Advanced Encryption Standard
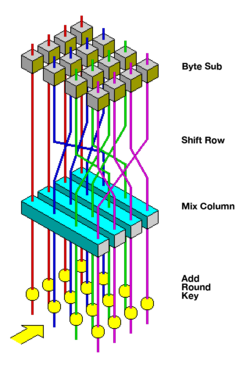 Visualization of the AES round function | |
| General | |
|---|---|
| Designers | Joan Daemen,Vincent Rijmen |
| First published | 1998 |
| Derived from | Square |
| Successors | Anubis,Grand Cru,Kalyna |
| Certification | AESwinner,CRYPTREC,NESSIE,NSA |
| Cipher detail | |
| Key sizes | 128, 192 or 256 bits[note 1] |
| Block sizes | 128 bits[note 2] |
| Structure | Substitution–permutation network |
| Rounds | 10, 12 or 14 (depending on key size) |
| Best publiccryptanalysis | |
| Attacks have been published that are computationally faster than a fullbrute-force attack,though none as of 2023 are computationally feasible.[1]
For AES-128, the key can be recovered with a computational complexity of 2126.1using thebiclique attack.For biclique attacks on AES-192 and AES-256, the computational complexities of 2189.7and 2254.4respectively apply.Related-key attackscan break AES-256 and AES-192 with complexities 299.5and 2176in both time and data, respectively.[2] Another attack was blogged[3]and released as apreprint[4]in 2009. This attack is against AES-256 that uses only two related keys and 239time to recover the complete 256-bit key of a 9-round version, or 245time for a 10-round version with a stronger type of related subkey attack, or 270time for an 11-round version. | |
TheAdvanced Encryption Standard(AES), also known by its original nameRijndael(Dutch pronunciation:[ˈrɛindaːl]),[5]is a specification for theencryptionof electronic data established by the U.S.National Institute of Standards and Technology(NIST) in 2001.[6]
AES is a variant of the Rijndaelblock cipher[5]developed by twoBelgiancryptographers,Joan DaemenandVincent Rijmen,who submitted a proposal[7]to NIST during theAES selection process.[8]Rijndael is a family of ciphers with different key and block sizes. For AES, NIST selected three members of the Rijndael family, each with a block size of 128 bits, but three different key lengths: 128, 192 and 256 bits.
AES has been adopted by theU.S. government.It supersedes theData Encryption Standard(DES),[9]which was published in 1977. The algorithm described by AES is asymmetric-key algorithm,meaning the same key is used for both encrypting and decrypting the data.
In the United States, AES was announced by the NIST as U.S.FIPSPUB 197 (FIPS 197) on November 26, 2001.[6]This announcement followed a five-year standardization process in which fifteen competing designs were presented and evaluated, before the Rijndael cipher was selected as the most suitable.[note 3]
AES is included in theISO/IEC18033-3standard. AES became effective as a U.S. federal government standard on May 26, 2002, after approval by U.S.Secretary of CommerceDonald Evans.AES is available in many different encryption packages, and is the first (and only) publicly accessiblecipherapproved by the U.S.National Security Agency(NSA) fortop secretinformation when used in an NSA approved cryptographic module.[note 4]
Definitive standards
[edit]The Advanced Encryption Standard (AES) is defined in each of:
Description of the ciphers
[edit]AES is based on a design principle known as asubstitution–permutation network,and is efficient in both software and hardware.[11]Unlike its predecessor DES, AES does not use aFeistel network.AES is a variant of Rijndael, with a fixedblock sizeof 128bits,and akey sizeof 128, 192, or 256 bits. By contrast, Rijndaelper seis specified with block and key sizes that may be any multiple of 32 bits, with a minimum of 128 and a maximum of 256 bits. Most AES calculations are done in a particularfinite field.
AES operates on a 4 × 4column-major orderarray of 16 bytesb0, b1, ..., b15termed thestate:[note 5]
The key size used for an AES cipher specifies the number of transformation rounds that convert the input, called theplaintext,into the final output, called theciphertext.The number of rounds are as follows:
- 10 rounds for 128-bit keys.
- 12 rounds for 192-bit keys.
- 14 rounds for 256-bit keys.
Each round consists of several processing steps, including one that depends on the encryption key itself. A set of reverse rounds are applied to transform ciphertext back into the original plaintext using the same encryption key.
