Error Correction Toolbox): a full communication chain in C++ (many supported codes like Turbo, LDPC, Polar codes, etc.), very fast and specialized on channel coding (can be used as a program for simulations or as a library for the SDR).
- IT++:a C++ library of classes and functions for linear algebra, numerical optimization, signal processing, communications, and statistics.
- OpenAir:implementation (in C) of the 3GPP specifications concerning the Evolved Packet Core Networks.
List of error-correcting codes
[edit]| Distance | Code |
|---|---|
| 2 (single-error detecting) | Parity |
| 3 (single-error correcting) | Triple modular redundancy |
| 3 (single-error correcting) | perfect Hamming such asHamming(7,4) |
| 4 (SECDED) | Extended Hamming |
| 5 (double-error correcting) | |
| 6 (double-error correct-/triple error detect) | Nordstrom-Robinson code |
| 7 (three-error correcting) | perfectbinary Golay code |
| 8 (TECFED) | extendedbinary Golay code |
- AN codes
- Algebraic geometry code
- BCH code,which can be designed to correct any arbitrary number of errors per code block.
- Barker codeused for radar, telemetry, ultra sound, Wifi, DSSS mobile phone networks, GPS etc.
- Berger code
- Constant-weight code
- Convolutional code
- Expander codes
- Group codes
- Golay codes,of which theBinary Golay codeis of practical interest
- Goppa code,used in theMcEliece cryptosystem
- Hadamard code
- Hagelbarger code
- Hamming code
- Latin square based codefor non-white noise (prevalent for example in broadband over powerlines)
- Lexicographic code
- Linear Network Coding,a type of erasure correcting code across networks instead of point-to-point links
- Long code
- Low-density parity-check code,also known asGallager code,as the archetype forsparse graph codes
- LT code,which is a near-optimalrateless erasure correcting code (Fountain code)
- m of n codes
- Nordstrom-Robinson code,used in Geometry and Group Theory[31]
- Online code,a near-optimalrateless erasure correcting code
- Polar code (coding theory)
- Raptor code,a near-optimalrateless erasure correcting code
- Reed–Solomon error correction
- Reed–Muller code
- Repeat-accumulate code
- Repetition codes,such asTriple modular redundancy
- Spinal code, a rateless, nonlinear code based on pseudo-random hash functions[32]
- Tornado code,a near-optimalerasure correcting code,and the precursor toFountain codes
- Turbo code
- Walsh–Hadamard code
- Cyclic redundancy checks(CRCs) can correct 1-bit errors for messages at mostbits long for optimal generator polynomials of degree,seeMathematics of cyclic redundancy checks § Bitfilters
See also
[edit]- Burst error-correcting code
- Code rate
- Erasure codes
- Error detection and correction
- Error-correcting codes with feedback
- Linear code
- Quantum error correction
- Soft-decision decoder
References
[edit]- ^Charles Wang; Dean Sklar; Diana Johnson (Winter 2001–2002)."Forward Error-Correction Coding".Crosslink.3(1). The Aerospace Corporation. Archived fromthe originalon 14 March 2012.Retrieved5 March2006.
- ^Charles Wang; Dean Sklar; Diana Johnson (Winter 2001–2002)."Forward Error-Correction Coding".Crosslink.3(1). The Aerospace Corporation. Archived fromthe originalon 14 March 2012.Retrieved5 March2006.
How Forward Error-Correcting Codes Work]
- ^abMaunder, Robert (2016)."Overview of Channel Coding".
- ^Glover, Neal; Dudley, Trent (1990).Practical Error Correction Design For Engineers(Revision 1.1, 2nd ed.). CO, USA:Cirrus Logic.ISBN0-927239-00-0.
- ^abHamming, Richard Wesley(April 1950). "Error Detecting and Error Correcting Codes".Bell System Technical Journal.29(2). USA:AT&T:147–160.doi:10.1002/j.1538-7305.1950.tb00463.x.hdl:10945/46756.S2CID61141773.
- ^"Hamming codes for NAND flash memory devices"Archived21 August 2016 at theWayback Machine.EE Times-Asia. Apparently based on"Micron Technical Note TN-29-08: Hamming Codes for NAND Flash Memory Devices"Archived29 August 2017 at theWayback Machine.2005. Both say: "The Hamming algorithm is an industry-accepted method for error detection and correction in many SLC NAND flash-based applications."
