Software
Softwareconsists ofcomputer programsthat instruct theexecutionof acomputer.[2]
Building on previous innovations inmathematicsand technology, software was created for the programmabledigital computersthat emerged in the late 1940s and was necessary to realize their usefulness. The first software was tied closely to the underlyingcomputer hardware,but over time, the lowerlayersof the system have become more standardized, and software has become increasinglyportablebetween different systems and abstracted from the underlyingmachine code.Operating systemsmanage the hardware resources and mediate between differentapplicationsthat accomplish tasks for the user. Programming languages are the format in which software is written, and must be both human-readable and capable of being translated into unambiguous instructions for computer hardware.Compilersorinterpretersare needed to link a program with other code that it relies on and convert the software intomachine codethat can beexecutedon the hardware. Programs are combined with each other and with external input to be capable of accomplishing a complex task.
Software development's central task isprogrammingandmaintaininga project'ssource code,but the term also covers conceiving the project, evaluating its feasibility, analyzing the business requirements,software design,andrelease.Software quality assurance,includingcode reviewandtesting,is an essential part of the process, as delivering quality code lowers the cost ofreliabilityfailures,cyberattacksenabled bysecurity vulnerabilities,andmaintenance costs.Maintenance typically consumes 75 percent or more of the software's lifetime engineering budget. Source codeis protectedbycopyright law,which vests the owner with the exclusive right to copy the code. Software has become ubiquitous ineveryday lifeindeveloped countries.In many cases, software augments the functionality of pre-existing technologies, but it has also enabled the creation of entirely new technologies such asthe Internet,video games,social media,mobile phones,andGPS.
Definition
Software can be defined more narrowly as the instructions executed by thecomputer hardware,or more broadly including other concepts, tools, and methods needed to make anexecutablesystem oncomputer hardware,such as design documents, specifications, and testing suites.[3][4]An individualprogramorsource codefile consists of unambiguous instructions andalgorithms.Programs are combined with each other and with external input to be capable of accomplishing a complex task.[5][4]Tools such ascompilers,assemblers,flowcharts,design tools, simulators, andarchitectural diagrams—some of which are also software—are essential to the design and execution of most computing systems.[4]Although software isintangible,[6][7]software makes instructions forcomputer hardwareto produce visible and tangible effects.[8]
History

A host of earlier inventions were necessary for the creation of software, includingmathematics—especiallybinaryanddecimalnumber systems, andzero—Alpha bets,writing,mechanical calculators,[10]boolean algebra,transistors,integrated circuits,andplastics.[11]Software could not exist withoutdigital computers,as it was created specifically for these devices and was necessary to realize their usefulness.[12]
The first programmable computers, which appeared at the end of the 1940s,[13]were programmed inmachine language(simple instructions that could be directly executed by the processor). Machine language was difficult to debug and was notportablebetween different computer systems.[14]Initially, hardware resources were scarce and expensive, whilehuman resourceswere cheaper.[15]As programs grew more complex,programmer productivitybecame a bottleneck. This led to the introduction ofhigh-level programming languagesin the mid-1950s. These languagesabstractedaway the details of the hardware, instead being designed to express algorithms that could be understood more easily by humans.[16][17]As instructions are distinct from the underlyingcomputer hardware,software is therefore relatively recent, dating to these early high-levelprogramming languagessuch asFortran,Lisp,andCobol.[17]The first use of the wordsoftwareis credited to mathematicianJohn Wilder Tukeyin 1958.[4]As this first definition of software was negative (elements of a computer that were not “tubes, transistors, wires, tapes and the like.” ), it left open for a broad understanding of the concept of software, asHistorian of ComputingNathan Ensmenger posits. For historians, software is asociotechnical system,which means "a system in which machines, people, and processes are inextricably interconnected and interdependent", in Ensmenger's words.[18]Historian of Computing Thomas Haigh insists on the idea of circulation and argues “software always involves packaging disparate elements such as computer code, practices, algorithms,tacit knowledge,andintellectual property rightsinto an artifact suitable for dissemination”.[19]