High-level description of the algorithm
[edit]- KeyExpansion– round keys are derived from the cipher key using theAES key schedule.AES requires a separate 128-bit round key block for each round plus one more.
- Initial round key addition:
- AddRoundKey– each byte of the state is combined with a byte of the round key usingbitwise xor.
- 9, 11 or 13 rounds:
- SubBytes– anon-linearsubstitution step where each byte is replaced with another according to alookup table.
- ShiftRows– a transposition step where the last three rows of the state are shifted cyclically a certain number of steps.
- MixColumns– a linear mi xing operation which operates on the columns of the state, combining the four bytes in each column.
- AddRoundKey
- Final round (making 10, 12 or 14 rounds in total):
- SubBytes
- ShiftRows
- AddRoundKey
TheSubBytesstep
[edit]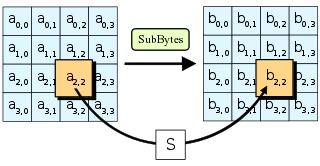
In theSubBytesstep, each bytein thestatearray is replaced with aSubByteusing an 8-bitsubstitution box.Before round 0, thestatearray is simply the plaintext/input. This operation provides the non-linearity in thecipher.The S-box used is derived from themultiplicative inverseoverGF(28),known to have good non-linearity properties. To avoid attacks based on simple algebraic properties, the S-box is constructed by combining the inverse function with an invertibleaffine transformation.The S-box is also chosen to avoid any fixed points (and so is aderangement), i.e.,,and also any opposite fixed points, i.e.,. While performing the decryption, theInvSubBytesstep (the inverse ofSubBytes) is used, which requires first taking the inverse of the affine transformation and then finding the multiplicative inverse.
TheShiftRowsstep
[edit]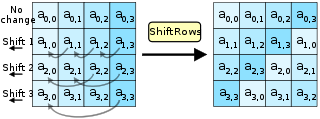
TheShiftRowsstep operates on the rows of the state; it cyclically shifts the bytes in each row by a certainoffset.For AES, the first row is left unchanged. Each byte of the second row is shifted one to the left. Similarly, the third and fourth rows are shifted by offsets of two and three respectively.[note 6]In this way, each column of the output state of theShiftRowsstep is composed of bytes from each column of the input state. The importance of this step is to avoid the columns being encrypted independently, in which case AES would degenerate into four independent block ciphers.
TheMixColumnsstep
[edit]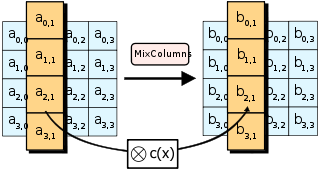
In theMixColumnsstep, the four bytes of each column of the state are combined using an invertiblelinear transformation.TheMixColumnsfunction takes four bytes as input and outputs four bytes, where each input byte affects all four output bytes. Together withShiftRows,MixColumnsprovidesdiffusionin the cipher.
During this operation, each column is transformed using a fixed matrix (matrix left-multiplied by column gives new value of column in the state):
Matrix multiplication is composed of multiplication and addition of the entries. Entries are bytes treated as coefficients of polynomial of order.Addition is simply XOR. Multiplication is modulo irreducible polynomial.If processed bit by bit, then, after shifting, a conditionalXORwith 1B16should be performed if the shifted value is larger than FF16(overflow must be corrected by subtraction of generating polynomial). These are special cases of the usual multiplication in.
In more general sense, each column is treated as a polynomial overand is then multiplied modulowith a fixed polynomial.The coefficients are displayed in theirhexadecimalequivalent of the binary representation of bit polynomials from.TheMixColumnsstep can also be viewed as a multiplication by the shown particularMDS matrixin thefinite field.This process is described further in the articleRijndael MixColumns.
TheAddRoundKey
[edit]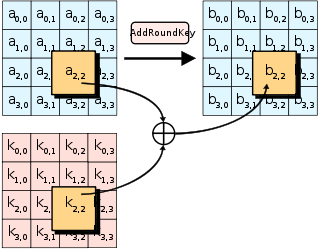
In theAddRoundKeystep, the subkey is combined with the state. For each round, a subkey is derived from the mainkeyusingRijndael's key schedule;each subkey is the same size as the state. The subkey is added by combining of the state with the corresponding byte of the subkey using bitwiseXOR.
