Domain Name System
| Internet protocol suite |
|---|
| Application layer |
| Transport layer |
| Internet layer |
| Link layer |
TheDomain Name System(DNS) is a hierarchical and distributedname servicethat provides a naming system forcomputers,services, and other resources on the Internet or otherInternet Protocol(IP) networks. It associates various information withdomain names(identificationstrings) assigned to each of the associated entities. Most prominently, it translates readily memorized domain names to the numericalIP addressesneeded for locating and identifying computer services and devices with the underlyingnetwork protocols.[1]The Domain Name System has been an essential component of the functionality of the Internet since 1985.
The Domain Name System delegates the responsibility of assigning domain names and mapping those names to Internet resources by designatingauthoritative name serversfor each domain. Network administrators may delegate authority oversubdomainsof their allocated name space to other name servers. This mechanism provides distributed andfault-tolerantservice and was designed to avoid a single large central database. In addition, the DNS specifies the technical functionality of thedatabaseservice that is at its core. It defines the DNS protocol, a detailed specification of the data structures and data communication exchanges used in the DNS, as part of theInternet protocol suite.
The Internet maintains two principalnamespaces,the domain name hierarchy and the IPaddress spaces.[2]The Domain Name System maintains the domain name hierarchy and provides translation services between it and the address spaces. Internet name servers and acommunication protocolimplement the Domain Name System. A DNS name server is a server that stores the DNS records for a domain; a DNS name server responds with answers to queries against its database.
The most common types of records stored in the DNS database are for start of authority (SOA), IP addresses (AandAAAA),SMTPmail exchangers(MX), name servers (NS), pointers forreverse DNS lookups(PTR), anddomain name aliases(CNAME). Although not intended to be a general purpose database, DNS has been expanded over time to store records for other types of data for either automatic lookups, such asDNSSECrecords, or for human queries such asresponsible person(RP) records. As a general purpose database, the DNS has also been used in combatingunsolicited email(spam) by storing areal-time blackhole list(RBL). The DNS database is traditionally stored in a structured text file, thezone file,but other database systems are common.
The Domain Name System originally used theUser Datagram Protocol(UDP) as transport over IP. Reliability, security, and privacy concerns spawned the use of theTransmission Control Protocol(TCP) as well as numerous other protocol developments.
Function[edit]
An often-used analogy to explain the DNS is that it serves as thephone bookfor the Internet by translating human-friendly computerhostnamesinto IP addresses. For example, the hostnameexamplewithin the domain nameexampletranslates to the addresses93.184.216.34(IPv4) and2606:2800:220:1:248:1893:25c8:1946(IPv6). The DNS can be quickly and transparently updated, allowing a service's location on the network to change without affecting the end users, who continue to use the same hostname. Users take advantage of this when they use meaningful Uniform Resource Locators (URLs) ande-mail addresseswithout having to know how the computer actually locates the services.
An important andubiquitousfunction of the DNS is its central role in distributed Internet services such ascloud servicesandcontent delivery networks.[3]When a user accesses a distributed Internet service using a URL, the domain name of theURLis translated to the IP address of a server that is proximal to the user. The key functionality of the DNS exploited here is that different users cansimultaneouslyreceive different translations for thesamedomain name, a key point of divergence from a traditional phone-book view of the DNS. This process of using the DNS to assign proximal servers to users is key to providing faster and more reliable responses on the Internet and is widely used by most major Internet services.[4]
The DNS reflects the structure of administrative responsibility on the Internet.[5]Each subdomain is azoneof administrative autonomy delegated to a manager. For zones operated by aregistry,administrative information is often complemented by the registry'sRDAPandWHOISservices. That data can be used to gain insight on, and track responsibility for, a given host on the Internet.[6]
History[edit]
Using a simpler, more memorable name in place of a host's numerical address dates back to theARPANETera. The Stanford Research Institute (nowSRI International) maintained a text file namedHOSTS.TXTthat mapped host names to the numerical addresses of computers on the ARPANET.[7][8]Elizabeth Feinlerdeveloped and maintained the first ARPANET directory.[9][10]Maintenance of numerical addresses, called the Assigned Numbers List, was handled byJon Postelat theUniversity of Southern California'sInformation Sciences Institute(ISI), whose team worked closely with SRI.[11]
Addresses were assigned manually. Computers, including their hostnames and addresses, were added to the primary file by contacting the SRINetwork Information Center(NIC), directed by Feinler, viatelephoneduring business hours.[12]Later, Feinler set up aWHOISdirectory on a server in the NIC for retrieval of information about resources, contacts, and entities.[13]She and her team developed the concept of domains.[13]Feinler suggested that domains should be based on the location of the physical address of the computer.[14]Computers at educational institutions would have the domainedu,for example.[15]She and her team managed the Host Naming Registry from 1972 to 1989.[16]
By the early 1980s, maintaining a single, centralized host table had become slow and unwieldy and the emerging network required an automated naming system to address technical and personnel issues. Postel directed the task of forging a compromise between five competing proposals of solutions toPaul Mockapetris.Mockapetris instead created the Domain Name System in 1983 while at theUniversity of Southern California.[12][17]
TheInternet Engineering Task Forcepublished the original specifications in RFC 882 and RFC 883 in November 1983.[18][19]These were updated in RFC 973 in January 1986.
In 1984, fourUC Berkeleystudents, Douglas Terry, Mark Painter, David Riggle, and Songnian Zhou, wrote the firstUnixname serverimplementation for the Berkeley Internet Name Domain, commonly referred to asBIND.[20]In 1985, Kevin Dunlap ofDECsubstantially revised the DNS implementation.Mike Karels,Phil Almquist, andPaul Vixiethen took over BIND maintenance.Internet Systems Consortiumwas founded in 1994 byRick Adams,Paul Vixie,andCarl Malamud,expressly to provide a home for BIND development and maintenance. BIND versions from 4.9.3 onward were developed and maintained by ISC, with support provided by ISC's sponsors. As co-architects/programmers, Bob Halley and Paul Vixie released the first production-ready version of BIND version 8 in May 1997. Since 2000, over 43 different core developers have worked on BIND.[21]
In November 1987, RFC 1034[22]and RFC 1035[5]superseded the 1983 DNS specifications. Several additionalRequest for Commentshave proposed extensions to the core DNS protocols.[23]
Structure[edit]
Domain name space[edit]
The domain name space consists of atree data structure.Each node or leaf in the tree has alabeland zero or moreresource records(RR), which hold information associated with the domain name. The domain name itself consists of the label, concatenated with the name of its parent node on the right, separated by a dot.[24]
The tree sub-divides intozonesbeginning at theroot zone.ADNS zonemay consist of as many domains and subdomains as the zone manager chooses. DNS can also be partitioned according toclasswhere the separate classes can be thought of as an array of parallel namespace trees.[25]
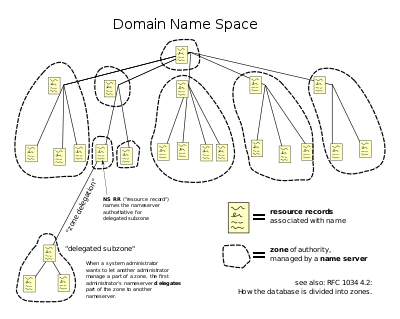
Administrative responsibility for any zone may be divided by creating additional zones. Authority over the new zone is said to bedelegatedto a designated name server. The parent zone ceases to be authoritative for the new zone.[25]
Domain name syntax, internationalization[edit]
The definitive descriptions of the rules for forming domain names appear in RFC 1035, RFC 1123, RFC 2181, and RFC 5892. Adomain nameconsists of one or more parts, technically calledlabels,that are conventionallyconcatenated,and delimited by dots, such as example.