The first software was tied closely to the underlying hardware and, consequently, was notportableto other systems. As it has evolved, newer software can be built and run on a wide variety of platforms. Much of the increase in portability can be attributed to the standardization of lower-level aspects of the system, such asnetworking,operating systems,anddatabases.Because there are only a relatively few operating systems,TCPandIPare used for virtually all networking, andSQLis used for many database queries,application softwarecan run more easily over a wide variety of hardware.[20]Increasing the number of layers ofabstractionin the system is a related development: both in programming languages where it enables better structure and increasedmodularity,as well as enablingvirtualizationof system resources. As a result of the increase in stability and abstraction, software has become increasingly complex and can solve more problems.[21]Both industry andacademiahave had a strong influence on the development of different aspects of software.[22]
Types

There are two main types of software:
- Operating systemsare "thelayer of softwarethat manages a computer's resources for its users and theirapplications".[23]There are three main purposes that an operating system fulfills:[24]
- Allocating resources between different applications, deciding when they will receivecentral processing unit(CPU) time or space inmemory.[24]
- Providing an interface that abstracts the details of accessinghardwaredetails (like physical memory) to make things easier for programmers.[24][25]
- Offering common services, such as an interface for accessing network and disk devices. This enables an application to be run on different hardware without needing to be rewritten.[26]
- Application softwareruns on top of the operating system and uses the computer's resources to perform a task.[27]There are many different types of application software because the range of tasks that can be performed with modern computers is so large.[28]Applications account for most software[29]and require theenvironmentprovided by an operating system, and often other applications, in order to function.[30]
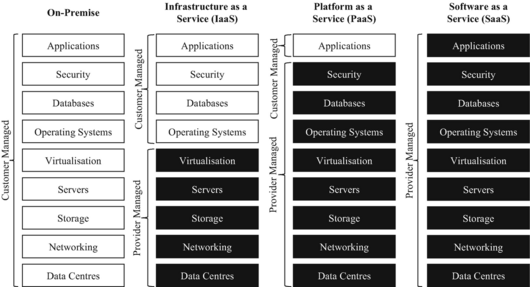
Software can also be categorized by how it isdeployed.Traditional applications are purchased with a perpetuallicensefor a specific version of the software, downloaded, and run on hardware belonging to the purchaser.[31]The rise ofthe Internetandcloud computingenabled a new model,software as a service(SaaS),[32]in which the provider hosts the software (usually built on top of rentedinfrastructureorplatforms)[33]and provides the use of the software to customers, often in exchange for asubscription fee.[31]By 2023, SaaS products—which are usually delivered via aweb application—had become the primary method that companies deliver applications.[34]
Software development and maintenance

Software companies aim to deliver a high-quality product on time and under budget. A challenge is thatsoftware development effort estimationis often inaccurate.[35]Software developmentbegins by conceiving the project, evaluating its feasibility, analyzing the business requirements, and making asoftware design.[36][37]Most software projects speed up their development byreusingor incorporating existing software, either in the form ofcommercial off-the-shelf(COTS) oropen-source software.[38][39]Software quality assuranceis typically a combination of manualcode reviewby other engineers[40]and automatedsoftware testing.Due to time constraints, testing cannot cover all aspects of the software's intended functionality, so developers often focus on the most critical functionality.[41]Formal methodsare used in some safety-critical systems to prove the correctness of code,[42]whileuser acceptance testinghelps to ensure that the product meets customer expectations.[43]There are a variety ofsoftware development methodologies,which vary from completing all steps in order to concurrent and iterative models.[44]Software development is driven byrequirementstaken from prospective users, as opposed to maintenance, which is driven by events such as a change request.[45]
