Tor (network)
 The Tor Projectlogo | |
| Developer(s) | The Tor Project |
|---|---|
| Initial release | September 20, 2002[1] |
| Stable release(s)[±] | |
| 0.4.8.12[2] | |
| Preview release(s)[±] | |
| Repository | |
| Written in | C,[3]Python,Rust[4] |
| Operating system | Unix-like,(Android,Linux,BSD,macOS),Microsoft Windows,iOS |
| Size | 50–55 MB |
| Type | Overlay network,mix network,onion router,Anonymity application |
| License | BSD 3-clause license[5] |
| Website | torproject |
| Part ofa serieson |
| File sharing |
|---|
 |
Tor[6]is a freeoverlay networkfor enablinganonymous communication.Built onfree and open-source softwareand more than seven thousand volunteer-operated relays worldwide, users can have theirInternet trafficrouted via a random path through the network.[7][8]
Using Tor makes it more difficult to trace a user'sInternetactivity by preventing any single point on the Internet (other than the user's device) from being able to view both where traffic originated from and where it is ultimately going to at the same time.[9]This conceals a user's location and usage from anyone performingnetwork surveillanceortraffic analysisfrom any such point, protecting the user's freedom and ability to communicate confidentially.[10]
History
[edit]The core principle of Tor, known asonion routing,was developed in the mid-1990s byUnited States Naval Research Laboratoryemployees,mathematicianPaul Syverson,andcomputer scientistsMichael G. Reed and David Goldschlag, to protectAmerican intelligencecommunications online.[11]Onion routing is implemented by means ofencryptionin theapplication layerof thecommunication protocolstack, nested like the layers of anonion.TheAlpha versionof Tor, developed by Syverson and computer scientistsRoger DingledineandNick Mathewsonand then called The Onion Routing project (which was later given the acronym "Tor" ), was launched on 20 September 2002.[12][13]The first public release occurred a year later.[14]
In 2004, the Naval Research Laboratory released the code for Tor under a free license, and theElectronic Frontier Foundation(EFF) began funding Dingledine and Mathewson to continue its development.[12]In 2006, Dingledine, Mathewson, and five others foundedThe Tor Project,aMassachusetts-based501(c)(3)research-educationnonprofit organizationresponsible for maintaining Tor. The EFF acted as The Tor Project'sfiscal sponsorin its early years, and early financial supporters included the U.S.Bureau of Democracy, Human Rights, and LaborandInternational Broadcasting Bureau,Internews,Human Rights Watch,theUniversity of Cambridge,Google,and Netherlands-basedStichting NLnet.[15][16]

Over the course of its existence, various Torweaknesseshave been discovered and occasionally exploited. Attacks against Tor are an active area of academic research[17][18]that is welcomed by The Tor Project itself.[19]
Usage
[edit]| Category | Percentage |
|---|---|
| Gambling | |
| Gun | |
| Chat | |
| New (not yet indexed) |
|
| Abuse | |
| Books | |
| Directory | |
| Blog | |
| Porn | |
| Hosting | |
| Hacking | |
| Search | |
| Anonymity | |
| Forum | |
| Counterfeit | |
| Whistleblower | |
| Wiki | |
| Bitcoin | |
| Fraud | |
| Market | |
| Drugs |
| Category | % of total | % of active |
|---|---|---|
| Violence | ||
| Arms | ||
| Illicit Social | ||
| Hacking | ||
| Illicit links | ||
| Illicit pornography | ||
| Extremism | ||
| Illicit Other | ||
| Illicit Finance | ||
| Illicit Drugs | ||
| Non-illicit+Unknown | ||
| Illicit total | ||
| Inactive | ||
| Active |
Tor enables its users to surf the Internet, chat and send instant messagesanonymously,and is used by a wide variety of people for bothlicitand illicit purposes.[23]Tor has, for example, been used by criminal enterprises,hacktivismgroups, and law enforcement agencies at cross purposes, sometimes simultaneously;[24][25]likewise, agencies within the U.S. government variously fund Tor (theU.S. State Department,the National Science Foundation, and – through the Broadcasting Board of Governors, which itself partially funded Tor until October 2012 –Radio Free Asia) and seek to subvert it.[26][11]Tor was one of a dozen circumvention tools evaluated by aFreedom House-funded report based on user experience from China in 2010, which includeUltrasurf,Hotspot Shield,andFreegate.[27]
Tor is not meant to completely solve the issue ofanonymityon the web. Tor is not designed to completely erase tracking but instead to reduce the likelihood for sites to trace actions and data back to the user.[28]
Tor is also used for illegal activities. These can include privacy protection or censorship circumvention,[29]as well as distribution of child abuse content, drug sales, or malware distribution.[30]
Tor has been described byThe Economist,in relation toBitcoinandSilk Road,as being "a dark corner of the web".[31]It has been targeted by the AmericanNational Security Agencyand the BritishGCHQsignals intelligenceagencies, albeit with marginal success,[26]and more successfully by the BritishNational Crime Agencyin its Operation Notarise.[32]At the same time, GCHQ has been using a tool named "Shadowcat" for "end-to-end encrypted access to VPS over SSH using the Tor network".[33][34]Tor can be used for anonymous defamation, unauthorizednews leaksof sensitive information,copyright infringement,distribution of illegal sexual content,[35][36][37]sellingcontrolled substances,[38]weapons, and stolen credit card numbers,[39]money laundering,[40]bank fraud,[41]credit card fraud,identity theftand the exchange ofcounterfeit currency;[42]theblack marketutilizes the Tor infrastructure, at least in part, in conjunction with Bitcoin.[24]It has also been used to brickIoTdevices.[43]
In its complaint againstRoss William UlbrichtofSilk Road,the USFederal Bureau of Investigationacknowledged that Tor has "known legitimate uses".[44][45]According toCNET,Tor's anonymity function is "endorsed by theElectronic Frontier Foundation(EFF) and other civil liberties groups as a method forwhistleblowersand human rights workers to communicate with journalists ".[46]EFF's Surveillance Self-Defense guide includes a description of where Tor fits in a larger strategy for protecting privacy and anonymity.[47]
In 2014, the EFF'sEva GalperintoldBusinessweekthat "Tor's biggest problem is press. No one hears about that time someone wasn'tstalkedby their abuser. They hear how somebody got away with downloading child porn. "[48]
The Tor Project states that Tor users include "normal people" who wish to keep their Internet activities private from websites and advertisers, people concerned about cyber-spying, and users who are evading censorship such as activists, journalists, and military professionals. In November 2013, Tor had about four million users.[49]According to theWall Street Journal,in 2012 about 14% of Tor's traffic connected from the United States, with people in "Internet-censoring countries" as its second-largest user base.[50]Tor is increasingly used by victims ofdomestic violenceand thesocial workersand agencies that assist them, even though shelter workers may or may not have had professional training on cyber-security matters.[51]Properly deployed, however, it precludes digital stalking, which has increased due to the prevalence of digital media in contemporaryonlinelife.[52]Along withSecureDrop,Tor is used by news organizations such asThe Guardian,The New Yorker,ProPublicaandThe Interceptto protect the privacy of whistleblowers.[53]
In March 2015, theParliamentary Office of Science and Technologyreleased a briefing which stated that "There is widespread agreement that banning online anonymity systems altogether is not seen as an acceptable policy option in the U.K." and that "Even if it were, there would be technical challenges." The report further noted that Tor "plays only a minor role in the online viewing and distribution of indecent images of children" (due in part to its inherent latency); its usage by theInternet Watch Foundation,the utility of its onion services forwhistleblowers,and its circumvention of theGreat Firewallof China were touted.[54]
Tor's executive director, Andrew Lewman, also said in August 2014 that agents of the NSA and the GCHQ have anonymously provided Tor with bug reports.[55]
The Tor Project's FAQ offers supporting reasons for the EFF's endorsement:
Criminals can already do bad things. Since they're willing to break laws, they already have lots of options available that provide better privacy than Tor provides...
Tor aims to provide protection for ordinary people who want to follow the law. Only criminals have privacy right now, and we need to fix that...
So yes, criminals could in theory use Tor, but they already have better options, and it seems unlikely that taking Tor away from the world will stop them from doing their bad things. At the same time, Tor and other privacy measures can fight identity theft, physical crimes like stalking, and so on.
— Tor Project FAQ[56]
Operation
[edit]Tor aims to conceal its users' identities and their online activity from surveillance and traffic analysis by separating identification and routing. It is an implementation ofonion routing,which encrypts and then randomly bounces communications through a network of relays run by volunteers around the globe. These onion routers employencryptionin a multi-layered manner (hence the onion metaphor) to ensureperfect forward secrecybetween relays, thereby providing users with anonymity in a network location. That anonymity extends to the hosting of censorship-resistant content by Tor's anonymous onion service feature.[7]Furthermore, by keeping some of the entry relays (bridge relays) secret, users can evadeInternet censorshipthat relies upon blocking public Tor relays.[57]
Because theIP addressof the sender and the recipient are notbothincleartextat any hop along the way, anyone eavesdropping at any point along the communication channel cannot directly identify both ends. Furthermore, to the recipient, it appears that the last Tornode(called the exit node), rather than the sender, is the originator of the communication.
Originating traffic
[edit]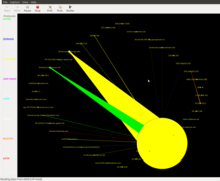
A Tor user'sSOCKS-aware applications can be configured to direct their network traffic through a Tor instance's SOCKS interface, which is listening on TCP port 9050 (for standalone Tor) or 9150 (for Tor Browser bundle) atlocalhost.[58]Tor periodically creates virtual circuits through the Tor network through which it canmultiplexand onion-route that traffic to its destination. Once inside a Tor network, the traffic is sent from router to router along the circuit, ultimately reaching an exit node at which point thecleartextpacket is available and is forwarded on to its original destination. Viewed from the destination, the traffic appears to originate at the Tor exit node.
Tor's application independence sets it apart from most other anonymity networks: it works at theTransmission Control Protocol(TCP) stream level. Applications whose traffic is commonly anonymized using Tor includeInternet Relay Chat(IRC),instant messaging,andWorld Wide Webbrowsing.