The right-most label conveys thetop-level domain;for example, the domain name example belongs to the top-level domaincom.
The hierarchy of domains descends from right to left; each label to the left specifies a subdivision, orsubdomainof the domain to the right. For example, the labelexamplespecifies a subdomain of thecomdomain, andwwwis a subdomain of example. This tree of subdivisions may have up to 127 levels.[26]
A label may contain zero to 63 characters. The null label of length zero is reserved for the root zone. The full domain name may not exceed the length of 253 characters in its textual representation.[22]In the internal binary representation of the DNS the maximum length requires 255 octets of storage, as it also stores the length of the name.[5]
Although no technical limitation exists to prevent domain name labels from using any character that is representable by an octet, hostnames use a preferred format and character set. The characters allowed in labels are a subset of theASCIIcharacter set, consisting of charactersathroughz,AthroughZ,digits0through9,and hyphen. This rule is known as theLDH rule(letters, digits, hyphen). Domain names are interpreted in a case-independent manner.[27]Labels may not start or end with a hyphen.[28]An additional rule requires that top-level domain names should not be all-numeric.[28]
The limited set of ASCII characters permitted in the DNS prevented the representation of names and words of many languages in their native Alpha bets or scripts. To make this possible,ICANNapproved theInternationalizing Domain Names in Applications(IDNA) system, by which user applications, such as web browsers, mapUnicodestrings into the valid DNS character set usingPunycode.In 2009, ICANN approved the installation of internationalized domain namecountry code top-level domains (ccTLDs).In addition, manyregistriesof the existing top-level domain names (TLDs) have adopted the IDNA system, guided by RFC 5890, RFC 5891, RFC 5892, RFC 5893.
Name servers[edit]
The Domain Name System is maintained by adistributed databasesystem, which uses theclient–server model.The nodes of this database are thename servers.Each domain has at least one authoritative DNS server that publishes information about that domain and the name servers of any domains subordinate to it. The top of the hierarchy is served by theroot name servers,the servers to query when looking up (resolving) aTLD.
Authoritative name server[edit]
Anauthoritativename server is a name server that only givesanswersto DNS queries from data that have been configured by an original source, for example, the domain administrator or by dynamic DNS methods, in contrast to answers obtained via a query to another name server that only maintains a cache of data.
An authoritative name server can either be aprimaryserver or asecondaryserver. Historically the termsmaster/slaveandprimary/secondarywere sometimes used interchangeably[29]but the current practice is to use the latter form. A primary server is a server that stores the original copies of all zone records. A secondary server uses a specialautomatic updating mechanismin the DNS protocol in communication with its primary to maintain an identical copy of the primary records.
Every DNS zone must be assigned a set of authoritative name servers. This set of servers is stored in the parent domain zone with name server (NS) records.
An authoritative server indicates its status of supplying definitive answers, deemedauthoritative,by setting a protocol flag, called the "Authoritative Answer"(AA)bitin its responses.[5]This flag is usually reproduced prominently in the output of DNS administration query tools, such asdig,to indicatethat the responding name server is an authority for the domain name in question.[5]
When a name server is designated as the authoritative server for a domain name for which it does not have authoritative data, it presents a type of error called a "lame delegation" or "lame response".[30][31]
Operation[edit]
Address resolution mechanism[edit]
Domain name resolvers determine the domain name servers responsible for the domain name in question by a sequence of queries starting with the right-most (top-level) domain label.

For proper operation of its domain name resolver, a network host is configured with an initial cache (hints) of the known addresses of the root name servers. The hints are updated periodically by an administrator by retrieving a dataset from a reliable source.
Assuming the resolver has no cached records to accelerate the process, the resolution process starts with a query to one of the root servers. In typical operation, the root servers do not answer directly, but respond with a referral to more authoritative servers, e.g., a query for "wikipedia.org" is referred to theorgservers. The resolver now queries the servers referred to, and iteratively repeats this process until it receives an authoritative answer. The diagram illustrates this process for the host that is named by thefully qualified domain name"wikipedia.org".
This mechanism would place a large traffic burden on the root servers, if every resolution on the Internet required starting at the root. In practicecachingis used in DNS servers to off-load the root servers, and as a result, root name servers actually are involved in only a relatively small fraction of all requests.
Recursive and caching name server[edit]
In theory, authoritative name servers are sufficient for the operation of the Internet. However, with only authoritative name servers operating, every DNS query must start with recursive queries at theroot zoneof the Domain Name System and each user system would have to implement resolver software capable of recursive operation.[32]
To improve efficiency, reduce DNS traffic across the Internet, and increase performance in end-user applications, the Domain Name System supports DNS cache servers which store DNS query results for a period of time determined in the configuration (time-to-live) of the domain name record in question. Typically, such caching DNS servers also implement the recursive algorithm necessary to resolve a given name starting with the DNS root through to the authoritative name servers of the queried domain. With this function implemented in the name server, user applications gain efficiency in design and operation.
The combination of DNS caching and recursive functions in a name server is not mandatory; the functions can be implemented independently in servers for special purposes.
Internet service providerstypically provide recursive and caching name servers for their customers. In addition, many home networking routers implement DNS caches and recursion to improve efficiency in the local network.
DNS resolvers[edit]
Theclient sideof the DNS is called a DNS resolver. A resolver is responsible for initiating and sequencing the queries that ultimately lead to a full resolution (translation) of the resource sought, e.g., translation of a domain name into an IP address. DNS resolvers are classified by a variety of query methods, such asrecursive,non-recursive,anditerative.A resolution process may use a combination of these methods.[22]
In anon-recursive query,a DNS resolver queries a DNS server that provides a record either for which the server is authoritative, or it provides a partial result without querying other servers. In case of acaching DNS resolver,the non-recursive query of its localDNS cachedelivers a result and reduces the load on upstream DNS servers by caching DNS resource records for a period of time after an initial response from upstream DNS servers.