Optimization of the cipher
[edit]On systems with 32-bit or larger words, it is possible to speed up execution of this cipher by combining theSubBytesandShiftRowssteps with theMixColumnsstep by transforming them into a sequence of table lookups. This requires four 256-entry 32-bit tables (together occupying 4096 bytes). A round can then be performed with 16 table lookup operations and 12 32-bit exclusive-or operations, followed by four 32-bit exclusive-or operations in theAddRoundKeystep.[12]Alternatively, the table lookup operation can be performed with a single 256-entry 32-bit table (occupying 1024 bytes) followed by circular rotation operations.
Using a byte-oriented approach, it is possible to combine theSubBytes,ShiftRows,andMixColumnssteps into a single round operation.[13]
Security
[edit]TheNational Security Agency(NSA) reviewed all the AES finalists, including Rijndael, and stated that all of them were secure enough for U.S. Government non-classified data. In June 2003, the U.S. Government announced that AES could be used to protectclassified information:
The design and strength of all key lengths of the AES algorithm (i.e., 128, 192 and 256) are sufficient to protect classified information up to the SECRET level. TOP SECRET information will require use of either the 192 or 256 key lengths. The implementation of AES in products intended to protect national security systems and/or information must be reviewed and certified by NSA prior to their acquisition and use.[14]
AES has 10 rounds for 128-bit keys, 12 rounds for 192-bit keys, and 14 rounds for 256-bit keys.
By 2006, the best known attacks were on 7 rounds for 128-bit keys, 8 rounds for 192-bit keys, and 9 rounds for 256-bit keys.[15]
Known attacks
[edit]For cryptographers, acryptographic"break" is anything faster than abrute-force attack— i.e., performing one trial decryption for each possible key in sequence.A break can thus include results that are infeasible with current technology. Despite being impractical, theoretical breaks can sometimes provide insight into vulnerability patterns. The largest successful publicly known brute-force attack against a widely implemented block-cipher encryption algorithm was against a 64-bitRC5key bydistributed.netin 2006.[16]
The key space increases by a factor of 2 for each additional bit of key length, and if every possible value of the key is equiprobable; this translates into a doubling of the average brute-force key search time with every additional bit of key length. This implies that the effort of a brute-force search increases exponentially with key length. Key length in itself does not imply security against attacks, since there are ciphers with very long keys that have been found to be vulnerable.
AES has a fairly simple algebraic framework.[17]In 2002, a theoretical attack, named the "XSL attack",was announced byNicolas CourtoisandJosef Pieprzyk,purporting to show a weakness in the AES algorithm, partially due to the low complexity of its nonlinear components.[18]Since then, other papers have shown that the attack, as originally presented, is unworkable; seeXSL attack on block ciphers.
During the AES selection process, developers of competing algorithms wrote of Rijndael's algorithm "we are concerned about [its] use... in security-critical applications."[19]In October 2000, however, at the end of the AES selection process,Bruce Schneier,a developer of the competing algorithmTwofish,wrote that while he thought successful academic attacks on Rijndael would be developed someday, he "did not believe that anyone will ever discover an attack that will allow someone to read Rijndael traffic."[20]
Until May 2009, the only successful published attacks against the full AES wereside-channel attackson some specific implementations. In 2009, a newrelated-key attackwas discovered that exploits the simplicity of AES's key schedule and has a complexity of 2119.In December 2009 it was improved to 299.5.[2]This is a follow-up to an attack discovered earlier in 2009 byAlex Biryukov,Dmitry Khovratovich,and Ivica Nikolić, with a complexity of 296for one out of every 235keys.[21]However, related-key attacks are not of concern in any properly designed cryptographic protocol, as a properly designed protocol (i.e., implementational software) will take care not to allow related keys, essentially byconstrainingan attacker's means of selecting keys for relatedness.
Another attack was blogged by Bruce Schneier[22] on July 30, 2009, and released as apreprint[23] on August 3, 2009. This new attack, by Alex Biryukov,Orr Dunkelman,Nathan Keller,Dmitry Khovratovich, andAdi Shamir,is against AES-256 that uses only two related keys and 239time to recover the complete 256-bit key of a 9-round version, or 245time for a 10-round version with a stronger type of related subkey attack, or 270time for an 11-round version. 256-bit AES uses 14 rounds, so these attacks are not effective against full AES.