Onion services
[edit]Tor can also provide anonymity to websites and other servers. Servers configured to receive inbound connections only through Tor are calledonion services(formerly,hidden services).[59]Rather than revealing a server's IP address (and thus its network location), an onion service is accessed through itsonion address,usually via theTor Browser.The Tor network understands these addresses by looking up their correspondingpublic keysandintroduction pointsfrom adistributed hash tablewithin the network. It can route data to and from onion services, even those hosted behindfirewallsornetwork address translators(NAT), while preserving the anonymity of both parties. Tor is necessary to access these onion services.[60]
Onion services were first specified in 2003[61]and have been deployed on the Tor network since 2004.[62]Other than the database that stores the onion service descriptors,[63]Tor is decentralized by design; there is no direct readable list of all onion services, although a number of onion services catalog publicly known onion addresses.[citation needed]TorSearch is an internetsearch enginethat indexes pages to help find content in websites located on the Tor network.[64]
Because onion services route their traffic entirely through the Tor network, connection to an onion service is encrypted end-to-end and not subject to eavesdropping. There are, however, security issues involving Tor onion services. For example, services that are reachable through Tor onion servicesandthe public Internet are susceptible to correlation attacks and thus not perfectly hidden. Other pitfalls include misconfigured services (e.g. identifying information included by default in web server error responses), uptime and downtime statistics, intersection attacks, and user error.[63][65]Theopen sourceOnionScan program, written by independent security researcherSarah Jamie Lewis,comprehensively examines onion services for numerous flaws and vulnerabilities.[66]
Onion services can also be accessed from a standard web browser withoutclient-sideconnection to the Tor network, using services likeTor2web.[67]Popular sources of.onionlinks includePastebin,Twitter,Reddit,and otherInternet forums.[68]
Weaknesses
[edit]This section needs to beupdated.(September 2020) |
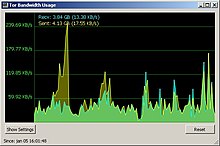
Like all currentlow-latencyanonymity networks,Tor cannot and does not attempt to protect against monitoring of traffic at the boundaries of the Tor network (i.e., the traffic entering and exiting the network). While Tor does provide protection againsttraffic analysis,it cannot prevent traffic confirmation (also calledend-to-end correlation).[69][70]
A 2009 study ofRegensburg Universityrevealed that Tor and the alternative network systemJonDonym(Java Anon Proxy, JAP) are considered more resilient to website fingerprinting techniques than othertunneling protocols.[71]
The reason for this is that conventional single-hopVPNprotocols do not need to reconstruct packet data nearly as much as a multi-hop service like Tor or JonDonym. Website fingerprinting yielded greater than 90% accuracy for identifyingHTTPpackets on conventional VPN protocols versus Tor which yielded only 2.96% accuracy. However, some protocols likeOpenSSHandOpenVPNrequired a large amount of data before HTTP packets were identified.[72]
Researchers from theUniversity of Michigandeveloped a network scanner allowing the identification of 86% of live Tor "bridges" with a single scan.[73]
Consensus blocking
[edit]Like many decentralized systems, Tor relies on aconsensus mechanismto periodically update its current operating parameters, which for Tor are network parameters like which nodes are good/bad relays, exits, guards, and how much traffic each can handle. Tor's architecture for deciding the consensus relies on a small number of directory authority nodes voting on current network parameters. Currently, there are eight directory authority nodes, and their health is publicly monitored.[74]The IP addresses of the authority nodes arehard codedinto each Tor client. The authority nodes vote every hour to update the consensus, and clients download the most recent consensus on startup.[75][76][77]A network congestion attack, such as aDDoS,can prevent the consensus nodes from communicating and thus prevent voting to update the consensus.[citation needed]
Eavesdropping
[edit]Autonomous system (AS) eavesdropping
[edit]If the sameautonomous system(AS), responsible for routing packets at least partly, is present on both path segments from a client to entry relay and from exit relay to destination, such an AS can statistically correlate traffic on the entry and exit segments of the path (i.e. traffic confirmation) and potentially infer the destination with which the client communicated. In 2012, LASTor proposed a method to predict a set of potential ASes on these two segments and then avoid choosing this path during the path selection algorithm on the client side. In this paper, they also improve latency by choosing shorter geographical paths between a client and destination.[78]
Exit node eavesdropping
[edit]In September 2007, Dan Egerstad, a Swedish security consultant, revealed he had intercepted usernames and passwords for email accounts by operating and monitoring Tor exit nodes.[79]As Tor cannot encrypt the traffic between an exit node and the target server, any exit node is in a position to capture traffic passing through it that does not useend-to-end encryptionsuch asSecure Sockets Layer(SSL) orTransport Layer Security(TLS). While this may not inherently breach the anonymity of the source, traffic intercepted in this way by malicious Tor exit nodes operators can expose information about the source in either or both of payload and protocol data.[80]Furthermore, Egerstad is circumspect about the possible subversion of Tor by intelligence agencies:[81]
If you actually look into where these Tor nodes are hosted and how big they are, some of these nodes cost thousands of dollars each month just to host because they're using lots of bandwidth, they're heavy-duty servers and so on. Who would pay for this and be anonymous?
In October 2019, a Tor researcher revealed that since at least 2017, there were hundreds of highly suspicious entry, relay, and exit nodes, run by an unknown group, in an unprecedented scale.[82][83][84]It was alleged that this number of servers could pose the risk of asybil attackas it could map Tor users' routes inside the network, increasing risk of deanonymization.[85][82][83]At some point there were about 900 nodes running and by November 2021 about 600 of them were purged.[86][82][83] Although described as being a deanonymization attempt, the motives and the achievements of this possibly on-going event are still unknown.[82][83]
Internal communication attack
[edit]In October 2011, a research team fromESIEAclaimed to have discovered a way to compromise the Tor network by decrypting communication passing over it.[87][88]The technique they describe requires creating a map of Tor network nodes, controlling one-third of them, and then acquiring their encryptionkeysand algorithmseeds.Then, using these known keys and seeds, they claim the ability to decrypt two encryption layers out of three. They claim to break the third key by a statistical attack. In order to redirect Tor traffic to the nodes they controlled, they used adenial-of-serviceattack. A response to this claim has been published on the official Tor Blog stating these rumors of Tor's compromise are greatly exaggerated.[89]
Traffic-analysis attack
[edit]There are two methods of traffic-analysis attack, passive and active. In the passive traffic-analysis method, the attacker extracts features from the traffic of a specific flow on one side of the network and looks for those features on the other side of the network. In the active traffic-analysis method, the attacker alters the timings of the packets of a flow according to a specific pattern and looks for that pattern on the other side of the network; therefore, the attacker can link the flows on one side to the other side of the network and break the anonymity of it.[failed verification][90]It is shown that, although timing noise is added to the packets, there are active traffic analysis methods that are robust against such a noise.[verification needed][90]
Steven Murdochand George Danezis from theUniversity of Cambridgepresented an article at the 2005IEEESymposiumon security and privacy on traffic-analysis techniques that allow adversaries with only a partial view of the network to infer which nodes are being used to relay the anonymous streams.[91]These techniques greatly reduce the anonymity provided by Tor. Murdoch and Danezis have also shown that otherwise unrelated streams can be linked back to the same initiator. This attack, however, fails to reveal the identity of the original user.[91]Murdoch has been working with and has been funded by Tor since 2006.[citation needed]
Tor exit node block
[edit]Operators of Internet sites have the ability to prevent traffic from Tor exit nodes or to offer reduced functionality for Tor users. For example, it is not generally possible to editWikipediawhen using Tor or when using an IP address also used by a Tor exit node. TheBBCblocks the IP addresses of all known Tor exit nodes from itsiPlayerservice, although non-exit relays and bridges are not blocked.[92]
Bad apple attack
[edit]In March 2011, researchers with the RocquencourtFrench Institute for Research in Computer Science and Automation(Institut national de recherche en informatique et en automatique,INRIA), documented an attack that is capable of revealing the IP addresses ofBitTorrentusers on the Tor network. The "bad apple attack" exploits Tor's design and takes advantage of insecure application used to associate the simultaneous use of a secure application with the IP address of the Tor user in question. One method of attack depends on control of an exit node or hijacking tracker responses, while a secondary attack method is based in part on the statistical exploitation ofdistributed hash tabletracking.[93]According to the study:[93]
The results presented in the bad apple attack research paper are based on an attack launched against the Tor network by the authors of the study. The attack targeted six exit nodes, lasted for twenty-three days, and revealed a total of 10,000 IP addresses of active Tor users. This study is significant because it is the first documented attack designed to targetP2Pfile-sharing applications on Tor.[93]BitTorrent may generate as much as 40% of all traffic on Tor.[94]Furthermore, the bad apple attack is effective against insecure use of any application over Tor, not just BitTorrent.[93]
Sniper attack
[edit]Jansenet al.,describe aDDoSattack targeted at the Tor node software, as well as defenses against that attack and its variants. The attack works using a colluding client and server, and filling the queues of the exit node until the node runs out of memory, and hence can serve no other (genuine) clients. By attacking a significant proportion of the exit nodes this way, an attacker can degrade the network and increase the chance of targets using nodes controlled by the attacker.[95]
Heartbleed bug
[edit]TheHeartbleedOpenSSLbugdisrupted the Tor network for several days in April 2014 whileprivate keyswere renewed. The Tor Project recommended Tor relay operators and onion service operators revoke and generate fresh keys after patching OpenSSL, but noted Tor relays use two sets of keys and Tor's multi-hop design minimizes the impact of exploiting a single relay.[96]Five hundred eighty-six relays, later found to be susceptible to the Heartbleed bug, were taken offline as a precautionary measure.[97][98][99][100]
Relay early traffic confirmation attack
[edit]On 30 July 2014, the Tor Project issued the security advisory "relay early traffic confirmation attack" in which the project discovered a group of relays that tried to de-anonymize onion service users and operators.[101]In summary, the attacking onion service directory node changed the headers of cells being relayed tagging them as "relay" or "relay early" cells differently to encode additional information and sent them back to the requesting user/operator. If the user's/operator's guard/entry node was also part of the attacking relays, the attacking relays might be able to capture the IP address of the user/operator along with the onion service information that the user/operator was requesting. The attacking relays were stable enough to be designated as "suitable as hidden service directory" and "suitable as entry guard"; therefore, both the onion service users and the onion services might have used those relays as guards and hidden service directory nodes.[102]
The attacking nodes joined the network early in the year on 30 January and the project removed them on 4 July.[102]Although the attack's beginning is unclear, the project implied that between February and July, IP addresses of onion service users and operators might have been exposed.[103]
The project mentioned the following mitigations besides removing the attacking relays from the network:
- patched relay software to prevent relays from relaying cells with "relay early" headers that were not intended.[104]
- planned update for users' proxy software so that they could inspect if they received "relay early" cells from the relays (as they are not supposed to),[105]along with the settings to connect to just one guard node instead of selecting randomly from 3 to reduce the probability of connecting to an attacking relay[106]
- recommended that onion services should consider changing their locations[107]
- reminded users and onion service operators that Tor could not prevent de-anonymization if the attacker controlled or could listen to both ends of the Tor circuit, like in this attack.[108]
In November 2014 there was speculation in the aftermath ofOperation Onymous,resulting in 17 arrests internationally, that a Tor weakness had been exploited. A representative ofEuropolwas secretive about the method used, saying: "This is something we want to keep for ourselves. The way we do this, we can't share with the whole world, because we want to do it again and again and again."[109] ABBCsource cited a "technical breakthrough"[110] that allowed tracking physical locations of servers, and the initial number of infiltrated sites led to the exploit speculation. Andrew Lewman—a Tor Project representative—downplayed this possibility, suggesting that execution of more traditional police work was more likely.[111][112]
In November 2015 court documents on the matter[113] addressed concerns about security research ethics[114][non-primary source needed]and the right of not being unreasonably searched as guaranteed by the USFourth Amendment.[115][unreliable source?]Moreover, the documents, along with expert opinions,[who?]may also show the connection between the network attack and the law enforcement operation including:
- the search warrant for an administrator of Silkroad 2.0 indicated that from January 2014 until July, the FBI received information from a "university-based research institute" with the information being "reliable IP addresses for Tor and onion services such as SR2" that led to the identification of "at least another seventeen black markets on Tor" and "approximately 78 IP addresses that accessed a vendor.onionaddress. "One of these IP addresses led to the arrest of the administrator[113]