In arecursive query,a DNS resolver queries a single DNS server, which may in turn query other DNS servers on behalf of the requester. For example, a simple stub resolver running on ahome routertypically makes a recursive query to the DNS server run by the user'sISP.A recursive query is one for which the DNS server answers the query completely by querying other name servers as needed. In typical operation, a client issues a recursive query to a caching recursive DNS server, which subsequently issues non-recursive queries to determine the answer and send a single answer back to the client. The resolver, or another DNS server acting recursively on behalf of the resolver, negotiates use of recursive service using bits in the query headers. DNS servers are not required to support recursive queries.
Theiterative queryprocedure is a process in which a DNS resolver queries a chain of one or more DNS servers. Each server refers the client to the next server in the chain, until the current server can fully resolve the request. For example, a possible resolution of example would query a global root server, then a "com" server, and finally an "example" server.
Circular dependencies and glue records[edit]
Name servers in delegations are identified by name, rather than by IP address. This means that a resolving name server must issue another DNS request to find out the IP address of the server to which it has been referred. If the name given in the delegation is a subdomain of the domain for which the delegation is being provided, there is acircular dependency.
In this case, the name server providing the delegation must also provide one or more IP addresses for the authoritative name server mentioned in the delegation. This information is calledglue.The delegating name server provides this glue in the form of records in theadditional sectionof the DNS response, and provides the delegation in theauthority sectionof the response. A glue record is a combination of the name server and IP address.
For example, if theauthoritative name serverfor example.org is ns1.example.org, a computer trying to resolve example.org first resolves ns1.example.org. As ns1 is contained in example.org, this requires resolving example.org first, which presents a circular dependency. To break the dependency, the name server for thetop level domainorg includes glue along with the delegation for example.org. The glue records are address records that provide IP addresses for ns1.example.org. The resolver uses one or more of these IP addresses to query one of the domain's authoritative servers, which allows it to complete the DNS query.
Record caching[edit]
A common approach to reduce the burden on DNS servers is to cache the results of name resolution locally or on intermediary resolver hosts. Each DNS query result comes with a time to live (TTL), which indicates how long the information remains valid before it needs to be discarded or refreshed. This TTL is determined by the administrator of the authoritative DNS server and can range from a few seconds to several days or even weeks.[33]
As a result of this distributed caching architecture, changes to DNS records do not propagate throughout the network immediately, but require all caches to expire and to be refreshed after the TTL. RFC 1912 conveys basic rules for determining appropriate TTL values.
Some resolvers may override TTL values, as the protocol supports caching for up to sixty-eight years or no caching at all.Negative caching,i.e. the caching of the fact of non-existence of a record, is determined by name servers authoritative for a zone which must include theStart of Authority(SOA) record when reporting no data of the requested type exists. The value of theminimumfield of the SOA record and the TTL of the SOA itself is used to establish the TTL for the negative answer.
Reverse lookup[edit]
Areverse DNS lookupis a query of the DNS for domain names when the IP address is known. Multiple domain names may be associated with an IP address. The DNS stores IP addresses in the form of domain names as specially formatted names in pointer (PTR) records within the infrastructure top-level domainarpa.For IPv4, the domain is in-addr.arpa. For IPv6, the reverse lookup domain is ip6.arpa. The IP address is represented as a name in reverse-ordered octet representation for IPv4, and reverse-ordered nibble representation for IPv6.
When performing a reverse lookup, the DNS client converts the address into these formats before querying the name for a PTR record following the delegation chain as for any DNS query. For example, assuming the IPv4 address 208.80.152.2 is assigned to Wikimedia, it is represented as a DNS name in reverse order: 2.152.80.208.in-addr.arpa. When the DNS resolver gets a pointer (PTR) request, it begins by querying the root servers, which point to the servers ofAmerican Registry for Internet Numbers(ARIN) for the 208.in-addr.arpa zone. ARIN's servers delegate 152.80.208.in-addr.arpa to Wikimedia to which the resolver sends another query for 2.152.80.208.in-addr.arpa, which results in an authoritative response.
Client lookup[edit]

Users generally do not communicate directly with a DNS resolver. Instead DNS resolution takes place transparently in applications such asweb browsers,e-mail clients,and other Internet applications. When an application makes a request that requires a domain name lookup, such programs send a resolution request to theDNS resolverin the local operating system, which in turn handles the communications required.
The DNS resolver will almost invariably have a cache (see above) containing recent lookups. If the cache can provide the answer to the request, the resolver will return the value in the cache to the program that made the request. If the cache does not contain the answer, the resolver will send the request to one or more designated DNS servers. In the case of most home users, the Internet service provider to which the machine connects will usually supply this DNS server: such a user will either have configured that server's address manually or allowedDHCPto set it; however, where systems administrators have configured systems to use their own DNS servers, their DNS resolvers point to separately maintained name servers of the organization. In any event, the name server thus queried will follow the process outlinedabove,until it either successfully finds a result or does not. It then returns its results to the DNS resolver; assuming it has found a result, the resolver duly caches that result for future use, and hands the result back to the software which initiated the request.
Broken resolvers[edit]
Some large ISPs have configured their DNS servers to violate rules, such as by disobeying TTLs, or by indicating that a domain name does not exist just because one of its name servers does not respond.[34]
Some applications such as web browsers maintain an internal DNS cache to avoid repeated lookups via the network. This practice can add extra difficulty when debugging DNS issues as it obscures the history of such data. These caches typically use very short caching times on the order of one minute.[35]
Internet Explorerrepresents a notable exception: versions up to IE 3.x cache DNS records for 24 hours by default. Internet Explorer 4.x and later versions (up to IE 8) decrease the default timeout value to half an hour, which may be changed by modifying the default configuration.[36]
WhenGoogle Chromedetects issues with the DNS server it displays a specific error message.
Other applications[edit]
The Domain Name System includes several other functions and features.
Hostnames and IP addresses are not required to match in a one-to-one relationship. Multiple hostnames may correspond to a single IP address, which is useful invirtual hosting,in which many web sites are served from a single host. Alternatively, a single hostname may resolve to many IP addresses to facilitatefault toleranceandload distributionto multiple server instances across an enterprise or the global Internet.
DNS serves other purposes in addition to translating names to IP addresses. For instance,mail transfer agentsuse DNS to find the best mail server to delivere-mail:AnMX recordprovides a mapping between a domain and a mail exchanger; this can provide an additional layer of fault tolerance and load distribution.
The DNS is used for efficient storage and distribution of IP addresses of blacklisted email hosts. A common method is to place the IP address of the subject host into the sub-domain of a higher level domain name, and to resolve that name to a record that indicates a positive or a negative indication.
For example:
- The address203.0.113.5is blacklisted. It points to5.113.0.203.blacklist.example,which resolves to127.0.0.1.