The practicality of these attacks with stronger related keys has been criticized,[24]for instance, by the paper on chosen-key-relations-in-the-middle attacks on AES-128 authored by Vincent Rijmen in 2010.[25]
In November 2009, the firstknown-key distinguishing attackagainst a reduced 8-round version of AES-128 was released as a preprint.[26] This known-key distinguishing attack is an improvement of the rebound, or the start-from-the-middle attack, against AES-like permutations, which view two consecutive rounds of permutation as the application of a so-called Super-S-box. It works on the 8-round version of AES-128, with a time complexity of 248,and a memory complexity of 232.128-bit AES uses 10 rounds, so this attack is not effective against full AES-128.
The firstkey-recovery attackson full AES were by Andrey Bogdanov, Dmitry Khovratovich, and Christian Rechberger, and were published in 2011.[27]The attack is abiclique attackand is faster than brute force by a factor of about four. It requires 2126.2operations to recover an AES-128 key. For AES-192 and AES-256, 2190.2and 2254.6operations are needed, respectively. This result has been further improved to 2126.0for AES-128, 2189.9for AES-192 and 2254.3for AES-256,[28]which are the current best results in key recovery attack against AES.
This is a very small gain, as a 126-bit key (instead of 128 bits) would still take billions of years to brute force on current and foreseeable hardware. Also, the authors calculate the best attack using their technique on AES with a 128-bit key requires storing 288bits of data. That works out to about 38 trillion terabytes of data, which was more than all the data stored on all the computers on the planet in 2016.[29]A paper in 2015 later improved the space complexity to 256bits,[28]which is 9007 terabytes (while still keeping a time complexity of 2126.2).
According to theSnowden documents,the NSA is doing research on whether a cryptographic attack based ontau statisticmay help to break AES.[30]
At present, there is no known practical attack that would allow someone without knowledge of the key to read data encrypted by AES when correctly implemented.
Side-channel attacks
[edit]Side-channel attacksdo not attack the cipher as ablack box,and thus are not related to cipher security as defined in the classical context, but are important in practice. They attack implementations of the cipher on hardware or software systems that inadvertently leak data. There are several such known attacks on various implementations of AES.
In April 2005,D. J. Bernsteinannounced a cache-timing attack that he used to break a custom server that usedOpenSSL's AES encryption.[31]The attack required over 200 million chosen plaintexts.[32]The custom server was designed to give out as much timing information as possible (the server reports back the number of machine cycles taken by the encryption operation). However, as Bernstein pointed out, "reducing the precision of the server's timestamps, or eliminating them from the server's responses, does not stop the attack: the client simply uses round-trip timings based on its local clock, and compensates for the increased noise by averaging over a larger number of samples."[31]
In October 2005, Dag Arne Osvik,Adi Shamirand Eran Tromer presented a paper demonstrating several cache-timing attacks against the implementations in AES found in OpenSSL and Linux'sdm-cryptpartition encryption function.[33]One attack was able to obtain an entire AES key after only 800 operations triggering encryptions, in a total of 65 milliseconds. This attack requires the attacker to be able to run programs on the same system or platform that is performing AES.
In December 2009 an attack on some hardware implementations was published that useddifferential fault analysisand allows recovery of a key with a complexity of 232.[34]
In November 2010 Endre Bangerter, David Gullasch and Stephan Krenn published a paper which described a practical approach to a "near real time" recovery of secret keys from AES-128 without the need for either cipher text or plaintext. The approach also works on AES-128 implementations that use compression tables, such as OpenSSL.[35]Like some earlier attacks, this one requires the ability to run unprivileged code on the system performing the AES encryption, which may be achieved by malware infection far more easily than commandeering the root account.[36]
In March 2016, Ashokkumar C., Ravi Prakash Giri and Bernard Menezes presented a side-channel attack on AES implementations that can recover the complete 128-bit AES key in just 6–7 blocks of plaintext/ciphertext, which is a substantial improvement over previous works that require between 100 and a million encryptions.[37]The proposed attack requires standard user privilege and key-retrieval algorithms run under a minute.