- ^ab"What Types of ECC Should Be Used on Flash Memory?"(Application note).Spansion. 2011.
Both Reed–Solomon algorithm and BCH algorithm are common ECC choices for MLC NAND flash.... Hamming based block codes are the most commonly used ECC for SLC.... both Reed–Solomon and BCH are able to handle multiple errors and are widely used on MLC flash.
- ^Jim Cooke (August 2007)."The Inconvenient Truths of NAND Flash Memory"(PDF).p. 28.
For SLC, a code with a correction threshold of 1 is sufficient. t=4 required... for MLC.
- ^Baldi, M.; Chiaraluce, F. (2008)."A Simple Scheme for Belief Propagation Decoding of BCH and RS Codes in Multimedia Transmissions".International Journal of Digital Multimedia Broadcasting.2008:1–12.doi:10.1155/2008/957846.
- ^Shah, Gaurav; Molina, Andres; Blaze, Matt (2006)."Keyboards and covert channels".USENIX.Retrieved20 December2018.
- ^Tse, David; Viswanath, Pramod (2005),Fundamentals of Wireless Communication,Cambridge University Press,UK
- ^Shannon, C. E. (1948)."A mathematical theory of communication"(PDF).Bell System Technical Journal.27(3–4): 379–423 & 623–656.doi:10.1002/j.1538-7305.1948.tb01338.x.hdl:11858/00-001M-0000-002C-4314-2.
- ^Rosas, F.; Brante, G.; Souza, R. D.; Oberli, C. (2014)."Optimizing the code rate for achieving energy-efficient wireless communications".Proceedings of the IEEE Wireless Communications and Networking Conference (WCNC).pp. 775–780.doi:10.1109/WCNC.2014.6952166.ISBN978-1-4799-3083-8.
- ^IEEE Standard, section 20.3.11.6"802.11n-2009"Archived3 February 2013 at theWayback Machine,IEEE, 29 October 2009, accessed 21 March 2011.
- ^Kaufman, Tali;Viderman, Michael."Locally Testable vs. Locally Decodable Codes".
- ^Brubaker, Ben (9 January 2024)."'Magical' Error Correction Scheme Proved Inherently Inefficient ".Quanta Magazine.Retrieved9 January2024.
- ^Kothari, Pravesh K.; Manohar, Peter (2023). "An Exponential Lower Bound for Linear 3-Query Locally Correctable Codes".arXiv:2311.00558[cs.CC].
- ^Kerenidis, Iordanis; de Wolf, Ronald (9 June 2003)."Exponential lower bound for 2-query locally decodable codes via a quantum argument".Proceedings of the thirty-fifth annual ACM symposium on Theory of computing.ACM. pp. 106–115.arXiv:quant-ph/0208062.doi:10.1145/780542.780560.ISBN978-1-58113-674-6.S2CID10585919.
- ^Yekhanin, Sergey (February 2008)."Towards 3-query locally decodable codes of subexponential length".Journal of the ACM.55(1): 1–16.doi:10.1145/1326554.1326555.ISSN0004-5411.S2CID14617710.
- ^Efremenko, Klim (31 May 2009)."3-query locally decodable codes of subexponential length".Proceedings of the forty-first annual ACM symposium on Theory of computing.ACM. pp. 39–44.doi:10.1145/1536414.1536422.ISBN978-1-60558-506-2.S2CID263865692.
{{cite book}}:|journal=ignored (help) - ^abVucetic, B.; Yuan, J. (2000).Turbo codes: principles and applications.Springer Verlag.ISBN978-0-7923-7868-6.
- ^Luby, Michael;Mitzenmacher, M.; Shokrollahi, A.; Spielman, D.; Stemann, V. (1997). "Practical Loss-Resilient Codes".Proc. 29th Annual Association for Computing Machinery (ACM) Symposium on Theory of Computation.
- ^"Digital Video Broadcast (DVB); Second generation framing structure, channel coding and modulation systems for Broadcasting, Interactive Services, News Gathering and other satellite broadband applications (DVB-S2)".En 302 307(V1.2.1).ETSI.April 2009.