- the chronology and nature of the attack fitted well with the operation[113]
- a senior researcher ofInternational Computer Science Institute,part ofUniversity of California, Berkeley,said in an interview that the institute which worked with the FBI was "almost certainly"Carnegie Mellon University(CMU),[113]and this concurred with the Tor Project's assessment[114]and with an earlier analysis ofEdward Felten,a computer security professor atPrinceton University,about researchers from CMU'sCERT/CCbeing involved[116]
In his analysis published on 31 July, besides raising ethical issues, Felten also questioned the fulfillment of CERT/CC's purposes which were to prevent attacks, inform the implementers of vulnerabilities, and eventually inform the public. Because in this case, CERT/CC's staff did the opposite which was to carry out a large-scale long-lasting attack, withhold vulnerability information from the implementers, and withhold the same information from the public.[116][unreliable source?]CERT/CC is a non-profit, computer security research organizationpublicly fundedthrough theUS federal government.[citation needed][117]
Mouse fingerprinting
[edit]In March 2016, a security researcher based inBarcelonademonstrated laboratory techniques using time measurement viaJavaScriptat the 1-millisecondlevel[118]which could potentially identify and correlate a user's uniquemousemovements, provided the user has visited the same "fingerprinting" website with both the Tor browser and a regular browser.[citation needed]Thisproof of conceptexploits the "time measurement via JavaScript" issue, which had been an open ticket on the Tor Project for ten months.[119]
Circuit fingerprinting attack
[edit]In 2015, the administrators ofAgora,adarknet market,announced they were taking the site offline in response to a recently discovered security vulnerability in Tor. They did not say what the vulnerability was, butWiredspeculated it was the "Circuit Fingerprinting Attack" presented at theUSENIXsecurity conference.[120][121]
Volume information
[edit]A study showed "anonymization solutions protect only partially against target selection that may lead to efficient surveillance" as they typically "do not hide the volume information necessary to do target selection".[122]
Implementations
[edit]The main implementation of Tor is written primarily inC.[123]
Tor Browser
[edit] Tor Browser showing its start page – about:tor | |
| Developer(s) | Tor Project |
|---|---|
| Stable release(s) | |
| Repository | gitweb |
| Engine | Gecko |
| Operating system |
|
| Size | 90–165 MB |
| Available in | 37 languages[125] |
| Type | Onion routing,anonymity,web browser,feed reader |
| License | Mozilla Public License[126] |
| Website | torproject |
The Tor Browser[127]is aweb browsercapable of accessing the Tor network. It was created as the Tor Browser Bundle bySteven J. Murdoch[128]and announced in January 2008.[129]The Tor Browser consists of a modified MozillaFirefoxESR web browser, the TorButton, TorLauncher,NoScriptand the Tor proxy.[130][131]Users can run the Tor Browser fromremovable media.It can operate underMicrosoft Windows,macOS,AndroidandLinux.[132]
The defaultsearch engineisDuckDuckGo(until version 4.5,Startpagewas its default). The Tor Browser automatically starts Tor background processes and routes traffic through the Tor network. Upon termination of a session the browser deletes privacy-sensitive data such as HTTP cookies and the browsing history.[131]This is effective in reducingweb trackingandcanvas fingerprinting,and it also helps to prevent creation of afilter bubble.[citation needed]
To allow download from places where accessing the Tor Project URL may be risky or blocked, aGitHubrepository is maintained with links for releases hosted in other domains.[133]
Firefox/Tor browser attack
[edit]In 2011, theDutch authorityinvestigatingchild pornographydiscovered the IP address of a Tor onion service site called "Pedoboard" from an unprotected administrator's account and gave it to theFBI,who traced it to Aaron McGrath.[134]After a year of surveillance, the FBI launched "Operation Torpedo"which resulted in McGrath's arrest and allowed them to install theirNetwork Investigative Technique(NIT) malware on the servers for retrieving information from the users of the three onion service sites that McGrath controlled.[135]The technique, exploiting a Firefox/Tor browser's vulnerability that had been patched and targeting users that had not updated, had aFlashapplication pinging a user's IP address directly back to an FBI server,[136][137][138][139]and resulted in revealing at least 25 US users as well as numerous users from other countries.[140]McGrath was sentenced to 20 years in prison in early 2014, with at least 18 other users including a former ActingHHSCyber Security Director being sentenced in subsequent cases.[141][142]
In August 2013, it was discovered[143][144]that theFirefoxbrowsers in many older versions of the Tor Browser Bundle were vulnerable to a JavaScript-deployedshellcodeattack, as NoScript was not enabled by default.[145]Attackers used this vulnerability to extract users' MAC and IP addresses and Windows computer names.[146][147][148]News reports linked this to a FBI operation targetingFreedom Hosting's owner, Eric Eoin Marques, who was arrested on a provisionalextraditionwarrant issued by a United States' court on 29 July.[149]The FBI extradited Marques from Ireland to the state of Maryland on 4 charges: distributing; conspiring to distribute; and advertising child pornography, as well as aiding and abetting advertising of child pornography.[150]The warrant alleged that Marques was "the largest facilitator of child porn on the planet".[151][152][need quotation to verify]The FBI acknowledged the attack in a 12 September 2013 court filing inDublin;[153]further technical details from a training presentation leaked byEdward Snowdenrevealed the code name for the exploit as "EgotisticalGiraffe".[154]
In 2022,Kasperskyresearchers found that when looking up "Tor Browser" in Chinese onYouTube,one of theURLsprovided under the top-ranked Chinese-language video actually pointed to a malware disguised as Tor Browser. Once installed, it saves browsing history and form data that genuine Tor forgot by default, and even downloads malicious components to computers with IP addresses in China. Kaspersky researchers noted that the malware was not stealing data to sell for profit, but was designed to identify users.[155]
Tor Messenger
[edit] | |
| Developer(s) | The Tor Project |
|---|---|
| Initial release | 29 October 2015[156] |
| Final release | |
| Repository | https://gitweb.torproject.org/tor-messenger-build.git |
| Written in | C/C++,JavaScript,CSS,XUL |
| Operating system |
|
| Available in | English |
| Website | trac |
On 29 October 2015, the Tor Project released Tor Messenger Beta, an instant messaging program based onInstantbirdwith Tor andOTRbuilt in and used by default.[156]LikePidginandAdium,Tor Messenger supports multiple different instant messaging protocols; however, it accomplishes this without relying onlibpurple,implementing all chat protocols in the memory-safe language JavaScript instead.[159][160]
According to Lucian Armasu of Toms Hardware, in April 2018, the Tor Project shut down the Tor Messenger project for three reasons: the developers of "Instabird" [sic] discontinued support for their own software, limited resources and known metadata problems.[161]The Tor Messenger developers explained that overcoming any vulnerabilities discovered in the future would be impossible due to the project relying on outdated software dependencies.[162]
Tor Phone
[edit]In 2016, Tor developer Mike Perry announced a prototype tor-enabled smartphone bases onCopperheadOS.[163][164]It was meant as a direction for Tor on mobile.[165]The project was called 'Mission Improbable'. Copperhead's then lead developer Daniel Micay welcomed the prototype.[166]
Third-party applications
[edit]TheVuze(formerly Azureus)BitTorrentclient,[167]Bitmessageanonymous messaging system,[168]andTorChatinstant messenger include Tor support. TheBriarmessenger routes all messaging via Tor by default.OnionShareallows users to share files using Tor.[169]
The Guardian Projectis actively developing a free and open-source suite of applications and firmware for theAndroid operating systemto improve the security of mobile communications.[170]The applications include theChatSecureinstant messaging client,[171]OrbotTor implementation[172](also available for iOS),[173]Orweb (discontinued) privacy-enhanced mobile browser,[174][175]Orfox, the mobile counterpart of the Tor Browser, ProxyMobFirefox add-on,[176]and ObscuraCam.[177]
Onion Browser[178]is open-source, privacy-enhancing web browser foriOS,which uses Tor.[179]It is available in the iOSApp Store,[180]and source code is available onGitHub.[181]
Braveadded support forTorin its desktop browser'sprivate-browsingmode.[182][183]
-
Orbot logo
-
Orbot 16.6.3, running underSamsung Internet
-
Onion Browser oniPad
Security-focused operating systems
[edit]Severalsecurity-focused operating systemsmake or made extensive use of Tor. These includeHardened Linux From Scratch,Incognito,Liberté Linux,Qubes OS,Subgraph,Parrot OS,Tails,Tor-ramdisk, andWhonix.[184]
Reception, impact, and legislation
[edit]Tor has been praised for providing privacy and anonymity to vulnerable Internet users such as political activists fearing surveillance and arrest, ordinary web users seeking to circumvent censorship, and people who have been threatened with violence or abuse by stalkers.[186][187]The U.S. National Security Agency (NSA) has called Tor "the king of high-secure, low-latency Internet anonymity",[26]andBusinessWeekmagazine has described it as "perhaps the most effective means of defeating the online surveillance efforts of intelligence agencies around the world".[11]Other media have described Tor as "a sophisticated privacy tool",[188]"easy to use"[189]and "so secure that even the world's most sophisticated electronic spies haven't figured out how to crack it".[48]
Advocates for Tor say it supportsfreedom of expression,including in countries where the Internet is censored, by protecting the privacy and anonymity of users. The mathematical underpinnings of Tor lead it to be characterized as acting "like a piece ofinfrastructure,and governments naturally fall into paying for infrastructure they want to use ".[190]
The project was originally developed on behalf of the U.S. intelligence community and continues to receive U.S. government funding, and has been criticized as "more resembl[ing] a spook project than a tool designed by a culture that values accountability or transparency".[191]As of 2012[update],80% of The Tor Project's $2M annual budget came from theUnited States government,with theU.S. State Department,theBroadcasting Board of Governors,and theNational Science Foundationas major contributors,[192]aiming "to aid democracy advocates in authoritarian states".[193]Other public sources of funding includeDARPA,theU.S. Naval Research Laboratory,and theGovernment of Sweden.[194][195]Some have proposed that the government values Tor's commitment to free speech, and uses the darknet to gather intelligence.[196][need quotation to verify]Tor also receives funding fromNGOsincludingHuman Rights Watch,and private sponsors includingRedditandGoogle.[197]Dingledine said that theUnited States Department of Defensefunds are more similar to aresearch grantthan aprocurement contract.Tor executive director Andrew Lewman said that even though it accepts funds from the U.S. federal government, the Tor service did not collaborate with the NSA to reveal identities of users.[198]
Critics say that Tor is not as secure as it claims,[199]pointing to U.S. law enforcement's investigations and shutdowns of Tor-using sites such as web-hosting companyFreedom Hostingand online marketplaceSilk Road.[191]In October 2013, after analyzing documents leaked by Edward Snowden,The Guardianreported that the NSA had repeatedly tried to crack Tor and had failed to break its core security, although it had had some success attacking the computers of individual Tor users.[26]The Guardianalso published a 2012 NSA classified slide deck, entitled "Tor Stinks", which said: "We will never be able to de-anonymize all Tor users all the time", but "with manual analysis we can de-anonymize a very small fraction of Tor users".[200]When Tor users are arrested, it is typically due to human error, not to the core technology being hacked or cracked.[201]On 7 November 2014, for example, a joint operation by the FBI, ICE Homeland Security investigations and European Law enforcement agencies led to 17 arrests and the seizure of 27 sites containing 400 pages.[202][dubious–discuss]A late 2014 report byDer Spiegelusing a new cache of Snowden leaks revealed, however, that as of 2012[update]the NSA deemed Tor on its own as a "major threat" to its mission, and when used in conjunction with other privacy tools such asOTR,Cspace,ZRTP,RedPhone,Tails,andTrueCryptwas ranked as "catastrophic," leading to a "near-total loss/lack of insight to target communications, presence..."[203][204]
2011
[edit]In March 2011, The Tor Project received theFree Software Foundation's 2010 Award for Projects of Social Benefit. The citation read, "Using free software, Tor has enabled roughly 36 million people around the world to experience freedom of access and expression on the Internet while keeping them in control of their privacy and anonymity. Its network has proved pivotal in dissident movements in bothIranand more recentlyEgypt."[205]
Iran tried to block Tor at least twice in 2011. One attempt simply blocked all servers with 2-hour-expiry security certificates; it was successful for less than 24 hours.[206][207]
2012
[edit]In 2012,Foreign Policymagazine named Dingledine, Mathewson, and Syverson among its Top 100 Global Thinkers "for making the web safe for whistleblowers".[208]
2013
[edit]In 2013,Jacob Appelbaumdescribed Tor as a "part of an ecosystem of software that helps people regain and reclaim their autonomy. It helps to enable people to have agency of all kinds; it helps others to help each other and it helps you to help yourself. It runs, it is open and it is supported by a large community spread across all walks of life."[209]
In June 2013, whistleblowerEdward Snowdenused Tor to send information aboutPRISMtoThe Washington PostandThe Guardian.[210]
2014
[edit]In 2014, the Russian government offered a $111,000 contract to "study the possibility of obtaining technical information about users and users' equipment on the Tor anonymous network".[211][212]
In September 2014, in response to reports thatComcasthad been discouraging customers from using the Tor Browser,Comcastissued a public statement that "We have no policy against Tor, or any other browser or software."[213]
In October 2014, The Tor Project hired the public relations firm Thomson Communications to improve its public image (particularly regarding the terms "Dark Net" and "hidden services," which are widely viewed as being problematic) and to educate journalists about the technical aspects of Tor.[214]
Turkey blockeddownloads of Tor Browser from the Tor Project.[215]
2015
[edit]In June 2015, thespecial rapporteurfrom the United Nations'Office of the High Commissioner for Human Rightsspecifically mentioned Tor in the context of the debate in the U.S. about allowing so-calledbackdoorsin encryption programs for law enforcement purposes[216]in an interview forThe Washington Post.