Many modern CPUs have built-inhardware instructions for AES,which protect against timing-related side-channel attacks.[38][39]
Quantum attacks
[edit]AES-256 is considered to bequantumresistant, as it has similar quantum resistance to AES-128's resistance against traditional, non-quantum, attacks at 128bits of security.AES-192 and AES-128 are not considered quantum resistant due to their smaller key sizes. AES-192 has a strength of 96 bits against quantum attacks and AES-128 has 64 bits of strength against quantum attacks, making them both insecure.[40][41]
NIST/CSEC validation
[edit]TheCryptographic Module Validation Program(CMVP) is operated jointly by the United States Government'sNational Institute of Standards and Technology(NIST) Computer Security Division and theCommunications Security Establishment(CSE) of the Government of Canada. The use of cryptographic modules validated to NISTFIPS 140-2is required by the United States Government for encryption of all data that has a classification ofSensitive but Unclassified(SBU) or above. From NSTISSP #11, National Policy Governing the Acquisition of Information Assurance: "Encryption products for protecting classified information will be certified by NSA, and encryption products intended for protecting sensitive information will be certified in accordance with NIST FIPS 140-2."[42]
The Government of Canada also recommends the use ofFIPS 140validated cryptographic modules in unclassified applications of its departments.
Although NIST publication 197 ( "FIPS 197" ) is the unique document that covers the AES algorithm, vendors typically approach the CMVP under FIPS 140 and ask to have several algorithms (such asTriple DESorSHA1) validated at the same time. Therefore, it is rare to find cryptographic modules that are uniquely FIPS 197 validated and NIST itself does not generally take the time to list FIPS 197 validated modules separately on its public web site. Instead, FIPS 197 validation is typically just listed as an "FIPS approved: AES" notation (with a specific FIPS 197 certificate number) in the current list of FIPS 140 validated cryptographic modules.
The Cryptographic Algorithm Validation Program (CAVP)[43]allows for independent validation of the correct implementation of the AES algorithm. Successful validation results in being listed on the NIST validations page.[44]This testing is a pre-requisite for the FIPS 140-2 module validation. However, successful CAVP validation in no way implies that the cryptographic module implementing the algorithm is secure. A cryptographic module lacking FIPS 140-2 validation or specific approval by the NSA is not deemed secure by the US Government and cannot be used to protect government data.[42]
FIPS 140-2 validation is challenging to achieve both technically and fiscally.[45]There is a standardized battery of tests as well as an element of source code review that must be passed over a period of a few weeks. The cost to perform these tests through an approved laboratory can be significant (e.g., well over $30,000 US)[45]and does not include the time it takes to write, test, document and prepare a module for validation. After validation, modules must be re-submitted and re-evaluated if they are changed in any way. This can vary from simple paperwork updates if the security functionality did not change to a more substantial set of re-testing if the security functionality was impacted by the change.
Test vectors
[edit]Test vectors are a set of known ciphers for a given input and key. NIST distributes the reference of AES test vectors as AES Known Answer Test (KAT) Vectors.[note 7]
Performance
[edit]High speed and low RAM requirements were some of the criteria of the AES selection process. As the chosen algorithm, AES performed well on a wide variety of hardware, from 8-bitsmart cardsto high-performance computers.
On aPentium Pro,AES encryption requires 18 clock cycles per byte (cpb),[46]equivalent to a throughput of about 11 MiB/s for a 200 MHz processor.
OnIntel CoreandAMD RyzenCPUs supportingAES-NI instruction setextensions, throughput can be multiple GiB/s.[47]On a IntelWestmereCPU, AES encryption using AES-NI takes about 1.3 cpb for AES-128 and 1.8 cpb for AES-256.[48]
Implementations
[edit]See also
[edit]- AES modes of operation
- Disk encryption
- Whirlpool– hash function created by Vincent Rijmen and Paulo S. L. M. Barreto
- List of free and open-source software packages
Notes
[edit]- ^Key sizes of 128, 160, 192, 224, and 256 bits are supported by the Rijndael algorithm, but only the 128, 192, and 256-bit key sizes are specified in the AES standard.
- ^Block sizes of 128, 160, 192, 224, and 256 bits are supported by the Rijndael algorithm for each key size, but only the 128-bit block size is specified in the AES standard.
- ^SeeAdvanced Encryption Standard processfor more details.
- ^SeeSecurity of AESbelow.
- ^Large-block variants of Rijndael use an array with additional columns, but always four rows.
- ^Rijndael variants with a larger block size have slightly different offsets. For blocks of sizes 128 bits and 192 bits, the shifting pattern is the same. Rowis shifted left circular bybytes. For a 256-bit block, the first row is unchanged and the shifting for the second, third and fourth row is 1 byte, 3 bytes and 4 bytes respectively—this change only applies for the Rijndael cipher when used with a 256-bit block, as AES does not use 256-bit blocks.