Frequently, software isreleasedin an incomplete state when the development team runs out of time or funding.[46]Despitetestingandquality assurance,virtually all software containsbugswhere the system does not work as intended. Post-releasesoftware maintenanceis necessary to remediate these bugs when they are found and keep the software working as the environment changes over time.[47]New features are often added after the release. Over time, the level of maintenance becomes increasingly restricted before being cut off entirely when the product is withdrawn from the market.[48]As softwareages,it becomes known aslegacy softwareand can remain in use for decades, even if there is no one left who knows how to fix it.[6]Over the lifetime of the product, software maintenance is estimated to comprise 75 percent or more of the total development cost.[49][50]
Completing a software project involves various forms of expertise, not just insoftware programmersbut also testing, documentation writing,project management,graphic design,user experience,user support,marketing,and fundraising.[51][52][37]
Quality and security
Software qualityis defined as meeting the stated requirements as well as customer expectations.[53]Quality is an overarching term that can refer to a code's correct and efficient behavior, its reusability andportability,or the ease of modification.[54]It is usually more cost-effective to build quality into the product from the beginning rather than try to add it later in the development process.[55]Higher quality code will reduce lifetime cost to both suppliers and customers as it is more reliable andeasier to maintain.[56][57]Software failures insafety-critical systemscan be very serious including death.[56]By some estimates, the cost of poor quality software can be as high as 20 to 40 percent of sales.[58]Despite developers' goal of delivering a product that works entirely as intended, virtually all software contains bugs.[59]
The rise of the Internet also greatly increased the need forcomputer securityas it enabled malicious actors to conductcyberattacksremotely.[60][61]If a bug creates a security risk, it is called avulnerability.[62][63]Software patchesare often released to fix identified vulnerabilities, but those that remain unknown (zero days) as well as those that have not been patched are still liable for exploitation.[64]Vulnerabilities vary in their ability to beexploitedby malicious actors,[62]and the actual risk is dependent on the nature of the vulnerability as well as the value of the surrounding system.[65]Although some vulnerabilities can only be used fordenial of serviceattacks that compromise a system's availability, others allow the attacker toinjectand run their own code (calledmalware), without the user being aware of it.[62]To thwart cyberattacks, all software in the system must be designed to withstand and recover from external attack.[61]Despite efforts to ensure security, a significant fraction of computers are infected with malware.[66]
Encoding and execution
Programming languages

Programming languages are the format in which software is written. Since the 1950s, thousands of different programming languages have been invented; some have been in use for decades, while others have fallen into disuse.[67]Some definitions classifymachine code—the exact instructions directly implemented by the hardware—andassembly language—a more human-readable alternative to machine code whose statements can be translated one-to-one into machine code—as programming languages.[68]Programs written in thehigh-level programming languagesused to create software share a few main characteristics: knowledge of machine code is not necessary to write them, they can beportedto other computer systems, and they are more concise and human-readable than machine code.[69]They must be both human-readable and capable of being translated into unambiguous instructions for computer hardware.[70]
Compilation, interpretation, and execution
The invention of high-level programming languages was simultaneous with thecompilersneeded to translate them automatically into machine code.[71]Most programs do not contain all the resources needed to run them and rely on externallibraries.Part of the compiler's function is to link these files in such a way that the program can be executed by the hardware. Once compiled, the program can be saved as anobject fileand theloader(part of the operating system) can take this saved file andexecuteit as aprocesson the computer hardware.[72]Some programming languages use aninterpreterinstead of a compiler. An interpreter converts the program into machine code atrun time,which makes them 10 to 100 times slower than compiled programming languages.[73][74]
Legal issues
Liability