In July 2015, the Tor Project announced an alliance with theLibrary Freedom Projectto establish exit nodes in public libraries.[217][218]The pilot program, which established a middle relay running on the excess bandwidth afforded by the Kilton Library inLebanon, New Hampshire,making it the first library in the U.S. to host a Tor node, was briefly put on hold when the local city manager and deputy sheriff voiced concerns over the cost of defending search warrants for information passed through the Tor exit node. Although theDepartment of Homeland Security(DHS) had alerted New Hampshire authorities to the fact that Tor is sometimes used by criminals, the Lebanon Deputy Police Chief and the Deputy City Manager averred that no pressure to strong-arm the library was applied, and the service was re-established on 15 September 2015.[219]U.S. Rep.Zoe Lofgren(D-Calif) released a letter on 10 December 2015, in which she asked theDHSto clarify its procedures, stating that "While the Kilton Public Library's board ultimately voted to restore their Tor relay, I am no less disturbed by the possibility thatDHSemployees are pressuring or persuading public and private entities to discontinue or degrade services that protect the privacy and anonymity of U.S. citizens. "[220][221][222]In a 2016 interview, Kilton Library IT Manager Chuck McAndrew stressed the importance of getting libraries involved with Tor: "Librarians have always cared deeply about protecting privacy, intellectual freedom, andaccess to information(the freedom to read). Surveillance has a very well-documented chilling effect on intellectual freedom. It is the job of librarians to remove barriers to information. "[223]The second library to host a Tor node was the Las Naves Public Library inValencia, Spain,implemented in the first months of 2016.[224]
In August 2015, anIBMsecurity research group, called "X-Force", put out a quarterly report that advised companies to block Tor on security grounds, citing a "steady increase" in attacks from Tor exit nodes as well as botnet traffic.[225]
In September 2015, Luke Millanta created OnionView (now defunct), a web service that plots the location of active Tor relay nodes onto an interactive map of the world. The project's purpose was to detail the network's size and escalating growth rate.[226]
In December 2015,Daniel Ellsberg(of thePentagon Papers),[227]Cory Doctorow(ofBoing Boing),[228]Edward Snowden,[229]and artist-activistMolly Crabapple,[230]amongst others, announced their support of Tor.
2016
[edit]In March 2016, New Hampshire state representativeKeith Ammonintroduced a bill[231]allowing public libraries to run privacy software. The bill specifically referenced Tor. The text was crafted with extensive input fromAlison Macrina,the director of theLibrary Freedom Project.[232]The bill was passed by the House 268–62.[233]
Also in March 2016, the first Tor node, specifically a middle relay, was established at a library in Canada, the Graduate Resource Centre (GRC) in the Faculty of Information and Media Studies (FIMS) at theUniversity of Western Ontario.[234]Given that the running of a Tor exit node is an unsettled area of Canadian law,[235]and that in general institutions are more capable than individuals to cope with legal pressures, Alison Macrina of the Library Freedom Project has opined that in some ways she would like to see intelligence agencies and law enforcement attempt to intervene in the event that an exit node were established.[236]
On 16 May 2016,CNNreported on the case of core Tor developer "isis agora lovecruft",[237]who had fled to Germany under the threat of a subpoena by the FBI during the Thanksgiving break of the previous year. TheElectronic Frontier Foundationlegally represented lovecruft.[238]
On 2 December 2016,The New Yorkerreported on burgeoningdigital privacyand security workshops in theSan Francisco Bay Area,particularly at thehackerspaceNoisebridge,in the wake of the2016 United States presidential election;downloading the Tor browser was mentioned.[239]Also, in December 2016, Turkey has blocked the usage of Tor, together with ten of the most usedVPNservices in Turkey, which were popular ways of accessing banned social media sites and services.[240]
Tor (andBitcoin) was fundamental to the operation of the dark web marketplaceAlphaBay,which was taken down in an international law enforcement operation in July 2017.[241]Despite federal claims that Tor would not shield a user, however,[242]elementaryoperational securityerrors outside of the ambit of the Tor network led to the site's downfall.[243]
2017
[edit]In June 2017 theDemocratic Socialists of Americarecommended intermittent Tor usage for politically active organizations and individuals as a defensive mitigation againstinformation securitythreats.[244][245]And in August 2017, according to reportage, cybersecurity firms which specialize in monitoring and researching the dark web (which relies on Tor as its infrastructure) on behalf of banks and retailers routinely share their findings with theFBIand with other law enforcement agencies "when possible and necessary" regarding illegal content. The Russian-speaking underground offering a crime-as-a-service model is regarded as being particularly robust.[246]
2018
[edit]In June 2018, Venezuela blocked access to the Tor network. The block affected both direct connections to the network and connections being made via bridge relays.[247]
On 20 June 2018, Bavarian police raided the homes of the board members of the non-profitZwiebelfreunde,a member oftorservers.net,which handles the European financial transactions ofriseup.netin connection with a blog post there which apparently promised violence against the upcomingAlternative for Germanyconvention.[248][249]Tor came out strongly against the raid on its support organization, which provides legal and financial aid for the setting up and maintenance of high-speed relays and exit nodes.[250]According to torservers.net, on 23 August 2018 the German court at Landgericht München ruled that the raid and seizures were illegal. The hardware and documentation seized had been kept under seal, and purportedly were neither analyzed nor evaluated by the Bavarian police.[251][252]
Since October 2018,Chinese online communitieswithin Tor have begun to dwindle due to increased efforts to stop them by the Chinese government.[253]
2019
[edit]In November 2019,Edward Snowdencalled for a full, unabridgedsimplified Chinesetranslation of his autobiography,Permanent Record,as the Chinese publisher had violated their agreement by expurgating all mentions of Tor and other matters deemed politically sensitive by theChinese Communist Party.[254][255]
2021
[edit]On 8 December 2021, the Russian government agencyRoskomnadzorannounced it has banned Tor and six VPN services for failing to abide by theRussian Internet blacklist.[256]Russian ISPs unsuccessfully attempted to block Tor's main website as well as several bridges beginning on 1 December 2021.[257]The Tor Project has appealed to Russian courts over this ban.[258]
2022
[edit]In response toInternet censorshipduring theRussian invasion of Ukraine,theBBCandVOAhave directed Russian audiences to Tor.[259]The Russian government increased efforts to block access to Tor through technical and political means, while the network reported an increase in traffic from Russia, and increased Russian use of its anti-censorshipSnowflake tool.[260]
Russian courts temporarily lifted the blockade on Tor's website (but not connections to relays) on May 24, 2022[261]due to Russian law requiring that the Tor Project be involved in the case. However, the blockade was reinstated on July 21, 2022.[262]
Iran implemented rolling internet blackouts during theMahsa Amini protests,and Tor andSnowflakewere used to circumvent them.[263][264][265][266]
China, with its highly centralized control of its internet,had effectively blocked Tor.[260]
Improved security
[edit]Tor responded to earlier vulnerabilities listed above by patching them and improving security. In one way or another, human (user) errors can lead to detection. The Tor Project website provides the best practices (instructions) on how to properly use the Tor browser. When improperly used, Tor is not secure. For example, Tor warns its users that not all traffic is protected; only the traffic routed through the Tor browser is protected. Users are also warned to useHTTPSversions of websites, not totorrentwith Tor, not to enable browser plugins, not to open documents downloaded through Tor while online, and to use safe bridges.[267]Users are also warned that they cannot provide their name or other revealing information in web forums over Tor and stay anonymous at the same time.[268]
Despite intelligence agencies' claims that 80% of Tor users would be de-anonymized within 6 months in the year 2013,[269]that has still not happened. In fact, as late as September 2016, the FBI could not locate, de-anonymize and identify the Tor user who hacked into the email account of a staffer onHillary Clinton's email server.[270]
The best tactic of law enforcement agencies to de-anonymize users appears to remain with Tor-relay adversaries running poisoned nodes, as well as counting on the users themselves using the Tor browser improperly. For example, downloading a video through the Tor browser and then opening the same file on an unprotected hard drive while online can make the users' real IP addresses available to authorities.[271]
Odds of detection
[edit]When properly used, odds of being de-anonymized through Tor are said to be extremely low. Tor project's co-founderNick Mathewsonexplained that the problem of "Tor-relay adversaries" running poisoned nodes means that a theoretical adversary of this kind is not the network's greatest threat:
"No adversary is truly global, but no adversary needs to be truly global," he says. "Eavesdropping on the entire Internet is a several-billion-dollar problem. Running a few computers to eavesdrop on a lot of traffic, a selective denial of service attack to drive traffic to your computers, that's like a tens-of-thousands-of-dollars problem." At the most basic level, an attacker who runs two poisoned Tor nodes—one entry, one exit—is able to analyse traffic and thereby identify the tiny, unlucky percentage of users whose circuit happened to cross both of those nodes. In 2016 the Tor network offers a total of around 7,000 relays, around 2,000 guard (entry) nodes and around 1,000 exit nodes. So the odds of such an event happening are one in two million (1⁄2000×1⁄1000), give or take. "[269]
Tor does not provide protection againstend-to-end timing attacks:if an attacker can watch the traffic coming out of the target computer, and also the traffic arriving at the target's chosen destination (e.g. a server hosting a.onion site), that attacker can use statistical analysis to discover that they are part of the same circuit.[268]
Levels of security
[edit]Depending on individual user needs, Tor browser offers three levels of security located under the Security Level (the small gray shield at the top-right of the screen) icon > Advanced Security Settings. In addition to encrypting the data, including constantly changing an IP address through a virtual circuit comprising successive, randomly selected Tor relays, several other layers of security are at a user's disposal:[272][273]
- Standard (default) – at this security level, all browser features are enabled.
- This level provides the most usable experience, and the lowest level of security.
- Safer – at this security level, the following changes apply:
- JavaScript is disabled on non-HTTPS sites.
- On sites where JavaScript is enabled, performance optimizations are disabled. Scripts on some sites may run slower.
- Some mechanisms of displaying math equations are disabled.
- Audio and video (HTML5 media), and WebGL are click-to-play.
- Safest – at this security level, these additional changes apply:
- JavaScript is disabled by default on all sites.
- Some fonts, icons, math symbols, and images are disabled.
- Audio and video (HTML5 media), and WebGL are click-to-play.
Introduction of Proof-of-Work Defense for Onion Services
[edit]In a groundbreaking development, Tor has unveiled a new defense mechanism to safeguard its onion services against crippling denial of service (DoS) attacks. With the release of Tor 0.4.8, this proof-of-work (PoW) defense promises to prioritize legitimate network traffic while deterring malicious attacks.[274]
Why the Need for PoW Defense?
Onion services, designed to protect user privacy by concealing IP addresses, have long been susceptible to DoS attacks. Traditional IP-based rate limits have proven inadequate in thwarting these threats. To counter this vulnerability, Tor has introduced a PoW mechanism that strengthens security without compromising user anonymity.
How Does it Work?
The PoW defense is like a ticket system that activates only during network stress. Before accessing an onion service, clients must solve a small computational puzzle, demonstrating their authenticity. The complexity of the puzzle correlates with the amount of computational "work" performed, confirming the user's legitimacy and deterring bot-based attacks. This dynamic system blocks attackers while ensuring a smooth experience for genuine users.
Impact on Attackers and Users
For attackers attempting to flood an onion service, the PoW defense poses a formidable obstacle. As attack intensity increases, the computational effort required also escalates, leading to diminishing returns for attackers. In contrast, regular users, who typically make only a few requests, experience manageable computational demands, with solving times ranging from 5 to 30 milliseconds. Even during network stress, users can access Tor by proving their humanity.
See also
[edit]Citations
[edit]- ^Dingledine, Roger (20 September 2002)."Pre- Alpha: run an onion proxy now!".[email protected](Mailing list).Archivedfrom the original on 26 July 2011.Retrieved17 July2008.
- ^"Stable release 0.4.8.12".6 June 2024.Retrieved6 June2024.
- ^"Tor".Open HUB.Archivedfrom the original on 3 September 2014.Retrieved27 May2021.
- ^"Announcing Arti, a pure-Rust Tor implementation".2022.Archivedfrom the original on 10 July 2021.Retrieved10 July2021.