- ^Andrews, K. S.; Divsalar, D.; Dolinar, S.; Hamkins, J.; Jones, C. R.; Pollara, F. (November 2007). "The Development of Turbo and LDPC Codes for Deep-Space Applications".Proceedings of the IEEE.95(11): 2142–2156.doi:10.1109/JPROC.2007.905132.S2CID9289140.
- ^Dolinar, S.; Divsalar, D. (15 August 1995). "Weight Distributions for Turbo Codes Using Random and Nonrandom Permutations".TDA Progress Report.122:42–122.Bibcode:1995TDAPR.122...56D.CiteSeerX10.1.1.105.6640.
- ^Takeshita, Oscar (2006). "Permutation Polynomial Interleavers: An Algebraic-Geometric Perspective".IEEE Transactions on Information Theory.53(6): 2116–2132.arXiv:cs/0601048.Bibcode:2006cs........1048T.doi:10.1109/TIT.2007.896870.S2CID660.
- ^3GPP TS 36.212,version 8.8.0, page 14
- ^"Digital Video Broadcast (DVB); Frame structure, channel coding and modulation for a second generation digital terrestrial television broadcasting system (DVB-T2)".En 302 755(V1.1.1).ETSI.September 2009.
- ^Techie (3 June 2010)."Explaining Interleaving".W3 Techie Blog.Retrieved3 June2010.
- ^Krastanov, Stefan; Jiang, Liang (8 September 2017)."Deep Neural Network Probabilistic Decoder for Stabilizer Codes".Scientific Reports.7(1): 11003.arXiv:1705.09334.Bibcode:2017NatSR...711003K.doi:10.1038/s41598-017-11266-1.PMC5591216.PMID28887480.
- ^Nordstrom, A.W.; Robinson, J.P. (1967), "An optimum nonlinear code",Information and Control,11(5–6): 613–616,doi:10.1016/S0019-9958(67)90835-2
- ^Perry, Jonathan; Balakrishnan, Hari; Shah, Devavrat (2011)."Rateless Spinal Codes".Proceedings of the 10th ACM Workshop on Hot Topics in Networks.pp. 1–6.doi:10.1145/2070562.2070568.hdl:1721.1/79676.ISBN9781450310598.
Further reading
[edit]- MacWilliams, Florence Jessiem;Sloane, Neil James Alexander(2007) [1977]. Written at AT&T Shannon Labs, Florham Park, New Jersey, USA.The Theory of Error-Correcting Codes.North-Holland Mathematical Library. Vol. 16 (digital print of 12th impression, 1st ed.). Amsterdam / London / New York / Tokyo:North-Holland/Elsevier BV.ISBN978-0-444-85193-2.LCCN76-41296.(xxii+762+6 pages)
- Clark, Jr., George C.; Cain, J. Bibb (1981).Error-Correction Coding for Digital Communications.New York, USA:Plenum Press.ISBN0-306-40615-2.
- Arazi, Benjamin (1987). Swetman, Herb (ed.).A Commonsense Approach to the Theory of Error Correcting Codes.MIT PressSeries in Computer Systems. Vol. 10 (1 ed.). Cambridge, Massachusetts, USA / London, UK:Massachusetts Institute of Technology.ISBN0-262-01098-4.LCCN87-21889.(x+2+208+4 pages)
- Wicker, Stephen B. (1995).Error Control Systems for Digital Communication and Storage.Englewood Cliffs, New Jersey, USA:Prentice-Hall.ISBN0-13-200809-2.
- Wilson, Stephen G. (1996).Digital Modulation and Coding.Englewood Cliffs, New Jersey, USA:Prentice-Hall.ISBN0-13-210071-1.
- "Error Correction Code in Single Level Cell NAND Flash memories"2007-02-16
- "Error Correction Code in NAND Flash memories"2004-11-29
- Observations on Errors, Corrections, & Trust of Dependent Systems,by James Hamilton, 2012-02-26
- Sphere Packings, Lattices and Groups, By J. H. Conway, Neil James Alexander Sloane,Springer Science & Business Media,2013-03-09 – Mathematics – 682 pages.
External links
[edit]- Morelos-Zaragoza, Robert (2004)."The Correcting Codes (ECC) Page".Retrieved5 March2006.
- error correction zoo.Database of error correcting codes.
- lpdec: library for LP decoding and related things (Python)