- The address203.0.113.6is not blacklisted and points to6.113.0.203.blacklist.example.This hostname is either not configured, or resolves to127.0.0.2.
E-mail servers can query blacklist.example to find out if a specific host connecting to them is in the blacklist. Many of such blacklists, either subscription-based or free of cost, are available for use by email administrators and anti-spam software.
To provide resilience in the event of computer or network failure, multiple DNS servers are usually provided for coverage of each domain. At the top level of global DNS, thirteen groups ofroot name serversexist, with additional "copies" of them distributed worldwide viaanycastaddressing.
Dynamic DNS(DDNS) updates a DNS server with a client IP address on-the-fly, for example, when moving between ISPs or mobilehot spots,or when the IP address changes administratively.
DNS message format[edit]
The DNS protocol uses two types of DNS messages, queries and responses; both have the same format. Each message consists of a header and four sections: question, answer, authority, and an additional space. A header field (flags) controls the content of these four sections.[22]
The header section consists of the following fields:Identification,Flags,Number of questions,Number of answers,Number of authority resource records(RRs), andNumber of additional RRs.Each field is 16 bits long, and appears in the order given. The identification field is used to match responses with queries. The flag field consists of sub-fields as follows:
| Field | Description | Length (bits) |
|---|---|---|
| QR | Indicates if the message is a query (0) or a reply (1) | 1 |
| OPCODE | The type can be QUERY (standard query, 0), IQUERY (inverse query, 1), or STATUS (server status request, 2) | 4 |
| AA | Authoritative Answer, in a response, indicates if the DNS server is authoritative for the queried hostname | 1 |
| TC | TrunCation, indicates that this message was truncated due to excessive length | 1 |
| RD | Recursion Desired, indicates if the client means a recursive query | 1 |
| RA | Recursion Available, in a response, indicates if the replying DNS server supports recursion | 1 |
| Z | Zero, reserved for future use | 3 |
| RCODE | Response code, can be NOERROR (0), FORMERR (1, Format error), SERVFAIL (2), NXDOMAIN (3, Nonexistent domain), etc.[37] | 4 |
After the flag, the header ends with four 16-bit integers which contain the number of records in each of the sections that follow, in the same order.
| Offsets | 0 | 1 | 2 | 3 | |||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Octet | Bit | 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 |
| 0 | 0 | Transaction ID | Flags | ||||||||||||||||||||||||||||||
| QR | OPCODE | AA | TC | RD | RA | Z | RCODE | ||||||||||||||||||||||||||
| 4 | 32 | Number of questions | Number of answers | ||||||||||||||||||||||||||||||
| 8 | 64 | Number of authority RRs | Number of additional RRs | ||||||||||||||||||||||||||||||
Question section[edit]
The question section has a simpler format than the resource record format used in the other sections. Each question record (there is usually just one in the section) contains the following fields:
| Field | Description | Length (octets) |
|---|---|---|
| NAME | Name of the requested resource | Variable |
| TYPE | Type of RR (A, AAAA, MX, TXT, etc.) | 2 |
| CLASS | Class code | 2 |
The domain name is broken into discrete labels which are concatenated; each label is prefixed by the length of that label.[38]
Resource records[edit]
The Domain Name System specifies a database of information elements for network resources. The types of information elements are categorized and organized with alist of DNS record types,the resource records (RRs). Each record has a type (name and number), an expiration time (time to live), a class, and type-specific data. Resource records of the same type are described as aresource record set(RRset), having no special ordering. DNS resolvers return the entire set upon query, but servers may implementround-robin orderingto achieveload balancing.In contrast, theDomain Name System Security Extensions(DNSSEC) work on the complete set of resource record in canonical order.
When sent over anInternet Protocolnetwork, all records use the common format specified in RFC 1035:[39]
| Field | Description | Length (octets) |
|---|---|---|
| NAME | Name of the node to which this record pertains | Variable |
| TYPE | Type of RR in numeric form (e.g., 15 for MX RRs) | 2 |
| CLASS | Class code | 2 |
| TTL | Count of seconds that the RR stays valid (The maximum is 231−1, which is about 68 years) | 4 |
| RDLENGTH | Length of RDATA field (specified in octets) | 2 |
| RDATA | Additional RR-specific data | Variable, as per RDLENGTH |
NAMEis the fully qualified domain name of the node in the tree.[clarification needed]On the wire, the name may be shortened using label compression where ends of domain names mentioned earlier in the packet can be substituted for the end of the current domain name.
TYPEis the record type. It indicates the format of the data and it gives a hint of its intended use. For example, theArecord is used to translate from a domain name to anIPv4 address,theNSrecord lists which name servers can answer lookups on aDNS zone,and theMXrecord specifies the mail server used to handle mail for a domain specified in an e-mail address.
RDATAis data of type-specific relevance, such as the IP address for address records, or the priority and hostname for MX records. Well known record types may use label compression in the RDATA field, but "unknown" record types must not (RFC 3597).
TheCLASSof a record is set to IN (forInternet) for common DNS records involving Internet hostnames, servers, or IP addresses. In addition, the classesChaos(CH) andHesiod(HS) exist.[40]Each class is an independent name space with potentially different delegations of DNS zones.
In addition to resource records defined in azone file,the domain name system also defines several request types that are used only in communication with other DNS nodes (on the wire), such as when performing zone transfers (AXFR/IXFR) or forEDNS(OPT).
Wildcard records[edit]
The domain name system supportswildcard DNS recordswhich specify names that start with theasterisk label,*,e.g.,*.example.[22][41]DNS records belonging to wildcard domain names specify rules for generating resource records within a single DNS zone by substituting whole labels with matching components of the query name, including any specified descendants. For example, in the following configuration, the DNS zonex.examplespecifies that all subdomains, including subdomains of subdomains, ofx.exampleuse the mail exchanger (MX)a.x.example.The A record fora.x.exampleis needed to specify the mail exchanger IP address. As this has the result of excluding this domain name and its subdomains from the wildcard matches, an additional MX record for the subdomaina.x.example,as well as a wildcarded MX record for all of its subdomains, must also be defined in the DNS zone.
x.example.MX10a.x.example.
*.x.example.MX10a.x.example.
*.a.x.example.MX10a.x.example.
a.x.example.MX10a.x.example.
a.x.example.AAAA2001:db8::1
The role of wildcard records was refined inRFC4592,because the original definition inRFC1034was incomplete and resulted in misinterpretations by implementers.[41]
Protocol extensions[edit]
The original DNS protocol had limited provisions for extension with new features. In 1999, Paul Vixie published in RFC 2671 (superseded by RFC 6891) an extension mechanism, calledExtension Mechanisms for DNS(EDNS) that introduced optional protocol elements without increasing overhead when not in use. This was accomplished through the OPT pseudo-resource record that only exists in wire transmissions of the protocol, but not in any zone files. Initial extensions were also suggested (EDNS0), such as increasing the DNS message size in UDP datagrams.