- ^"LICENSE – Tor's source code".tor.Archivedfrom the original on 5 November 2018.Retrieved15 May2018.
- ^Collier, Ben (16 April 2024).Tor: From the Dark Web to the Future of Privacy.The MIT Press. p. 60.ISBN978-0-262-37892-5.Retrieved18 May2024.
Even years later, getting this wrong (by calling it The Onion Router, or writing TOR rather than Tor) remains a surefire way to get tripped up by the security community.
- ^abDingledine, Roger; Mathewson, Nick; Syverson, Paul (13 August 2004)."Tor: The Second-Generation Onion Router".Proc. 13th USENIX Security Symposium.San Diego, California.Archivedfrom the original on 9 August 2011.Retrieved17 November2008.
- ^"Tor Server Status".Tor Project – Metrics.Archivedfrom the original on 7 June 2020.Retrieved7 July2021.
- ^"ABOUT TOR BROWSER | Tor Project | Tor Browser Manual".tb-manual.torproject.org.Archivedfrom the original on 19 April 2022.Retrieved27 April2022.
- ^McCoy, Damon; Kevin Bauer; Dirk Grunwald; Tadayoshi Kohno; Douglas Sicker. "Shining light in dark places: Understanding the Tor network".International Symposium on Privacy Enhancing Technologies.
- ^abcLawrence, Dune (23 January 2014)."The Inside Story of Tor, the Best Internet Anonymity Tool the Government Ever Built".Bloomberg Businessweek.Archived fromthe originalon 29 March 2014.Retrieved28 April2014.
- ^ab"History".Tor Project.Archivedfrom the original on 13 January 2023.Retrieved5 June2021.
- ^"Tor FAQ: Why is it called Tor?".Tor Project.Archivedfrom the original on 17 January 2016.Retrieved1 July2011.
- ^Dingledine, Rogert (8 October 2003)."Tor is free".tor-dev(Mailing list). Tor Project.Archivedfrom the original on 13 February 2017.Retrieved23 September2016.
- ^"Tor Project Form 990 2008"(PDF).Tor Project.2009. Archived fromthe original(PDF)on 29 June 2017.Retrieved30 August2014.
- ^"Tor Project Form 990 2009"(PDF).Tor Project.2010. Archived fromthe original(PDF)on 29 June 2017.Retrieved30 August2014.
- ^Goodin, Dan (22 July 2014)."Tor developers vow to fix bug that can uncloak users".Ars Technica.Archivedfrom the original on 8 July 2017.Retrieved15 June2017.
- ^"Selected Papers in Anonymity".Free Haven.Archivedfrom the original on 12 July 2018.Retrieved26 October2005.
- ^"Tor Research Home".torproject.org.Archivedfrom the original on 26 June 2018.Retrieved31 July2014.
- ^Owen, Gareth."Dr Gareth Owen: Tor: Hidden Services and Deanonymisation".Retrieved20 June2015.
- ^Moore, Daniel."Cryptopolitik and the Darknet".Survival: Global Politics and Strategy.Retrieved20 March2016.
- ^Cox, Joseph (1 February 2016)."Study Claims Dark Web Sites Are Most Commonly Used for Crimes".Retrieved20 March2016.
- ^Zetter, Kim (17 May 2005)."Tor Torches Online Tracking".Wired.Archivedfrom the original on 26 July 2014.Retrieved30 August2014.
- ^abGregg, Brandon (30 April 2012)."How online black markets work".CSO Online.Archivedfrom the original on 13 August 2012.Retrieved6 August2012.
- ^Morisy, Michael (8 June 2012)."Hunting for child porn, FBI stymied by Tor undernet".Muckrock.Archivedfrom the original on 16 June 2012.Retrieved6 August2012.
- ^abcdBall, James; Schneier, Bruce; Greenwald, Glenn (4 October 2013)."NSA and GCHQ target Tor network that protects anonymity of web users".The Guardian.Archivedfrom the original on 28 February 2019.Retrieved5 October2013.
- ^"Leaping Over the Firewall: A Review of Censorship Circumvention Tools"(PDF).freedomhouse.org.Archived fromthe original(PDF)on 28 December 2023.Retrieved30 December2023.
- ^"Tor: Overview".The Tor Project.Archivedfrom the original on 6 June 2015.Retrieved29 April2015.
- ^Cochrane, Nate (2 February 2011)."Egyptians turn to Tor to organise dissent online".SC Magazine.Archivedfrom the original on 13 December 2011.Retrieved10 December2011.
- ^Jardine, Eric; Lindner, Andrew M.; Owenson, Gareth (15 December 2020)."The potential harms of the Tor anonymity network cluster disproportionately in free countries".Proceedings of the National Academy of Sciences.117(50): 31716–31721.Bibcode:2020PNAS..11731716J.doi:10.1073/pnas.2011893117.ISSN0027-8424.PMC7749358.PMID33257555.
- ^"Bitcoin: Monetarists Anonymous".The Economist.29 September 2012.Archivedfrom the original on 20 October 2013.Retrieved19 May2013.
- ^Boiten, Eerke; Hernandez-Castro, Julio (28 July 2014)."Can you really be identified on Tor or is that just what the cops want you to believe?".Phys.org.Archivedfrom the original on 1 February 2019.Retrieved31 July2014.
- ^"JTRIG Tools and Techniques".The Intercept.14 July 2014.Archivedfrom the original on 14 July 2014.Retrieved14 July2014.
- ^"Document from an internal GCHQ wiki lists tools and techniques developed by the Joint Threat Research Intelligence Group".documentcoud.org.5 July 2012.Archivedfrom the original on 8 August 2014.Retrieved30 July2014.
- ^Bode, Karl (12 March 2007)."Cleaning up Tor".Broadband.Archivedfrom the original on 21 October 2013.Retrieved28 April2014.
- ^Jones, Robert (2005).Internet forensics.O'Reilly. p.133.ISBN978-0-596-10006-3.
- ^Chen, Adrian (11 June 2012)."'Dark Net' Kiddie Porn Website Stymies FBI Investigation ".Gawker.Archivedfrom the original on 14 August 2012.Retrieved6 August2012.
- ^Chen, Adrian (1 June 2011)."The Underground Website Where You Can Buy Any Drug Imaginable".Gawker.Archived fromthe originalon 3 June 2011.Retrieved20 April2012.
- ^Steinberg, Joseph (8 January 2015)."How Your Teenage Son or Daughter May Be Buying Heroin Online".Forbes.Archivedfrom the original on 10 February 2015.Retrieved6 February2015.
- ^Goodin, Dan (16 April 2012)."Feds shutter online narcotics store that used Tor to hide its tracks".Ars Technica.Archivedfrom the original on 19 April 2012.Retrieved20 April2012.
- ^"Treasury Dept: Tor a Big Source of Bank Fraud".Krebs on Security.5 December 2014.Archivedfrom the original on 3 February 2019.Retrieved7 December2014.
- ^Farivar, Cyrus (3 April 2015)."How a $3.85 latte paid for with a fake $100 bill led to counterfeit kingpin's downfall".Ars Technica.Archivedfrom the original on 18 April 2015.Retrieved19 April2015.
- ^Cimpanu, Catalin (6 April 2017)."New Malware Intentionally Bricks IoT Devices".BleepingComputer.Archivedfrom the original on 19 February 2019.Retrieved7 April2017.
- ^Turner, Serrin (27 September 2013)."Sealed compaint"(PDF).United States of America v. Ross William Ulbricht.Archived fromthe original(PDF)on 2 October 2013.
- ^Higgins, Parker (3 October 2013)."In the Silk Road Case, Don't Blame the Technology".Electronic Frontier Foundation.Archivedfrom the original on 26 January 2014.Retrieved22 December2013.
- ^Soghoian, Chris (16 September 2007)."Tor anonymity server admin arrested".CNET News.Archivedfrom the original on 10 December 2010.Retrieved17 January2011.
- ^"Surveillance Self-Defense: Tor".Electronic Frontier Foundation.Archivedfrom the original on 26 June 2014.Retrieved28 April2014.
- ^abHarris, Shane; Hudson, John (4 October 2014)."Not Even the NSA Can Crack the State Department's Favorite Anonymous Service".Foreign Policy.Archivedfrom the original on 20 July 2014.Retrieved30 August2014.
- ^Dredge, Stuart (5 November 2013)."What is Tor? A beginner's guide to the privacy tool".The Guardian.Archivedfrom the original on 15 August 2014.Retrieved30 August2014.
- ^Fowler, Geoffrey A. (17 December 2012)."Tor: An Anonymous, And Controversial, Way to Web-Surf".The Wall Street Journal.Archivedfrom the original on 19 February 2014.Retrieved30 August2014.
- ^Tveten, Julianne (12 April 2017)."Where Domestic Violence and Cybersecurity Intersect".Rewire.Archivedfrom the original on 10 August 2017.Retrieved9 August2017.
- ^LeVines, George (7 May 2014)."As domestic abuse goes digital, shelters turn to counter-surveillance with Tor".Boston Globe.Archivedfrom the original on 14 September 2014.Retrieved8 May2014.
- ^Ellis, Justin (5 June 2014)."The Guardian introduces SecureDrop for document leaks".Nieman Journalism Lab.Archivedfrom the original on 17 August 2014.Retrieved30 August2014.
- ^O'Neill, Patrick Howell (9 March 2015)."U.K. Parliament says banning Tor is unacceptable and impossible".The Daily Dot.Archivedfrom the original on 2 April 2015.Retrieved19 April2015.
- ^Kelion, Leo (22 August 2014)."NSA and GCHQ agents 'leak Tor bugs', alleges developer".BBC News.Archivedfrom the original on 2 February 2019.Retrieved21 July2018.
- ^"Doesn't Tor enable criminals to do bad things?".Tor Project.Archivedfrom the original on 17 August 2013.Retrieved28 August2013.
- ^"Tor: Bridges".Tor Project.Archivedfrom the original on 12 May 2012.Retrieved9 January2011.
- ^"TorPCAP – Tor Network Forensics".Netresec.12 December 2018.Archivedfrom the original on 12 December 2018.Retrieved12 December2018.
- ^Winter, Philipp."How Do Tor Users Interact With Onion Services?"(PDF).Archived(PDF)from the original on 28 December 2018.Retrieved27 December2018.
- ^Mathewson, Nick (12 June 2003)."Add first draft of rendezvous point document".Tor Source Code.Archivedfrom the original on 15 November 2018.Retrieved23 September2016.
- ^Øverlier, Lasse; Syverson, Paul (21 June 2006)."2006 IEEE Symposium on Security and Privacy (S&P'06)"(PDF).Proceedings of the 2006 IEEE Symposium on Security and Privacy.IEEE Symposium on Security and Privacy.Oakland, Calif.: IEEE CS Press. p. 1.doi:10.1109/SP.2006.24.ISBN0-7695-2574-1.Archived(PDF)from the original on 10 August 2013.
- ^"TorSearch: a search engine specifically for Tor pages".Ghacks.12 October 2013.Retrieved11 May2015.
- ^Goodin, Dan (10 September 2007)."Tor at heart of embassy passwords leak".The Register.Archivedfrom the original on 25 September 2007.Retrieved20 September2007.
- ^Cox, Joseph (6 April 2016)."A Tool to Check If Your Dark Web Site Really Is Anonymous: 'OnionScan' will probe dark web sites for security weaknesses".Motherboard.Archivedfrom the original on 16 August 2017.Retrieved7 July2017.
- ^Zetter, Kim (12 December 2008)."New Service Makes Tor Anonymized Content Available to All".Wired.Archivedfrom the original on 18 March 2014.Retrieved22 February2014.
- ^Koebler, Jason (23 February 2015)."The Closest Thing to a Map of the Dark Net: Pastebin".Motherboard.Archivedfrom the original on 22 December 2016.Retrieved14 July2015.
- ^Dingledine, Roger (18 February 2009)."One cell is enough to break Tor's anonymity".Tor Project.Archivedfrom the original on 20 September 2010.Retrieved9 January2011.
- ^"TheOnionRouter/TorFAQ".Archivedfrom the original on 16 September 2020.Retrieved18 September2007.