Software is often released with the knowledge that it is incomplete or contains bugs. Purchasers knowingly buy it in this state, which has led to a legal regime whereliabilityfor software products is significantly curtailed compared to other products.[75]
Licenses

Source code is protected bycopyright lawthat vests the owner with the exclusive right to copy the code. The underlying ideas or algorithms are not protected by copyright law, but are often treated as atrade secretand concealed by such methods asnon-disclosure agreements.[76]Software copyrighthas been recognized since the mid-1970s and is vested in the company that makes the software, not the employees orcontractorswho wrote it.[77]The use of most software is governed by an agreement (software license) between the copyright holder and the user.Proprietary softwareis usually sold under a restrictive license that limits copying and reuse (often enforced with tools such asdigital rights management(DRM)).[78]Open-source licenses,in contrast, allow free use and redistribution of software with few conditions.[77]Most open-source licenses used for software require that modifications be released under the same license, which can create complications when open-source software is reused in proprietary projects.[79]
Patents
Patentsgive an inventor an exclusive, time-limited license for a novel product or process.[80]Ideas about what software could accomplish are not protected by law and concrete implementations are instead covered bycopyright law.In some countries, a requirement for the claimed invention to have an effect on the physical world may also be part of the requirements for a software patent to be held valid.[81]Software patentshave beenhistorically controversial.Before the 1998 caseState Street Bank & Trust Co. v. Signature Financial Group, Inc.,software patents were generally not recognized in the United States. In that case, theSupreme Courtdecided that business processes could be patented.[11]Patent applications are complex and costly, and lawsuits involving patents can drive up the cost of products.[82]Unlike copyrights, patents generally only apply in the jurisdiction where they were issued.[83]
Impact

EngineerCapers Joneswrites that "computers and software are making profound changes to every aspect of human life: education, work, warfare, entertainment, medicine, law, and everything else".[85]It has become ubiquitous ineveryday lifeindeveloped countries.[86]In many cases, software augments the functionality of existing technologies such as householdappliancesandelevators.[1]Software also spawned entirely new technologies such asthe Internet,video games,mobile phones,andGPS.[1][87]New methods of communication, includingemail,forums,blogs,microblogging,wikis,andsocial media,were enabled by the Internet.[88]Massive amounts of knowledge exceeding any paper-based library are now available with a quickweb search.[87]Most creative professionals have switched to software-based tools such ascomputer-aided design,3D modeling,digitalimage editing,andcomputer animation.[84]Almost every complex device is controlled by software.[87]
References
- ^abcKitchin & Dodge 2011,p. 5.
- ^Stair, Ralph M. (2003).Principles of Information Systems, Sixth Edition.Thomson. p. 16.ISBN0-619-06489-7.
Software consists of computer programs that govern the operation of the computer.
- ^Osterweil 2013,p. 61.
- ^abcdTracy 2021,p. 2.
- ^Kitchin & Dodge 2011,pp. 3, 24.
- ^abTracy 2021,p. 3.
- ^Kitchin & Dodge 2011,p. 24.
- ^Kitchin & Dodge 2011,pp. 3–4.
- ^Jones 2014,pp. 19, 22.
- ^Jones 2014,pp. 9, 21.
- ^abJones 2014,p. 19.
- ^Jones 2014,p. 22.
- ^Gabbrielli & Martini 2023,p. 519.
- ^Gabbrielli & Martini 2023,pp. 520–521.
- ^Gabbrielli & Martini 2023,p. 522.
- ^Gabbrielli & Martini 2023,p. 521.
- ^abTracy 2021,p. 1.
- ^Ensmenger, Nathan (2010).The computer boys take over: computers, programmers, and the politics of technical expertise.History of computing. Cambridge, Mass: MIT Press.ISBN978-0-262-05093-7.OCLC496282165.
- ^Hocquet, Alexandre; Wieber, Frédéric; Gramelsberger, Gabriele; Hinsen, Konrad; Diesmann, Markus; Pasquini Santos, Fernando; Landström, Catharina; Peters, Benjamin; Kasprowicz, Dawid; Borrelli, Arianna; Roth, Phillip; Lee, Clarissa Ai Ling; Olteanu, Alin; Böschen, Stefan (1 July 2024)."Software in science is ubiquitous yet overlooked".Nature Computational Science.doi:10.1038/s43588-024-00651-2.ISSN2662-8457.
- ^Tracy 2021,p. 249.
- ^Tracy 2021,p. 250.
- ^Tracy 2021,pp. 250–251.
- ^Anderson & Dahlin 2014,p. 6.
- ^abcAnderson & Dahlin 2014,p. 7.
- ^Tanenbaum & Bos 2023,p. 5.
- ^Anderson & Dahlin 2014,pp. 7, 9, 13.
- ^Anderson & Dahlin 2014,pp. 6–7.