Dynamic zone updates[edit]
Dynamic DNS updatesuse the UPDATE DNS opcode to add or remove resource records dynamically from a zone database maintained on an authoritative DNS server.[42]This facility is useful to register network clients into the DNS when they boot or become otherwise available on the network. As a booting client may be assigned a different IP address each time from aDHCPserver, it is not possible to provide static DNS assignments for such clients.
Transport protocols[edit]
From the time of its origin in 1983 the DNS has used theUser Datagram Protocol(UDP) for transport over IP. Its limitations have motivated numerous protocol developments for reliability, security, privacy, and other criteria, in the following decades.
DNS over UDP/TCP/53 (Do53)[edit]
UDP reservesport number53 for servers listening to queries.[5]Such queries consist of a clear-text request sent in a single UDP packet from the client, responded to with a clear-text reply sent in a single UDP packet from the server. When the length of the answer exceeds 512 bytes and both client and server supportExtension Mechanisms for DNS(EDNS), larger UDP packets may be used.[43]Use of DNS over UDP is limited by, among other things, its lack of transport-layer encryption, authentication, reliable delivery, and message length. In 1989, RFC 1123 specified optionalTransmission Control Protocol(TCP) transport for DNS queries, replies and, particularly,zone transfers.Via fragmentation of long replies, TCP allows longer responses, reliable delivery, and re-use of long-lived connections between clients and servers. For larger responses, the server refers the client to TCP transport.
DNS over TLS (DoT)[edit]
DNS over TLSemerged as an IETF standard for encrypted DNS in 2016, utilizing Transport Layer Security (TLS) to protect the entire connection, rather than just the DNS payload. DoT servers listen on TCP port 853.RFC7858specifies that opportunistic encryption and authenticated encryption may be supported, but did not make either server or client authentication mandatory.
DNS over HTTPS (DoH)[edit]
DNS over HTTPSwas developed as a competing standard for DNS query transport in 2018, tunneling DNS query data over HTTPS, which transports HTTP over TLS. DoH was promoted as a more web-friendly alternative to DNS since, like DNSCrypt, it uses TCP port 443, and thus looks similar to web traffic, though they are easily differentiable in practice without proper padding.[44]
DNS over QUIC (DoQ)[edit]
RFC 9250, published in 2022 by theInternet Engineering Task Force,describes DNS overQUIC.It has "privacy properties similar to DNS over TLS (DoT) [...], and latency characteristics similar to classic DNS over UDP". This method is not the same as DNS overHTTP/3.[45]
Oblivious DoH (ODoH) and predecessor Oblivious DNS (ODNS)[edit]
Oblivious DNS (ODNS) was invented and implemented by researchers atPrinceton Universityand theUniversity of Chicagoas an extension to unencrypted DNS,[46]before DoH was standardized and widely deployed. Apple and Cloudflare subsequently deployed the technology in the context of DoH, as Oblivious DoH (ODoH).[47]ODoH combines ingress/egress separation (invented in ODNS) with DoH's HTTPS tunneling and TLS transport-layer encryption in a single protocol.[48]
DNS over Tor[edit]
DNS may be run overvirtual private networks(VPNs) andtunneling protocols.A use which has become common since 2019 to warrant its own frequently used acronym is DNS overTor.The privacy gains of Oblivious DNS can be garnered through the use of the preexisting Tor network of ingress and egress nodes, paired with the transport-layer encryption provided by TLS.[49]
DNSCrypt[edit]
TheDNSCryptprotocol, which was developed in 2011 outside theIETFstandards framework, introduced DNS encryption on the downstream side of recursive resolvers, wherein clients encrypt query payloads using servers' public keys, which are published in the DNS (rather than relying upon third-party certificate authorities) and which may in turn be protected by DNSSEC signatures.[50]DNSCrypt uses either TCP or UDP port 443, the same port as HTTPS encrypted web traffic. This introduced not only privacy regarding the content of the query, but also a significant measure of firewall-traversal capability. In 2019, DNSCrypt was further extended to support an "anonymized" mode, similar to the proposed "Oblivious DNS", in which an ingress node receives a query which has been encrypted with the public key of a different server, and relays it to that server, which acts as an egress node, performing the recursive resolution.[51]Privacy of user/query pairs is created, since the ingress node does not know the content of the query, while the egress nodes does not know the identity of the client. DNSCrypt was first implemented in production byOpenDNSin December 2011. There are several free and open source software implementations that additionally integrate ODoH.[52]It is available for a variety of operating systems, including Unix, Apple iOS, Linux, Android, and MS Windows.
Security issues[edit]
Originally, security concerns were not major design considerations for DNS software or any software for deployment on the early Internet, as the network was not open for participation by the general public. However, the expansion of the Internet into the commercial sector in the 1990s changed the requirements for security measures to protectdata integrityand userauthentication.
Several vulnerability issues were discovered and exploited by malicious users. One such issue isDNS cache poisoning,in which data is distributed to caching resolvers under the pretense of being an authoritative origin server, thereby polluting the data store with potentially false information and long expiration times (time-to-live). Subsequently, legitimate application requests may be redirected to network hosts operated with malicious intent.
DNS responses traditionally do not have acryptographic signature,leading to many attack possibilities; theDomain Name System Security Extensions(DNSSEC) modify DNS to add support for cryptographically signed responses.[53]DNSCurvehas been proposed as an alternative to DNSSEC. Other extensions, such asTSIG,add support for cryptographic authentication between trusted peers and are commonly used to authorize zone transfer or dynamic update operations.
Some domain names may be used to achieve spoofing effects. For example,paypalandpaypa1are different names, yet users may be unable to distinguish them in a graphical user interface depending on the user's chosentypeface.In many fonts the letterland the numeral1look very similar or even identical. This problem, known as theIDN homograph attack,is acute in systems that supportinternationalized domain names,as many character codes inISO 10646may appear identical on typical computer screens. This vulnerability is occasionally exploited inphishing.[54]
Techniques such asforward-confirmed reverse DNScan also be used to help validate DNS results.
DNS can also "leak" from otherwise secure or private connections, if attention is not paid to their configuration, and at times DNS has been used to bypass firewalls by malicious persons, andexfiltratedata, since it is often seen as innocuous.
Privacy and tracking issues[edit]
Originally designed as a public, hierarchical, distributed and heavily cached database, DNS protocol has no confidentiality controls. User queries and nameserver responses are being sent unencrypted which enablesnetwork packet sniffing,DNS hijacking,DNS cache poisoningandman-in-the-middle attacks.This deficiency is commonly used by cybercriminals and network operators for marketing purposes, user authentication oncaptive portalsandcensorship.[55]
User privacy is further exposed by proposals for increasing the level of client IP information in DNS queries (RFC 7871) for the benefit ofContent Delivery Networks.