Tor (like all current practical low-latency anonymity designs) fails when the attacker can see both ends of the communications channel
- ^Herrmann, Dominik; Wendolsky, Rolf; Federrath, Hannes (2009)."Website fingerprinting".Proceedings of the 2009 ACM workshop on Cloud computing security(PDF).New York, New York, US: ACM Press. pp. 31–42.doi:10.1145/1655008.1655013.ISBN9781605587844.S2CID8479479.
- ^Herrmann, Dominik; Wendolsky, Rolf; Federrath, Hannes (13 November 2009)."Website Fingerprinting: Attacking Popular Privacy Enhancing Technologies with the Multinomial Naïve-Bayes Classifier"(PDF).Proceedings of the 2009 ACM Cloud Computing Security Workshop (CCSW).Cloud Computing Security Workshop. New York, US:Association for Computing Machinery.Archived(PDF)from the original on 22 April 2011.Retrieved2 September2010.
- ^Judge, Peter (20 August 2013)."Zmap's Fast Internet Scan Tool Could Spread Zero Days In Minutes".TechWeek Europe.Archived fromthe originalon 24 August 2013.
- ^"Consensus health".Consensus-health.torproject.org.Archivedfrom the original on 12 January 2021.Retrieved15 March2022.
- ^George Tankersley (4 October 2017)."Getting Started with Tor Development".Archivedfrom the original on 22 January 2021.Retrieved16 January2021.
- ^tommy (2 November 2017)."Introducing Bastet, Our New Directory Authority".The Tor Project.Archivedfrom the original on 25 November 2020.Retrieved16 January2021.
- ^Karsten Loesing (15 May 2014)."10 years of collecting Tor directory data".The Tor Project.Archivedfrom the original on 20 June 2020.Retrieved16 January2021.
- ^Akhoondi, Masoud; Yu, Curtis; Madhyastha, Harsha V. (May 2012).LASTor: A Low-Latency AS-Aware Tor Client(PDF).IEEE Symposium on Security and Privacy. Oakland, US. Archived fromthe original(PDF)on 28 September 2013.Retrieved28 April2014.
- ^Zetter, Kim(10 September 2007)."Rogue Nodes Turn Tor Anonymizer Into Eavesdropper's Paradise".Wired.Archivedfrom the original on 31 December 2008.Retrieved16 September2007.
- ^Lemos, Robert (8 March 2007)."Tor hack proposed to catch criminals".SecurityFocus.Archivedfrom the original on 10 February 2019.Retrieved3 February2008.
- ^Gray, Patrick (13 November 2007)."The hack of the year".Sydney Morning Herald.Archivedfrom the original on 18 April 2014.Retrieved28 April2014.
- ^abcd"Someone Is Running Hundreds of Malicious Servers on the Tor Network and Might Be De-Anonymizing Users".Gizmodo.3 December 2021.Archivedfrom the original on 5 December 2021.Retrieved5 December2021.
- ^abcd"A mysterious threat actor is running hundreds of malicious Tor relays".The Record by Recorded Future.3 December 2021.Archivedfrom the original on 17 January 2023.Retrieved5 December2021.
- ^"Over 25% Of Tor Exit Relays Spied On Users' Dark Web Activities".The Hacker News.10 May 2021.Archivedfrom the original on 5 December 2021.Retrieved5 December2021.
- ^Paganini, Pierluigi (3 December 2021)."KAX17 threat actor is attempting to deanonymize Tor users running thousands of rogue relays".cybersecurityworldconference.Archivedfrom the original on 23 June 2021.
- ^Koppen, Georg (9 November 2021)."[tor-relays] Recent rejection of relays".Archivedfrom the original on 4 December 2021.Retrieved5 December2021.
- ^"Tor anonymizing network compromised by French researchers".The Hacker News.24 October 2011.Archivedfrom the original on 7 December 2011.Retrieved10 December2011.
- ^"Des chercheurs Francais cassent le reseau d'anonymisation Tor".01net(in French).Archivedfrom the original on 16 October 2011.Retrieved17 October2011.
- ^phobos (24 October 2011)."Rumors of Tor's compromise are greatly exaggerated".Tor Project.Archivedfrom the original on 30 January 2012.Retrieved20 April2012.
- ^abSoltani, Ramin; Goeckel, Dennis; Towsley, Don; Houmansadr, Amir (27 November 2017). "Towards provably invisible network flow fingerprints".2017 51st Asilomar Conference on Signals, Systems, and Computers.IEEE. pp. 258–262.arXiv:1711.10079.doi:10.1109/ACSSC.2017.8335179.ISBN978-1-5386-1823-3.S2CID4943955.
- ^abMurdoch, Steven J.; Danezis, George (19 January 2006)."Low-Cost Traffic Analysis of Tor"(PDF).Proceedings of the 2005 IEEE Symposium on Security and Privacy. IEEE CS.IEEE Symposium on Security and Privacy.Archived(PDF)from the original on 16 June 2007.Retrieved21 May2007.
- ^"BBC iPlayer Help – Why does BBC iPlayer think I'm outside the UK?".BBC.Archived fromthe originalon 28 December 2017.Retrieved10 September2017.
- ^abcdLe Blond, Stevens; Manils, Pere; Chaabane, Abdelberi; Ali Kaafar, Mohamed; Castelluccia, Claude; Legout, Arnaud; Dabbous, Walid (March 2011).One Bad Apple Spoils the Bunch: Exploiting P2P Applications to Trace and Profile Tor Users(PDF).4th USENIX Workshop on Large-Scale Exploits and Emergent Threats (LEET '11). National Institute for Research in Computer Science and Control.Archived(PDF)from the original on 27 April 2011.Retrieved13 April2011.
- ^McCoy, Damon; Bauer, Kevin; Grunwald, Dirk; Kohno, Tadayoshi; Sicker, Douglas (2008)."Privacy Enhancing Technologies"(PDF).Proceedings of the 8th International Symposium on Privacy Enhancing Technologies.8th International Symposium on Privacy Enhancing Technologies. Lecture Notes in Computer Science. Vol. 5134. Berlin, Germany: Springer-Verlag. pp. 63–76.doi:10.1007/978-3-540-70630-4_5.ISBN978-3-540-70629-8.Archived(PDF)from the original on 15 May 2012.Retrieved13 April2011.
- ^Jansen, Rob; Tschorsch, Florian; Johnson, Aaron; Scheuermann, Björn (2014).The Sniper Attack: Anonymously Deanonymizing and Disabling the Tor Network(PDF).21st Annual Network & Distributed System Security Symposium.Archived(PDF)from the original on 30 June 2014.Retrieved28 April2014.
- ^Dingledine, Roger (7 April 2014a)."OpenSSL bug CVE-2014-0160".Tor Project.Archivedfrom the original on 10 July 2017.Retrieved28 April2014.
- ^Dingledine, Roger (16 April 2014b)."Rejecting 380 vulnerable guard/exit keys".tor-relays(Mailing list).Archivedfrom the original on 19 April 2014.Retrieved28 April2014.
- ^Lunar (16 April 2014)."Tor Weekly News — 16 April 2014".Tor Project.Archivedfrom the original on 19 April 2014.Retrieved28 April2014.
- ^Gallagher, Sean (18 April 2014)."Tor network's ranks of relay servers cut because of Heartbleed bug".Ars Technica.Archivedfrom the original on 1 May 2014.Retrieved28 April2014.
- ^Mimoso, Michael (17 April 2014)."Tor begins blacklisting exit nodes vulnerable to Heartbleed".Threat Post.Archivedfrom the original on 19 April 2014.Retrieved28 April2014.
- ^Dingledine (2014)"On July 4, 2014 we found a group of relays that we assume were trying to deanonymize users. They appear to have been targeting people who operate or access Tor hidden services."
- ^abDingledine, Roger (30 July 2014)."Tor security advisory:" relay early "traffic confirmation attack".The Tor Project.Archivedfrom the original on 24 May 2019.Retrieved9 July2018.
- ^Dingledine (2014)"...we assume were trying to deanonymize users. They appear to have been targeting people who operate or access Tor hidden services... users who operated or accessed hidden services from early February through July 4 should assume they were affected... We know the attack looked for users who fetched hidden service descriptors... The attack probably also tried to learn who published hidden service descriptors, which would allow the attackers to learn the location of that hidden service... Hidden service operators should consider changing the location of their hidden service."
- ^Dingledine (2014)"Relays should upgrade to a recent Tor release (0.2.4.23 or 0.2.5.6- Alpha ), to close the particular protocol vulnerability the attackers used..."
- ^Dingledine (2014)"For expert users, the new Tor version warns you in your logs if a relay on your path injects any relay-early cells: look for the phrase 'Received an inbound RELAY_EARLY cell'"
- ^Dingledine (2014)"Clients that upgrade (once new Tor Browser releases are ready) will take another step towards limiting the number of entry guards that are in a position to see their traffic, thus reducing the damage from future attacks like this one... 3) Put out a software update that will (once enough clients have upgraded) let us tell clients to move to using one entry guard rather than three, to reduce exposure to relays over time."
- ^Dingledine (2014)"Hidden service operators should consider changing the location of their hidden service."
- ^Dingledine (2014)"...but remember that preventing traffic confirmation in general remains an open research problem."
- ^Greenberg, Andy (7 November 2014)."Global Web Crackdown Arrests 17, Seizes Hundreds Of Dark Net Domains".Wired.Archivedfrom the original on 9 August 2015.Retrieved9 August2015.
- ^Wakefield, Jane (7 November 2014)."Huge raid to shut down 400-plus dark net sites –".BBC News.Archivedfrom the original on 21 August 2015.Retrieved9 August2015.
- ^O'Neill, Patrick Howell (7 November 2014)."The truth behind Tor's confidence crisis".The Daily Dot.Archivedfrom the original on 10 November 2014.Retrieved10 November2014.
- ^Knight, Shawn (7 November 2014)."Operation Onymous seizes hundreds of darknet sites, 17 arrested globally".Techspot.Archivedfrom the original on 8 November 2014.Retrieved8 November2014.
- ^abcd"Court Docs Show a University Helped FBI Bust Silk Road 2, Child Porn Suspects".Motherboard.11 November 2015.Archivedfrom the original on 21 November 2015.Retrieved20 November2015.
- ^ab"Did the FBI Pay a University to Attack Tor Users?".torproject.org.11 November 2015.Archivedfrom the original on 18 November 2015.Retrieved20 November2015.
- ^Zorz, Zeljka (12 November 2015)."Tor Project claims FBI paid university researchers $1m to unmask Tor users".Help Net Security.Archivedfrom the original on 17 November 2015.Retrieved20 November2015.
- ^abFelten, Ed (31 July 2014)."Why were CERT researchers attacking Tor?".Freedom to Tinker, Center for Information Technology Policy, Princeton University.Archivedfrom the original on 5 September 2016.Retrieved9 July2018.
- ^Madnick, Stuart; Xitong Li; Nazli Choucri (2009). "Experiences and challenges with using CERT data to analyze international cyber security".MIT Sloan Research Paper.
- ^Cimpanu, Catalin (10 March 2016)."Tor Users Can Be Tracked Based on Their Mouse Movements".Softpedia.Archivedfrom the original on 11 March 2016.Retrieved11 March2016.
- ^Anonymous (10 March 2016)."Tor Users Can Be Tracked Based On Their Mouse Movements".Slashdot.Archivedfrom the original on 12 March 2016.Retrieved11 March2016.
- ^Greenberg, Andy (26 August 2015)."Agora, the Dark Web's Biggest Drug Market, Is Going Offline".Wired.Archivedfrom the original on 15 August 2016.Retrieved13 September2016.
- ^Albert Kwon; Mashael AlSabah; David Lazar; Marc Dacier; Srinivas Devadas (August 2015)."Circuit Fingerprinting Attacks: Passive Deanonymization of Tor Hidden Services"(PDF).Archived(PDF)from the original on 9 April 2016.Retrieved14 July2016.
- ^Danezis1, George; Wittneben, Bettina."The Economics of Mass Surveillance and the Questionable Value of Anonymous Communications"(PDF).Archived(PDF)from the original on 25 October 2016.Retrieved27 April2022– via ecoinfosec.org.