- ^The AES Known Answer Test (KAT) Vectors are available in Zip format within the NIST sitehereArchived2009-10-23 at theWayback Machine
References
[edit]- ^"Biclique Cryptanalysis of the Full AES"(PDF).Archived fromthe original(PDF)on March 6, 2016.RetrievedMay 1,2019.
- ^abAlex Biryukov and Dmitry Khovratovich,Related-key Cryptanalysis of the Full AES-192 and AES-256,"Related-key Cryptanalysis of the Full AES-192 and AES-256".Table 1.Archivedfrom the original on 2009-09-28.Retrieved2010-02-16.
- ^Bruce Schneier (2009-07-30)."Another New AES Attack".Schneier on Security, A blog covering security and security technology.Archivedfrom the original on 2009-10-05.Retrieved2010-03-11.
- ^Alex Biryukov; Orr Dunkelman; Nathan Keller; Dmitry Khovratovich; Adi Shamir (2009-08-19)."Key Recovery Attacks of Practical Complexity on AES Variants With Up To 10 Rounds".Archivedfrom the original on 28 January 2010.Retrieved2010-03-11.
- ^abDaemen, Joan; Rijmen, Vincent (March 9, 2003)."AES Proposal: Rijndael"(PDF).National Institute of Standards and Technology. p. 1.Archived(PDF)from the original on 5 March 2013.Retrieved21 February2013.
- ^abc"Announcing the ADVANCED ENCRYPTION STANDARD (AES)"(PDF).Federal Information Processing Standards Publication 197.United States National Institute of Standards and Technology (NIST). November 26, 2001.Archived(PDF)from the original on August 23, 2024.RetrievedAugust 26,2024.
- ^Joan Daemen and Vincent Rijmen (September 3, 1999)."AES Proposal: Rijndael"(PDF).Archived fromthe original(PDF)on February 3, 2007.
- ^John Schwartz (October 3, 2000)."U.S. Selects a New Encryption Technique".New York Times.Archivedfrom the original on March 28, 2017.
- ^Westlund, Harold B. (2002)."NIST reports measurable success of Advanced Encryption Standard".Journal of Research of the National Institute of Standards and Technology.Archived fromthe originalon 2007-11-03.
- ^"ISO/IEC 18033-3: Information technology – Security techniques – Encryption algorithms – Part 3: Block ciphers".Archivedfrom the original on 2013-12-03.
- ^Bruce Schneier; John Kelsey; Doug Whiting; David Wagner; Chris Hall; Niels Ferguson; Tadayoshi Kohno; et al. (May 2000)."The Twofish Team's Final Comments on AES Selection"(PDF).Archived(PDF)from the original on 2010-01-02.
- ^Bertoni, Guido; Breveglieri, Luca; Fragneto, Pasqualina; MacChetti, Marco; Marchesin, Stefano (2003)."Efficient Software Implementation of AES on 32-Bit Platforms".Cryptographic Hardware and Embedded Systems - CHES 2002.Lecture Notes in Computer Science. Vol. 2523. pp. 159–171.doi:10.1007/3-540-36400-5_13.ISBN978-3-540-00409-7.
- ^"byte-oriented-aes – A public domain byte-oriented implementation of AES in C – Google Project Hosting".Archivedfrom the original on 2013-07-20.Retrieved2012-12-23.
- ^Lynn Hathaway (June 2003)."National Policy on the Use of the Advanced Encryption Standard (AES) to Protect National Security Systems and National Security Information"(PDF).Archived(PDF)from the original on 2010-11-06.Retrieved2011-02-15.
- ^John Kelsey,Stefan Lucks,Bruce Schneier,Mike Stay,David Wagner,andDoug Whiting,Improved Cryptanalysis of Rijndael,Fast Software Encryption,2000 pp213–230"Academic: Improved Cryptanalysis of Rijndael - Schneier on Security".Archivedfrom the original on 2007-02-23.Retrieved2007-03-06.
- ^Ou, George (April 30, 2006)."Is encryption really crackable?".Ziff-Davis.Archivedfrom the original on August 8, 2010.RetrievedAugust 7,2010.
- ^"Sean Murphy".University of London.Archivedfrom the original on 2009-01-31.Retrieved2008-11-02.