The main approaches that are in use to counter privacy issues with DNS:
- VPNs,which move DNS resolution to the VPN operator and hide user traffic from local ISP,
- Tor,which replaces traditional DNS resolution with anonymous.oniondomains, hiding both name resolution and user traffic behindonion routingcounter-surveillance,
- Proxiesand public DNS servers, which move the actual DNS resolution to a third-party provider, who usually promises little or no request logging and optional added features, such as DNS-leveladvertisementor pornography blocking.
- Public DNS servers can be queried using traditional DNS protocol, in which case they provide no protection from local surveillance, orDNS over HTTPS,DNS over TLSandDNSCrypt,which do provide such protection
Solutions preventing DNS inspection by local network operator are criticized for thwarting corporate network security policies and Internet censorship. They are also criticized from a privacy point of view, as giving away the DNS resolution to the hands of a small number of companies known for monetizing user traffic and for centralizing DNS name resolution, which is generally perceived as harmful for the Internet.[55]
Google is the dominant provider of the platform inAndroid,the browser in Chrome, and the DNS resolver in the 8.8.8.8 service. Would this scenario be a case of a single corporate entity being in a position of overarching control of the entire namespace of the Internet?Netflixalready fielded an app that used its own DNS resolution mechanism independent of the platform upon which the app was running. What if theFacebookapp included DoH? What ifApple'siOSused a DoH-resolution mechanism to bypass local DNS resolution and steer all DNS queries from Apple's platforms to a set of Apple-operated name resolvers?
— DNS Privacy and the IETF
Domain name registration[edit]
The right to use a domain name is delegated by domain name registrars which are accredited by theInternet Corporation for Assigned Names and Numbers(ICANN) or other organizations such asOpenNIC,that are charged with overseeing the name and number systems of the Internet. In addition to ICANN, each top-level domain (TLD) is maintained and serviced technically by an administrative organization, operating a registry. Aregistryis responsible for operating the database of names within its authoritative zone, although the term is most often used for TLDs. Aregistrantis a person or organization who asked for domain registration.[23]The registry receives registration information from each domain nameregistrar,which is authorized (accredited) to assign names in the corresponding zone and publishes the information using theWHOISprotocol. As of 2015, usage ofRDAPis being considered.[56]
ICANN publishes the complete list of TLDs, TLD registries, and domain name registrars. Registrant information associated with domain names is maintained in an online database accessible with the WHOIS service. For most of the more than 290country code top-level domains(ccTLDs), the domain registries maintain the WHOIS (Registrant, name servers, expiration dates, etc.) information. For instance,DENIC,Germany NIC, holds the DE domain data. From about 2001, mostGeneric top-level domain(gTLD) registries have adopted this so-calledthickregistry approach, i.e. keeping the WHOIS data in central registries instead of registrar databases.
For top-level domains on COM and NET, athinregistry model is used. The domain registry (e.g.,GoDaddy,BigRock and PDR,VeriSign,etc., etc.) holds basic WHOIS data (i.e., registrar and name servers, etc.). Organizations, or registrants using ORG on the other hand, are on thePublic Interest Registryexclusively.
Some domain name registries, often callednetwork information centers(NIC), also function as registrars to end-users, in addition to providing access to the WHOIS datasets. The top-level domain registries, such as for the domains COM, NET, and ORG use a registry-registrar model consisting of many domain name registrars.[57]In this method of management, the registry only manages the domain name database and the relationship with the registrars. Theregistrants(users of a domain name) are customers of the registrar, in some cases through additional subcontracting of resellers.
RFC documents[edit]
The Domain Name System is defined byRequest for Comments(RFC) documents published by theInternet Engineering Task Force(Internet standards). The following is a list of RFCs that define the DNS protocol.
Standards track[edit]
- RFC1034,Domain Names - Concepts and Facilities
- RFC1035,Domain Names - Implementation and Specification
- RFC1123,Requirements for Internet Hosts—Application and Support
- RFC1995,Incremental Zone Transfer in DNS
- RFC1996,A Mechanism for Prompt Notification of Zone Changes (DNS NOTIFY)
- RFC2136,Dynamic Updates in the domain name system (DNS UPDATE)
- RFC2181,Clarifications to the DNS Specification
- RFC2308,Negative Caching of DNS Queries (DNS NCACHE)
- RFC3225,Indicating Resolver Support of DNSSEC
- RFC3226,DNSSEC and IPv6 A6 aware server/resolver message size requirements
- RFC3596,DNS Extensions to Support IP Version 6
- RFC3597,Handling of Unknown DNS Resource Record (RR) Types
- RFC4343,Domain Name System (DNS) Case Insensitivity Clarification
- RFC4592,The Role of Wildcards in the Domain Name System
- RFC4635,HMAC SHA TSIG Algorithm Identifiers
- RFC5001,DNS Name Server Identifier (NSID) Option
- RFC5011,Automated Updates of DNS Security (DNSSEC) Trust Anchors
- RFC5452,Measures for Making DNS More Resilient against Forged Answers
- RFC5890,Internationalized Domain Names for Applications (IDNA):Definitions and Document Framework
- RFC5891,Internationalized Domain Names in Applications (IDNA): Protocol
- RFC5892,The Unicode Code Points and Internationalized Domain Names for Applications (IDNA)
- RFC5893,Right-to-Left Scripts for Internationalized Domain Names for Applications (IDNA)
- RFC6672,Non-Terminal DNS Name Redirection
- RFC6891,Extension Mechanisms for DNS (EDNS0)
- RFC7766,DNS Transport over TCP - Implementation Requirements
- RFC8945,Secret Key Transaction Authentication for DNS (TSIG)
Proposed security standards[edit]
- RFC4033,DNS Security Introduction and Requirements
- RFC4034,Resource Records for the DNS Security Extensions
- RFC4035,Protocol Modifications for the DNS Security Extensions
- RFC4509,Use of SHA-256 in DNSSEC Delegation Signer (DS) Resource Records
- RFC4470,Minimally Covering NSEC Records and DNSSEC On-line Signing
- RFC5155,DNS Security (DNSSEC) Hashed Authenticated Denial of Existence
- RFC5702,Use of SHA-2 Algorithms with RSA in DNSKEY and RRSIG Resource Records for DNSSEC
- RFC5910,Domain Name System (DNS) Security Extensions Mapping for the Extensible Provisioning Protocol (EPP)
- RFC5933,Use of GOST Signature Algorithms in DNSKEY and RRSIG Resource Records for DNSSEC
- RFC7830,The EDNS(0) Padding Option
- RFC7858,Specification for DNS over Transport Layer Security (TLS)
- RFC8310,Usage Profiles for DNS over TLS and DNS over DTLS
- RFC8484,DNS Queries over HTTPS (DoH)
Experimental RFCs[edit]
- RFC1183,New DNS RR Definitions
Best Current Practices[edit]
- RFC2182,Selection and Operation of Secondary DNS Servers(BCP 16)
- RFC2317,Classless IN-ADDR.ARPA delegation(BCP 20)
- RFC5625,DNS Proxy Implementation Guidelines(BCP 152)
- RFC6895,Domain Name System (DNS) IANA Considerations(BCP 42)
- RFC7720,DNS Root Name Service Protocol and Deployment Requirements(BCP 40)
Informational RFCs[edit]
These RFCs are advisory in nature, but may provide useful information despite defining neither a standard or BCP. (RFC 1796)
- RFC1178,Choosing a Name for Your Computer(FYI 5)
- RFC1591,Domain Name System Structure and Delegation
- RFC1912,Common DNS Operational and Configuration Errors
- RFC2100,The Naming of Hosts
- RFC3696,Application Techniques for Checking and Transformation of Names
- RFC3833.Threat Analysis of the Domain Name System (DNS)
- RFC4892,Requirements for a Mechanism Identifying a Name Server Instance
- RFC5894,Internationalized Domain Names for Applications (IDNA):Background, Explanation, and Rationale
- RFC5895,Mapping Characters for Internationalized Domain Names in Applications (IDNA) 2008
- RFC8806,Running a Root Server Local to a Resolver
- RFC9076,DNS Privacy Considerations
- RFC9156,DNS Query Name Minimisation to Improve Privacy
- RFC9499,DNS Terminology
Unknown[edit]
These RFCs have an official status ofUnknown,but due to their age are not clearly labeled as such.