{{cite web}}:CS1 maint: numeric names: authors list (link) - ^"Repository Analytics".Tor Project GitLab.Archivedfrom the original on 24 June 2022.Retrieved24 August2022.
- ^abcd"New Release: Tor Browser 13.0.16 | Tor Project".Retrieved13 June2024.
- ^"Download Tor Browser in your language".The Tor Project, Inc.Archivedfrom the original on 3 June 2021.Retrieved19 December2022.
- ^"Tor Project: FAQ".torproject.org.Archivedfrom the original on 24 March 2019.Retrieved31 October2019.
- ^"Tor Browser Bundle".Tor Project.23 June 2014. Archived fromthe originalon 23 June 2014.Retrieved21 May2017.
- ^"Tor Project: Core People".Tor Project.Archived fromthe originalon 18 January 2011.Retrieved17 July2008.
- ^Murdoch, Steven J.(30 January 2008)."New Tor distribution for testing: Tor Browser Bundle".tor-talk(Mailing list).Archivedfrom the original on 5 March 2020.Retrieved13 January2020.
- ^Perry, Mike; Clark, Erinn; Murdoch, Steven (15 March 2013)."The Design and Implementation of the Tor Browser [DRAFT]".Tor Project.Archivedfrom the original on 15 August 2014.Retrieved28 April2014.
- ^abAlin, Andrei (2 December 2013)."Tor Browser Bundle Ubuntu PPA".Web Upd8.Archivedfrom the original on 21 April 2014.Retrieved28 April2014.
- ^Knight, John (1 September 2011)."Tor Browser Bundle-Tor Goes Portable".Linux Journal.Archivedfrom the original on 29 April 2014.Retrieved28 April2014.
- ^"This repository contains TorBrowser Releases".GitHub.23 September 2020.Archivedfrom the original on 23 September 2020.Retrieved23 September2020.
- ^"United States v. McGrath".Courtlistener.Free Law Project. 12 December 2013.Retrieved2 March2024.
- ^Poulsen, Kevin (8 May 2014)."Visit the Wrong Website, and the FBI Could End Up in Your Computer".Wired.Archivedfrom the original on 11 January 2018.Retrieved12 March2017.
- ^"Feds bust through huge Tor-hidden child porn site using questionable malware".Ars Technica.16 July 2015.Archivedfrom the original on 24 March 2020.Retrieved26 July2018.
- ^"FBI Tor busting 227 1".Archivedfrom the original on 2 July 2018.Retrieved26 July2018.
- ^Miller, Matthew; Stroschein, Joshua; Podhradsky, Ashley (25 May 2016)."Reverse Engineering a NIT That Unmasks Tor Users".Annual ADFSL Conference on Digital Forensics, Security and Law.Archivedfrom the original on 2 July 2018.Retrieved26 July2018.
- ^"The FBI Used the Web's Favorite Hacking Tool to Unmask Tor Users".Wired.16 December 2014.Archivedfrom the original on 22 February 2019.Retrieved26 July2018.
- ^"Federal Cybersecurity Director Found Guilty on Child Porn Charges".Wired.27 August 2014.Archivedfrom the original on 23 February 2019.Retrieved26 July2018.
- ^"Former Acting HHS Cyber Security Director Sentenced to 25 Years in Prison for Engaging in Child Pornography Enterprise".US Department of Justice. 5 January 2015.Archivedfrom the original on 2 July 2018.
- ^"New York Man Sentenced to Six Years in Prison for Receiving and Accessing Child Pornography".US Department of Justice. 17 December 2015.Archivedfrom the original on 5 July 2018.
- ^Poulsen, Kevin (5 August 2013)."Feds Are Suspects in New Malware That Attacks Tor Anonymity".Wired.Archivedfrom the original on 29 April 2014.Retrieved12 March2017.
- ^Krebs, Brian (13 August 2013)."Firefox Zero-Day Used in Child Porn Hunt?".Krebs on Security.Archivedfrom the original on 13 December 2020.Retrieved26 December2020.
- ^"Peeling back the layers of Tor with EgotisticalGiraffe".The Guardian.4 October 2013.Archivedfrom the original on 5 October 2013.Retrieved5 October2013.
- ^Samson, Ted (5 August 2013)."Tor Browser Bundle for Windows users susceptible to info-stealing attack".InfoWorld.Archivedfrom the original on 29 April 2014.Retrieved28 April2014.
- ^Poulsen, Kevin (8 May 2013)."Feds Are Suspects in New Malware That Attacks Tor Anonymity".Wired.Archivedfrom the original on 29 April 2014.Retrieved29 April2014.
- ^Owen, Gareth."FBI Malware Analysis".Archived fromthe originalon 17 April 2014.Retrieved6 May2014.
- ^O'Faolain, Aodhan (8 August 2013)."Man sought in US on child porn charges further remanded in custody".The Irish Times.Archivedfrom the original on 9 August 2013.Retrieved26 December2020.
- ^Man behind world's biggest source of child abuse imagery is jailed for 27 yearsArchived5 October 2021 at theWayback Machine,the guardian, 2021/09/16
- ^Best, Jessica (21 January 2014)."Man branded 'largest facilitator of child porn on the planet' remanded in custody again".Daily Mirror.Archivedfrom the original on 29 May 2014.Retrieved29 April2014.
- ^Dingledine, Roger (5 August 2013)."Tor security advisory: Old Tor Browser Bundles vulnerable".Tor Project.Archivedfrom the original on 26 March 2014.Retrieved28 April2014.
- ^Poulsen, Kevin (13 September 2013)."FBI Admits It Controlled Tor Servers Behind Mass Malware Attack".Wired.Archivedfrom the original on 21 December 2013.Retrieved22 December2013.
- ^Schneier, Bruce (4 October 2013)."Attacking Tor: how the NSA targets users' online anonymity".The Guardian.Archivedfrom the original on 7 August 2017.Retrieved22 December2013.
- ^"Someone is tricking Chinese YouTube users with a spyware version of the Tor Browser".The Verge.4 October 2022.Archivedfrom the original on 18 October 2022.Retrieved18 October2022.
- ^abSingh, Sukhbir (29 October 2015)."Tor Messenger Beta: Chat over Tor, Easily".The Tor Blog.The Tor Project.Archivedfrom the original on 30 October 2015.Retrieved31 October2015.
- ^Singh, Sukhbir (28 September 2017)."Tor Messenger 0.5.0b1 is released".sukhbir's blog.The Tor Project.Archivedfrom the original on 6 October 2017.Retrieved6 October2017.
- ^Singh, Sukhbir (2 April 2018)."Sunsetting Tor Messenger".Archivedfrom the original on 2 April 2020.Retrieved9 April2020.
- ^"Tor Messenger Design Document".The Tor Project.13 July 2015.Archivedfrom the original on 22 November 2015.Retrieved22 November2015.
- ^"Sunsetting Tor Messenger | Tor Project".blog.torproject.org.Archivedfrom the original on 22 April 2022.Retrieved7 May2022.
- ^Aemasu, Lucian (3 April 2018)."Tor Project Shuts Down Development Of Tor Messenger".Tom's Hardware.Retrieved3 April2018.
- ^Sharwood, Simon (3 April 2018)."Tor 'sunsets' secure Messenger that never exited beta".The Register.Archivedfrom the original on 15 July 2018.Retrieved2 October2019.
- ^"Tor Mobile | Tor Project | Support".support.torproject.org.Retrieved14 February2021.
- ^"How to anonymize all of your apps on Android".The Daily Dot.8 October 2014.Retrieved14 February2021.
- ^Staff, Ars (22 November 2016)."Tor phone is antidote to Google" hostility "over Android, says developer".Ars Technica.Retrieved14 February2021.
- ^Staff, Ars (22 November 2016)."Tor phone is antidote to Google" hostility "over Android, says developer".Ars Technica.Archivedfrom the original on 13 August 2022.Retrieved13 August2022.
- ^"Tor".Vuze.Archivedfrom the original on 30 April 2013.Retrieved3 March2010.
- ^"Bitmessage FAQ".Bitmessage.Archivedfrom the original on 18 August 2013.Retrieved17 July2013.
- ^Hassan, Nihad; Hijazi, Rami (2016).Data Hiding Techniques in Windows OS: A Practical Approach to Investigation and Defense.Syngress. p. 184.ISBN978-0-12-804496-4.Archivedfrom the original on 5 July 2022.Retrieved5 July2022.
- ^"About".The Guardian Project.Archivedfrom the original on 16 April 2011.Retrieved10 May2011.
- ^"ChatSecure: Private Messaging".The Guardian Project.Archivedfrom the original on 24 September 2014.Retrieved20 September2014.
- ^"Orbot: Mobile Anonymity + Circumvention".The Guardian Project.Archivedfrom the original on 11 May 2011.Retrieved10 May2011.
- ^Orbot iOS,Guardian Project, 25 August 2022,archivedfrom the original on 25 August 2022,retrieved25 August2022
- ^"Orweb: Privacy Browser".The Guardian Project.Archived fromthe originalon 11 May 2011.Retrieved10 May2011.
- ^n8fr8 (30 June 2015)."Orfox: Aspiring to bring Tor Browser to Android".guardianproject.info.Archivedfrom the original on 13 September 2015.Retrieved17 August2015.
Our plan is to actively encourage users to move from Orweb to Orfox, and stop active development of Orweb, even removing to from the Google Play Store.
{{cite web}}:CS1 maint: numeric names: authors list (link) - ^"ProxyMob: Firefox Mobile Add-on".The Guardian Project.Archived fromthe originalon 11 May 2011.Retrieved10 May2011.
- ^"Obscura: Secure Smart Camera".The Guardian Project.Archivedfrom the original on 24 September 2014.Retrieved19 September2014.
- ^Endless / Onion Browser License (OBL)[permanent dead link]
- ^"Tor at the Heart: Onion Browser (and more iOS Tor)".The Tor Blog.Archivedfrom the original on 28 August 2017.
- ^"Onion Browser on the App Store".
- ^"OnionBrowser/OnionBrowser".GitHub.30 June 2021.Archivedfrom the original on 17 November 2021.
- ^Shankland, Stephen (28 June 2018)."Brave advances browser privacy with Tor-powered tabs".CNET.Archivedfrom the original on 27 September 2018.Retrieved27 September2018.
- ^Brave (5 October 2020)."Brave now has its own Tor Onion Service, providing more users with secure access to Brave".Brave Browser.Archivedfrom the original on 6 October 2020.Retrieved22 January2021.
- ^Жуков, Антон (15 December 2009)."Включаем Tor на всю катушку"[Make Tor go the whole hog].Xakep.Archived fromthe originalon 1 September 2013.Retrieved28 April2014.
- ^"Tor Project: Pluggable Transports".torproject.org.Archivedfrom the original on 13 August 2016.Retrieved5 August2016.
- ^Brandom, Russell (9 May 2014)."Domestic violence survivors turn to Tor to escape abusers".The Verge.Archivedfrom the original on 2 September 2014.Retrieved30 August2014.
- ^Gurnow, Michael (1 July 2014)."Seated Between Pablo Escobar and Mahatma Gandhi: The Sticky Ethics of Anonymity Networks".Dissident Voice.Archivedfrom the original on 6 October 2014.Retrieved17 July2014.
- ^Zetter, Kim (1 June 2010)."WikiLeaks Was Launched With Documents Intercepted From Tor".Wired.Archivedfrom the original on 12 August 2014.Retrieved30 August2014.
- ^Lee, Timothy B. (10 June 2013)."Five ways to stop the NSA from spying on you".The Washington Post.Archivedfrom the original on 4 October 2014.Retrieved30 August2014.
- ^Norton, Quinn (9 December 2014)."Clearing the air around Tor".PandoDaily.Archivedfrom the original on 25 May 2019.Retrieved10 December2014.
- ^abLevine, Yasha (16 July 2014)."Almost everyone involved in developing Tor was (or is) funded by the US government".Pando Daily.Archivedfrom the original on 11 April 2016.Retrieved21 April2016.