- ^Bruce Schneier."AES News, Crypto-Gram Newsletter, September 15, 2002".Archivedfrom the original on 7 July 2007.Retrieved2007-07-27.
- ^ Niels Ferguson;Richard Schroeppel;Doug Whiting (2001)."A simple algebraic representation of Rijndael".Proceedings of Selected Areas in Cryptography, 2001, Lecture Notes in Computer Science.Springer-Verlag.pp. 103–111.CiteSeerX10.1.1.28.4921.Archived fromthe original(PDF/PostScript)on 4 November 2006.Retrieved2006-10-06.
- ^Bruce Schneier,AES AnnouncedArchived2009-02-01 at theWayback Machine,October 15, 2000
- ^Nikolić, Ivica (2009). "Distinguisher and Related-Key Attack on the Full AES-256".Advances in Cryptology - CRYPTO 2009.Lecture Notes in Computer Science. Vol. 5677. Springer Berlin / Heidelberg. pp. 231–249.doi:10.1007/978-3-642-03356-8_14.ISBN978-3-642-03355-1.
- ^Bruce Schneier (2009-07-30)."Another New AES Attack".Schneier on Security, A blog covering security and security technology.Archivedfrom the original on 2009-10-05.Retrieved2010-03-11.
- ^Alex Biryukov; Orr Dunkelman; Nathan Keller; Dmitry Khovratovich; Adi Shamir (2009-08-19)."Key Recovery Attacks of Practical Complexity on AES Variants With Up To 10 Rounds".Archivedfrom the original on 28 January 2010.Retrieved2010-03-11.
- ^Agren, Martin (2012).On Some Symmetric Lightweight Cryptographic Designs.Dissertation, Lund University. pp. 38–39.
- ^Vincent Rijmen (2010)."Practical-Titled Attack on AES-128 Using Chosen-Text Relations"(PDF).IACR Cryptology ePrint Archive.Archived(PDF)from the original on 2010-07-02.
- ^Henri Gilbert; Thomas Peyrin (2009-11-09)."Super-Sbox Cryptanalysis: Improved Attacks for AES-like permutations".IACR Cryptology ePrint Archive.Archivedfrom the original on 2010-06-04.Retrieved2010-03-11.
- ^Andrey Bogdanov; Dmitry Khovratovich & Christian Rechberger (2011)."Biclique Cryptanalysis of the Full AES"(PDF).Archived fromthe original(PDF)on 2012-09-05.
- ^abBiaoshuai Tao & Hongjun Wu (2015). "Improving the Biclique Cryptanalysis of AES".Information Security and Privacy.Lecture Notes in Computer Science. Vol. 9144. pp. 39–56.doi:10.1007/978-3-319-19962-7_3.ISBN978-3-319-19961-0.
- ^Jeffrey Goldberg (2011-08-18)."AES Encryption isn't Cracked".Archived fromthe originalon 8 January 2015.Retrieved30 December2014.
- ^SPIEGEL ONLINE, Hamburg, Germany (28 December 2014)."Inside the NSA's War on Internet Security".SPIEGEL ONLINE.Archivedfrom the original on 24 January 2015.Retrieved4 September2015.
- ^ab"Index of formal scientific papers".Cr.yp.to.Archivedfrom the original on 2008-09-17.Retrieved2008-11-02.
- ^Bruce Schneier."AES Timing Attack".Archivedfrom the original on 12 February 2007.Retrieved2007-03-17.
- ^Dag Arne Osvik; Adi Shamir; Eran Tromer (2005-11-20)."Cache Attacks and Countermeasures: the Case of AES"(PDF).The Cryptographer's Track at RSA Conference 2006.doi:10.1007/11605805_1.Archived(PDF)from the original on 2006-06-19.Retrieved2008-11-02.
- ^Dhiman Saha; Debdeep Mukhopadhyay; Dipanwita RoyChowdhury."A Diagonal Fault Attack on the Advanced Encryption Standard"(PDF).IACR Cryptology ePrint Archive.Archived(PDF)from the original on 22 December 2009.Retrieved2009-12-08.
- ^Endre Bangerter; David Gullasch & Stephan Krenn (2010)."Cache Games – Bringing Access-Based Cache Attacks on AES to Practice"(PDF).IACR Cryptology ePrint Archive.Archived(PDF)from the original on 2010-12-14.