- RFC920,Domain Requirements– Specified original top-level domains
- RFC1032,Domain Administrators Guide
- RFC1033,Domain Administrators Operations Guide
- RFC1101,DNS Encodings of Network Names and Other Types
See also[edit]
- Alternative DNS root
- Comparison of DNS server software
- Decentralized object location and routing
- Domain hijacking
- DNS hijacking
- DNS Long-Lived Queries
- DNS management software
- DNS over HTTPS
- DNS over TLS
- Hierarchical namespace
- IPv6 brokenness and DNS whitelisting
- Multicast DNS
- Public recursive name server
- resolv.conf
- Split-horizon DNS
- List of DNS record types
- List of managed DNS providers
- Zone file
- DNS leak
References[edit]
- ^Wu, Hao; Dang, Xianglei; Wang, Lidong; He, Longtao (2016)."Information fusion-based method for distributed domain name system cache poisoning attack detection and identification".IET Information Security.10(1): 37–44.doi:10.1049/iet-ifs.2014.0386.ISSN1751-8717.S2CID45091791.
- ^RFC 781,Internet Protocol - DARPA Internet Program Protocol Specification,Information Sciences Institute, J. Postel (Ed.), The Internet Society (September 1981)
- ^J. Dilley, B. Maggs, J. Parikh, H. Prokop, R. Sitaraman, and B. Weihl."Globally Distributed Content Delivery, IEEE Internet Computing, September/October 2002, pp. 50–58"(PDF).Archived(PDF)from the original on 2015-04-17.
- ^Nygren., E.; Sitaraman R. K.; Sun, J. (2010)."The Akamai Network: A Platform for High-Performance Internet Applications"(PDF).ACM SIGOPS Operating Systems Review.44(3): 2–19.doi:10.1145/1842733.1842736.S2CID207181702.Archived(PDF)from the original on 2010-12-02.RetrievedNovember 19,2012.
- ^abcdefMockapetris, Paul (November 1987).Domain Names - Implementation and Specification.IETF.doi:10.17487/RFC1035.RFC1035.
- ^Champika Wijayatunga (February 2015)."DNS Abuse Handling"(PDF).APNIC.Archived(PDF)from the original on 2015-12-22.Retrieved18 December2016.
- ^J. Klensin(February 2003).Role of the Domain Name System (DNS).Network Working Group.doi:10.17487/RFC3467.RFC3467.Informational.
- ^Liu, Cricket; Albitz, Paul (2006).DNS and BIND(5th ed.). O'Reilly Media. p. 3.ISBN978-0-596-10057-5.
- ^Evans 2018,p. 112.
- ^Evans 2018,p. 113.
- ^IEEE Annals [3B2-9] man2011030074.3d 29/7/011 11:54 Page 74
- ^ab"Why Does the Net Still Work on Christmas? Paul Mockapetris - Internet Hall of Fame".internethalloffame.org.23 July 2012.
- ^abEvans 2018,p. 119.
- ^Evans 2018,p. 120.
- ^Evans 2018,p. 120–121.
- ^"Elizabeth Feinler".Internet Hall of Fame.Archived fromthe originalon 14 September 2018.Retrieved2018-11-25.
- ^"Paul Mockapetris | Internet Hall of Fame".internethalloffame.org.Retrieved2020-02-12.
- ^Andrei Robachevsky (26 November 2013)."Happy 30th Birthday, DNS!".Internet Society.Retrieved18 December2015.
- ^Elizabeth Feinler, IEEE Annals, 3B2-9 man2011030074.3d 29/7/011 11:54 Page 74
- ^Terry, Douglas B.; et al. (June 12–15, 1984)."The Berkeley Internet Name Domain Server".Summer Conference, Salt Lake City 1984: Proceedings.USENIX Association Software Tools Users Group. pp. 23–31.
- ^Internet Systems Consortium."The History of BIND".History of BIND.Archivedfrom the original on 2019-06-30.Retrieved4 April2022.
- ^abcdeMockapetris, Paul (November 1987).Domain Names - Domain Concepts and Facilities.IETF.doi:10.17487/RFC1034.RFC1034.
- ^abPaul Hoffman; Andrew Sullivan; Kazunori Fujiwara (December 2015).DNS Terminology.IETF.doi:10.17487/RFC7719.RFC7719.Retrieved18 December2015.
- ^Paul Mockapetris (November 1987)."Name space specifications and terminology".Domain Names - Domain Concepts and Facilities.IETF.sec. 3.1.doi:10.17487/RFC1034.RFC1034.Retrieved17 December2015.
- ^abPaul Mockapetris (November 1987)."How the database is divided into zones".Domain Names - Domain Concepts and Facilities.IETF.sec. 4.2.doi:10.17487/RFC1034.RFC1034.Retrieved17 December2015.
- ^Lindsay, David (2007).International Domain Name Law: ICANN and the UDRP.Bloomsbury Publishing. p. 8.ISBN978-1-84113-584-7.
- ^D. Eastlake 3rd (January 2006).Domain Name System (DNS) Case Insensitivity Clarification.Network Working Group.doi:10.17487/RFC4343.RFC4343.