- ^Jones 2014,p. 121.
- ^Tracy 2021,p. 66.
- ^Tracy 2021,p. 72.
- ^abO'Regan 2022,p. 386.
- ^Campbell-Kelly & Garcia-Swartz 2015,pp. 156–157.
- ^Rosati & Lynn 2020,p. 23.
- ^Watt 2023,p. 4.
- ^O'Regan 2022,p. 7.
- ^O'Regan 2022,p. 5.
- ^abDooley 2017,p. 1.
- ^O'Regan 2022,pp. 18, 110–111.
- ^Tracy 2021,pp. 43, 76.
- ^O'Regan 2022,pp. 117–118.
- ^O'Regan 2022,p. 54.
- ^O'Regan 2022,p. 267.
- ^O'Regan 2022,p. 20.
- ^O'Regan 2022,p. 9.
- ^Tripathy & Naik 2014,p. 26.
- ^Reifer 2012,p. 22.
- ^Tripathy & Naik 2014,pp. 4, 27.
- ^Tripathy & Naik 2014,p. 89.
- ^Varga 2018,p. 6.
- ^Ulziitet al.2015,p. 764.
- ^Tucker, Morelli & de Silva 2011,p. 7.
- ^Stull 2018,pp. 24–25.
- ^Galin 2018,p. 3.
- ^Galin 2018,p. 26.
- ^O'Regan 2022,pp. 68, 117.
- ^abO'Regan 2022,pp. 3, 268.
- ^Varga 2018,p. 12.
- ^O'Regan 2022,p. 119.
- ^Ablon & Bogart 2017,p. 1.
- ^Campbell-Kelly & Garcia-Swartz 2015,p. 164.
- ^abO'Regan 2022,p. 266.
- ^abcAblon & Bogart 2017,p. 2.
- ^Daswani & Elbayadi 2021,p. 25.
- ^Daswani & Elbayadi 2021,pp. 26–27.
- ^Haber & Hibbert 2018,pp. 5–6.
- ^Kitchin & Dodge 2011,p. 37.
- ^Tracy 2021,p. 117.
- ^Tracy 2021,pp. 118–120.
- ^Tracy 2021,pp. 118–119.
- ^Kitchin & Dodge 2011,p. 26.
- ^Tracy 2021,p. 121.
- ^Tracy 2021,pp. 122–123.
- ^O'Regan 2022,p. 375.
- ^Sebesta 2012,p. 28.
- ^Kitchin & Dodge 2011,pp. 36–37.
- ^O'Regan 2022,pp. 394–396.
- ^abO'Regan 2022,p. 403.
- ^O'Regan 2022,pp. 394, 404.
- ^Langer 2016,pp. 44–45.
- ^O'Regan 2022,p. 395.
- ^Gerardo Con Díaz, "The Text in the Machine: American Copyright Law and the Many Natures of Software, 1974–1978",Technology and Culture57 (October 2016), 753–79.
- ^O'Regan 2022,p. 398.
- ^O'Regan 2022,p. 399.
- ^abManovich 2013,p. 333.
- ^Jones 2014,p. 32.
- ^Kitchin & Dodge 2011,p. iv.
- ^abcJones 2014,p. xxviii.
- ^Manovich 2013,p. 329.
Sources
- Ablon, Lillian; Bogart, Andy (2017).Zero Days, Thousands of Nights: The Life and Times of Zero-Day Vulnerabilities and Their Exploits(PDF).Rand Corporation.ISBN978-0-8330-9761-3.
- Anderson, Thomas;Dahlin, Michael (2014).Operating Systems: Principles and Practice(2 ed.). Recursive Books.ISBN978-0-9856735-2-9.
- Campbell-Kelly, Martin; Garcia-Swartz, Daniel D. (2015).From Mainframes to Smartphones: A History of the International Computer Industry.Harvard University Press.ISBN978-0-674-28655-9.
- Daswani, Neil;Elbayadi, Moudy (2021).Big Breaches: Cybersecurity Lessons for Everyone.Apress.ISBN978-1-4842-6654-0.