- ^"Breaking AES-128 in realtime, no ciphertext required".Hacker News.Archivedfrom the original on 2011-10-03.Retrieved2012-12-23.
- ^Ashokkumar C.; Ravi Prakash Giri; Bernard Menezes (2016).2016 IEEE European Symposium on Security and Privacy (EuroS&P).pp. 261–275.doi:10.1109/EuroSP.2016.29.ISBN978-1-5090-1751-5.S2CID11251391.
- ^"Are AES x86 Cache Timing Attacks Still Feasible?"(PDF).cseweb.ucsd.edu.Archived(PDF)from the original on 2017-08-09.
- ^"Securing the Enterprise with Intel AES-NI"(PDF).Intel Corporation.Archived(PDF)from the original on 2013-03-31.Retrieved2017-07-26.
- ^Bonnetain, Xavier; Naya-Plasencia, María; Schrottenloher, André (December 6, 2019)."Quantum Security Analysis of AES".HAL:40.
- ^O'Shea, Dan (April 26, 2022)."AES-256 joins the quantum resistance".Fierce Electronics.RetrievedSeptember 26,2023.
- ^ab"NSTISSP No. 11, Revised Fact Sheet, National Information Assurance Acquisition Policy"(PDF).Archived fromthe original(PDF)on 2012-04-21.Retrieved2012-05-29.
- ^"NIST.gov – Computer Security Division – Computer Security Resource Center".Csrc.nist.gov.Archivedfrom the original on 2013-01-02.Retrieved2012-12-23.
- ^"Validated FIPS 140-1 and FIPS 140-2 Cryptographic Modules".Archived fromthe originalon 2014-12-26.Retrieved2014-06-26.
- ^abOpenSSL, [email protected]."OpenSSL's Notes about FIPS certification".Openssl.org. Archived fromthe originalon 2013-01-02.Retrieved2012-12-23.
- ^Schneier, Bruce; Kelsey, John; Whiting, Doug; Wagner, David; Hall, Chris; Ferguson, Niels (1999-02-01)."Performance Comparisons of the AES submissions"(PDF).Archived(PDF)from the original on 2011-06-22.Retrieved2010-12-28.
- ^"AMD Ryzen 7 1700X Review".
- ^"Intel ® Advanced Encryption Standard (AES) New Instructions Set"(PDF).May 2010.
- Courtois, Nicolas; Pieprzyk, Josef (2003)."Cryptanalysis of Block Ciphers with Overdefined Systems of Equations".In Zheng, Yuliang (ed.).Advances in Cryptology – ASIACRYPT 2002: 8th International Conference on the Theory and Application of Cryptology and Information Security, Queenstown, New Zealand, December 1–5, 2002, Proceedings.Springer. pp. 268–287.ISBN978-3-540-36178-7.
- Daemen, Joan; Rijmen, Vincent (2002).The Design of Rijndael: AES – The Advanced Encryption Standard.Springer.ISBN978-3-540-42580-9.
- Paar, Christof; Pelzl, Jan (2009).Understanding Cryptography: A Textbook for Students and Practitioners.Springer. pp. 87–122.ISBN978-3-642-04101-3.alternate link(companion web site contains online lectures on AES)
External links
[edit]- "256bit key – 128bit block – AES".Cryptography – 256 bit Ciphers: Reference source code and submissions to international cryptographic designs contests.EmbeddedSW.
- "Advanced Encryption Standard (AES)"(PDF).Federal Information Processing Standards.26 November 2001.doi:10.6028/NIST.FIPS.197.197.
- AES algorithm archive information – (old, unmaintained)
- "Part 3: Block ciphers"(PDF).Information technology – Security techniques – Encryption algorithms(2nd ed.). ISO. 2010-12-15. ISO/IEC 18033-3:2010(E).Archived(PDF)from the original on 2022-10-09.
- Animation of Rijndael– AES deeply explained and animated using Flash (by Enrique Zabala / University ORT / Montevideo / Uruguay). This animation (in English, Spanish, and German) is also part ofCrypTool 1(menu Indiv. Procedures → Visualization of Algorithms → AES).
- HTML5 Animation of Rijndael– Same Animation as above made in HTML5.













![{\displaystyle \operatorname {GF} (2)[x]}](https://wikimedia.org/api/rest_v1/media/math/render/svg/6334bd0b6ddc3a60f9d7590f71c74e11f780b80f)