{{citation}}:CS1 maint: numeric names: authors list (link)Proposed Standard.Updated byRFC5890.UpdatesRFC1034,1035and2181. - ^abJ. Klensin(February 2004).Application Techniques for Checking and Transformation of Names.Network Working Group.doi:10.17487/RFC3696.RFC3696.Informational.
- ^Fujiwara, Kazunori; Sullivan, Andrew; Hoffman, Paul (2024)."DNS Terminology".tools.ietf.org.doi:10.17487/RFC9499.Retrieved2024-07-01.
- ^Nemeth, Evi; Snyder, Garth; Hein, Trent R. (2006-10-30).Linux Administration Handbook.Addison-Wesley Professional.ISBN978-0-13-700275-7.
- ^Bissyande, Tegawendé F.; Sie, Oumarou (2017-10-09).e-Infrastructure and e-Services for Developing Countries: 8th International Conference, AFRICOMM 2016, Ouagadougou, Burkina Faso, December 6-7, 2016, Proceedings.Springer.ISBN978-3-319-66742-3.
- ^"DNS zone".IONOS Digitalguide.27 January 2022.Retrieved2022-03-31.
- ^"What is DNS propagation?".IONOS Digitalguide.Retrieved2022-04-22.
- ^"Providers ignoring DNS TTL?".Slashdot.2005.Retrieved2012-04-07.
- ^Ben Anderson (7 September 2011)."Ben Anderson: Why Web Browser DNS Caching Can Be A Bad Thing".Retrieved20 October2014.
- ^"How Internet Explorer uses the cache for DNS host entries".Microsoft Corporation.2004.Retrieved2010-07-25.
- ^"Domain Name System (DNS) Parameters".IANA.DNS RCODEs.Retrieved14 June2019.
- ^James F. Kurose and Keith W. Ross, Computer Networking: A Top-Down Approach, 6th ed. Essex, England: Pearson Educ. Limited, 2012
- ^RFC 5395,Domain Name System (DNS) IANA Considerations,D. Eastlake 3rd (November 2008), Section 3
- ^RFC 5395,Domain Name System (DNS) IANA Considerations,D. Eastlake 3rd (November 2008), p. 11
- ^abRFC4592,The Role of Wildcards in the Domain Name System,E. Lewis (July 2006)
- ^S. Thomson; Y. Rekhter; J. Bound (April 1997).P. Vixie(ed.).Dynamic Updates in the Domain Name System (DNS UPDATE).Network Working Group.doi:10.17487/RFC2136.RFC2136.Proposed Standard.UpdatesRFC1035.Updated byRFC3007,4033,4034and4035.
- ^RFC2671,Extension Mechanisms for DNS (EDNS0),P. Vixie (August 1999)
- ^Csikor, Levente; Divakaran, Dinil Mon (February 2021)."Privacy of DNS over HTTPS: Requiem for a Dream?"(PDF).National University of Singapore.
We investigate whether DoH traffic is distinguishable from encrypted Web traffic. To this end, we train a machine learning model to classify HTTPS traffic as either Web or DoH. With our DoH identification model in place, we show that an authoritarian ISP can identify ≈97.4% of the DoH packets correctly while only misclassifying 1 in 10,000 Web packets.
- ^Huitema, Christian; Dickinson, Sara; Mankin, Allison (May 2022).DNS over Dedicated QUIC Connections.Internet Engineering Task Force.doi:10.17487/RFC9250.RFC9250.
- ^Schmitt, Paul; Edmundson, Anne; Feamster, Nick (2019)."Oblivious DNS: Practical Privacy for DNS Queries"(PDF).Privacy Enhancing Technologies.2019(2): 228–244.arXiv:1806.00276.doi:10.2478/popets-2019-0028.S2CID44126163.Archived(PDF)from the original on 2022-01-21.
- ^"Oblivious DNS Deployed by Cloudflare and Apple".9 December 2020.Retrieved27 July2022.
- ^Pauly, Tommy (2 September 2021)."Oblivious DNS Over HTTPS".IETF.
- ^Muffett, Alec (February 2021).""No Port 53, Who Dis?" A Year of DNS over HTTPS over Tor "(PDF).Network and Distributed System Security Symposium.Archived(PDF)from the original on 2021-03-21.
DNS over HTTPS (DoH) obviates many but not all of the risks, and its transport protocol (i.e. HTTPS) raises concerns of privacy due to (e.g.) 'cookies.' The Tor Network exists to provide TCP circuits with some freedom from tracking, surveillance, and blocking. Thus: In combination with Tor, DoH, and the principle of "Don't Do That, Then" (DDTT) to mitigate request fingerprinting, I describe DNS over HTTPS over Tor (DoHoT).
- ^Ulevitch, David (6 December 2011)."DNSCrypt – Critical, fundamental, and about time".Cisco Umbrella.Archivedfrom the original on 1 July 2020.
- ^"Anonymized DNSCrypt specification".GitHub.DNSCrypt.Archivedfrom the original on 25 October 2019.
- ^"Oblivious DoH · DNSCrypt/dnscrypt-proxy Wiki".GitHub.DNSCrypt project.Retrieved28 July2022.
- ^Herzberg, Amir; Shulman, Haya (2014-01-01)."Retrofitting Security into Network Protocols: The Case of DNSSEC".IEEE Internet Computing.18(1): 66–71.doi:10.1109/MIC.2014.14.ISSN1089-7801.S2CID12230888.
- ^APWG. "Global Phishing Survey: Domain Name Use and Trends in 1H2010."10/15/2010 apwg.orgArchived2012-10-03 at theWayback Machine
- ^abHuston, Geoff (July 2019)."DNS Privacy and the IETF"(PDF).The Internet Protocol Journal.Archived(PDF)from the original on 2019-09-30.
- ^"Registration Data Access Protocol (RDAP) Operational Profile for gTLD Registries and Registrars".ICANN.3 December 2015. Archived fromthe originalon 22 December 2015.Retrieved18 December2015.
- ^"Find a Registrar".VeriSign, Inc.Retrieved18 December2015.
Sources[edit]
- Evans, Claire L. (2018).Broad Band: The Untold Story of the Women Who Made the Internet.New York: Portfolio/Penguin.ISBN9780735211759.
External links[edit]
- Vixie, Paul (2007-05-04)."DNS Complexity".ACM Queue.Archivedfrom the original on 2023-03-29.
- Zytrax,Open Source Guide – DNS for Rocket Scientists.
- Internet Governance and the Domain Name System: Issues for CongressCongressional Research Service
- Ball, James (28 February 2014)."Meet the seven people who hold the keys to worldwide internet security".The Guardian.Guardian News & Media Limited.Retrieved28 February2014.
- Mess with DNS– site where you can do experiments with DNS.