- Dooley, John F. (2017).Software Development, Design and Coding: With Patterns, Debugging, Unit Testing, and Refactoring.Apress.ISBN978-1-4842-3153-1.
- Gabbrielli, Maurizio; Martini, Simone (2023).Programming Languages: Principles and Paradigms(2nd ed.). Springer.ISBN978-3-031-34144-1.
- Galin, Daniel (2018).Software Quality: Concepts and Practice.John Wiley & Sons.ISBN978-1-119-13449-7.
- Haber, Morey J.; Hibbert, Brad (2018).Asset Attack Vectors: Building Effective Vulnerability Management Strategies to Protect Organizations.Apress.ISBN978-1-4842-3627-7.
- Jones, Capers (2014).The Technical and Social History of Software Engineering.Pearson Education.ISBN978-0-321-90342-6.
- Kitchin, Rob; Dodge, Martin (2011).Code/space: Software and Everyday Life.MIT Press.ISBN978-0-262-04248-2.
- Langer, Arthur M. (2016).Guide to Software Development: Designing and Managing the Life Cycle.Springer.ISBN978-1-4471-6799-0.
- Manovich, Lev (2013).Software Takes Command.Bloomsbury Academic.ISBN978-1-62356-745-3.
- O'Regan, Gerard (2022).Concise Guide to Software Engineering: From Fundamentals to Application Methods.Springer Nature.ISBN978-3-031-07816-3.
- Osterweil, Leon J. (2013). "What Is Software? The Role of Empirical Methods in Answering the Question".Perspectives on the Future of Software Engineering: Essays in Honor of Dieter Rombach.Springer. pp. 237–254.ISBN978-3-642-37395-4.
- Rahman, Hanif Ur; da Silva, Alberto Rodrigues; Alzayed, Asaad; Raza, Mushtaq (2024). "A Systematic Literature Review on Software Maintenance Offshoring Decisions".Information and Software Technology.172:107475.doi:10.1016/j.infsof.2024.107475.
- Reifer, Donald J. (2012).Software Maintenance Success Recipes.CRC Press.ISBN978-1-4398-5167-8.
- Rosati, Pierangelo; Lynn, Theo (2020). "Measuring the Business Value of Infrastructure Migration to the Cloud".Measuring the Business Value of Cloud Computing.Springer International Publishing. pp. 19–37.ISBN978-3-030-43198-3.
- Sebesta, Robert W. (2012).Concepts of Programming Languages(10 ed.). Addison-Wesley.ISBN978-0-13-139531-2.
- Stull, Edward (2018).UX Fundamentals for Non-UX Professionals: User Experience Principles for Managers, Writers, Designers, and Developers.Apress.ISBN978-1-4842-3811-0.
- Tanenbaum, Andrew S.;Bos, Herbert (2023).Modern Operating Systems, Global Edition.Pearson Higher Ed.ISBN978-1-292-72789-9.
- Tracy, Kim W. (2021).Software: A Technical History.Morgan & Claypool Publishers.ISBN978-1-4503-8724-8.
- Tripathy, Priyadarshi; Naik, Kshirasagar (2014).Software Evolution and Maintenance: A Practitioner's Approach.John Wiley & Sons.ISBN978-0-470-60341-3.
- Tucker, Allen; Morelli, Ralph; de Silva, Chamindra (2011).Software Development: An Open Source Approach.CRC Press.ISBN978-1-4398-8460-7.
- Ulziit, Bayarbuyan; Warraich, Zeeshan Akhtar; Gencel, Cigdem; Petersen, Kai (2015). "A conceptual framework of challenges and solutions for managing global software maintenance".Journal of Software: Evolution and Process.27(10): 763–792.doi:10.1002/smr.1720.
- Watt, Andy (2023).Building Modern SaaS Applications with C# And. NET: Build, Deploy, and Maintain Professional SaaS Applications.Packt.ISBN978-1-80461-087-9.
- Varga, Ervin (2018).Unraveling Software Maintenance and Evolution: Thinking Outside the Box.Springer.ISBN978-3-319-71303-8.