- ^McKim, Jenifer B. (8 March 2012)."Privacy software, criminal use".The Boston Globe.Archived fromthe originalon 12 March 2012.
- ^Appelbaum J, Gibson A, Goetz J, Kabisch V, Kampf L, Ryge L (3 July 2014)."NSA targets the privacy-conscious".Panorama.Norddeutscher Rundfunk.Archivedfrom the original on 3 July 2014.Retrieved4 July2014.
- ^"Tor: Sponsors".Tor Project.Archivedfrom the original on 27 July 2011.Retrieved11 December2010.
- ^Fowler, Geoffrey A. (17 December 2012)."Tor: an anonymous, and controversial, way to web-surf".Wall Street Journal.Archivedfrom the original on 11 March 2015.Retrieved19 May2013.
- ^Moore, Daniel; Rid, Thomas. "Cryptopolitik and the Darknet". Survival. Feb2016, Vol. 58 Issue 1, p7-38. 32p.
- ^Inc., The Tor Project,. "Tor: Sponsors". torproject.org. Retrieved 28 October 2016.
- ^Fung, Brian (6 September 2013)."The feds pay for 60 percent of Tor's development. Can users trust it?".The Switch.Washington Post.Archivedfrom the original on 9 September 2013.Retrieved6 February2014.
- ^"Tor is Not as Safe as You May Think".Infosecurity magazine.2 September 2013.Archivedfrom the original on 27 August 2014.Retrieved30 August2014.
- ^"'Tor Stinks' presentation – read the full document ".The Guardian.4 October 2014.Archivedfrom the original on 29 August 2014.Retrieved30 August2014.
- ^O'Neill, Patrick Howell (2 October 2014)."The real chink in Tor's armor".The Daily Dot.Archivedfrom the original on 25 May 2019.Retrieved3 October2014.
- ^Lee, Dave (7 November 2014)."Dark net experts trade theories on 'de-cloaking' after raids".BBC News.Archivedfrom the original on 12 November 2014.Retrieved12 November2014.
- ^SPIEGEL Staff (28 December 2014)."Prying Eyes: Inside the NSA's War on Internet Security".Der Spiegel.Archivedfrom the original on 24 January 2015.Retrieved23 January2015.
- ^"Presentation from the SIGDEV Conference 2012 explaining which encryption protocols and techniques can be attacked and which not"(PDF).Der Spiegel.28 December 2014.Archived(PDF)from the original on 8 October 2018.Retrieved23 January2015.
- ^"2010 Free Software Awards announced".Free Software Foundation.Archivedfrom the original on 1 May 2015.Retrieved23 March2011.
- ^Lambert, Patrick (21 September 2011)."How the TOR Project defeated Iran filters inside 24 hours".TechRepublic.Archivedfrom the original on 15 October 2022.Retrieved15 October2022.
- ^"Iranian block on Tor traffic quickly foiled – The H Security: News and Features".h-online.Archivedfrom the original on 18 October 2022.Retrieved15 October2022.
- ^Wittmeyer, Alicia P.Q. (26 November 2012)."The FP Top 100 Global Thinkers".Foreign Policy.Archived fromthe originalon 30 November 2012.Retrieved28 November2012.
- ^Sirius, R. U. (11 March 2013)."Interview uncut: Jacob Appelbaum".theverge.Archivedfrom the original on 20 October 2014.Retrieved17 September2017.
- ^Gaertner, Joachim (1 July 2013)."Darknet – Netz ohne Kontrolle".Das Erste(in German). Archived fromthe originalon 4 July 2013.Retrieved28 August2013.
- ^Gallagher, Sean (25 July 2014)."Russia publicly joins war on Tor privacy with $111,000 bounty".Ars Technica.Archivedfrom the original on 26 July 2014.Retrieved26 July2014.
- ^Lucian, Constantin (25 July 2014)."Russian government offers huge reward for help unmasking anonymous Tor users".PC World.Archivedfrom the original on 26 July 2014.Retrieved26 July2014.
- ^Livingood, Jason (15 September 2014)."Setting the Record Straight on Tor".Archivedfrom the original on 4 January 2021.Retrieved5 January2021.
The report may have generated a lot of clicks but is totally inaccurate. Comcast is not asking customers to stop using Tor, or any other browser for that matter. We have no policy against Tor, or any other browser or software. Customers are free to use their Xfinity Internet service to visit any website, use any app, and so forth.... Comcast doesn't monitor our customer's browser software, web surfing or online history.
- ^O'Neill, Patrick Howell (26 March 2015)."Tor's great rebranding".The Daily Dot.Archivedfrom the original on 12 April 2015.Retrieved19 April2015.
- ^Galperin, Eva (27 March 2014)."When Is a Tor Block Not a Tor Block?".Electronic Frontier Foundation.Archivedfrom the original on 15 October 2022.Retrieved15 October2022.
- ^Peterson, Andrea (28 May 2015)."U.N. report: Encryption is important to human rights — and backdoors undermine it".The Washington Post.Archivedfrom the original on 23 June 2015.Retrieved17 September2017.
- ^"Tor Exit Nodes in Libraries – Pilot (phase one)".Tor Project.org.Archivedfrom the original on 8 September 2015.Retrieved15 September2015.
- ^"Library Freedom Project".libraryfreedomproject.org.Archivedfrom the original on 19 September 2015.Retrieved15 September2015.
- ^Doyle-Burr, Nora (16 September 2015)."Despite Law Enforcement Concerns, Lebanon Board Will Reactivate Privacy Network Tor at Kilton Library".Valley News.Archived fromthe originalon 18 September 2015.Retrieved20 November2015.
- ^"Lofgren questions DHS policy towards Tor Relays".house.gov.10 December 2015. Archived fromthe originalon 3 June 2016.Retrieved4 June2016.
- ^Geller, Eric (11 December 2015)."Democratic lawmaker wants to know if DHS is sabotaging plans for Tor exit relays".The Daily Dot.Archivedfrom the original on 10 June 2016.Retrieved4 June2016.
- ^Kopfstein, Janus (12 December 2015)."Congresswoman Asks Feds Why They Pressured a Library to Disable Its Tor Node".Motherboard.Archivedfrom the original on 22 December 2015.
- ^"Tor crusader discuss privacy, freedom with ExpressVPN".Home of internet privacy.4 August 2016.Archivedfrom the original on 31 August 2017.Retrieved11 September2017.
- ^Gonzalo, Marilín (26 January 2016)."Esta biblioteca valenciana es la segunda del mundo en unirse al proyecto Tor".El Diario(in Spanish).Archivedfrom the original on 7 March 2016.Retrieved4 March2016.
- ^Broersma, Matthew (26 August 2015)."IBM Tells Companies To Block Tor Anonymisation Network".TechWeekEurope UK.Archivedfrom the original on 10 September 2015.Retrieved15 September2015.
- ^Greenberg, Andy (14 September 2015)."Mapping How Tor's Anonymity Network Spread Around the World".Wired.Archivedfrom the original on 3 February 2016.Retrieved9 February2016.
- ^"This is What a Tor Supporter Looks Like: Daniel Ellsberg".The Tor Blog.26 December 2015.Archivedfrom the original on 4 March 2016.Retrieved4 June2016.
- ^"This is What a Tor Supporter Looks Like: Cory Doctorow".The Tor Blog.18 December 2015.Archivedfrom the original on 16 June 2016.Retrieved4 June2016.
- ^"This is What a Tor Supporter Looks Like: Edward Snowden".The Tor Blog.30 December 2015.Archivedfrom the original on 9 April 2016.Retrieved4 June2016.
- ^"This is what a Tor Supporter looks like: Molly Crabapple".The Tor Blog.9 December 2015.Archivedfrom the original on 16 June 2016.Retrieved4 June2016.
- ^"House Bill 1508: An Act allowing public libraries to run certain privacy software".New Hampshire State Government.10 March 2016.Archivedfrom the original on 11 April 2017.Retrieved4 June2016.
- ^O'Neill, Patrick Howell (18 February 2016)."New Hampshire bill allows for libraries' usage of encryption and privacy software".The Daily Dot.Archivedfrom the original on 11 March 2016.Retrieved10 March2016.
- ^"New Hampshire HB1508 – 2016 – Regular Session".legiscan.Archivedfrom the original on 29 July 2016.Retrieved4 June2016.
- ^"Library in FIMS joins global network fighting back against digital surveillance, censorship, and the obstruction of information".FIMS News.14 March 2016.Archivedfrom the original on 20 March 2016.Retrieved16 March2016.
- ^Pearson, Jordan (25 September 2015)."Can You Be Arrested for Running a Tor Exit Node In Canada?".Motherboard.Archivedfrom the original on 23 March 2016.Retrieved16 March2016.
- ^Pearson, Jordan (16 March 2016)."Canadian Librarians Must Be Ready to Fight the Feds on Running a Tor Node".Motherboard.Archivedfrom the original on 19 March 2016.Retrieved16 March2016.
- ^lovecruft, isis agora (7 May 2020)."May 7, 2020 Tweet".Archivedfrom the original on 27 May 2021.Retrieved7 April2021.
my name is isis agora lovecruft not Isis Agora Lovecruft
- ^Pagliery, Jose (17 May 2016)."Developer of anonymous Tor software dodges FBI, leaves US".CNN.Archivedfrom the original on 17 May 2016.Retrieved17 May2016.
- ^Weiner, Anna (2 December 2016)."Trump Preparedness: Digital Security 101".The New Yorker.Archivedfrom the original on 25 October 2020.Retrieved20 February2020.
- ^"Turkey Partially Blocks Access to Tor and Some VPNs".19 December 2016.Archivedfrom the original on 20 December 2016.Retrieved24 September2017.
- ^"Forfeiture Complaint".Justice.gov. 20 July 2017. p. 27.Archivedfrom the original on 23 September 2020.Retrieved28 July2017.
- ^Leyden, John (20 July 2017)."Cops harpoon two dark net whales in megabust: AlphaBay and Hansa: Tor won't shield you, warn Feds".The Register.Archivedfrom the original on 23 May 2020.Retrieved21 July2017.
- ^McCarthy, Kieren (20 July 2017)."Alphabay shutdown: Bad boys, bad boys, what you gonna do? Not use your Hotmail......or the Feds will get you ♪".The Register.Archivedfrom the original on 23 May 2020.Retrieved21 July2017.
- ^"Information Security Memo for Members".Democratic Socialists of America.11 July 2017.Archivedfrom the original on 20 January 2021.Retrieved20 January2021.
- ^"INFORMATION SECURITY RECOMMENDATIONS"(PDF).Democratic Socialists of America.June 2017.Archived(PDF)from the original on 7 September 2020.Retrieved20 January2021.
- ^Johnson, Tim (2 August 2017)."Shocked by gruesome crime, cyber execs help FBI on dark web".Idaho Statesman.
- ^Brandom, Russell (25 June 2018)."Venezuela is blocking access to the Tor network 16 Just days after new web blocks were placed on local media outlets".The Verge.Archivedfrom the original on 26 June 2018.Retrieved26 June2018.
- ^Grauer, Yael (4 July 2018)."German police raid homes of Tor-linked group's board members One board member described the police's justification for the raids as a" tenuous "link between the privacy group, a blog, and its email address".ZDNet.Archivedfrom the original on 6 July 2018.Retrieved6 July2018.
- ^n/a, 46halbe (4 July 2018)."Police searches homes of" Zwiebelfreunde "board members as well as" OpenLab "in Augsburg".Chaos Computer Club.Archivedfrom the original on 4 July 2018.Retrieved6 July2018.
{{cite web}}:CS1 maint: numeric names: authors list (link) - ^Stelle, Sharon (5 July 2018)."In Support of Torservers".TorProject.org.Archivedfrom the original on 7 July 2018.Retrieved6 July2018.
- ^"Gericht urteilt: Durchsuchung bei Zwiebelfreunden war rechtswidrig [Update]".24 August 2018.Archivedfrom the original on 12 October 2019.Retrieved1 December2019.
- ^"LG München I: Hausdurchsuchungen bei Verein Zwiebelfreunde waren rechtswidrig".Aktuell.Archivedfrom the original on 15 February 2021.Retrieved1 December2019.
- ^"China's clampdown on Tor pushes its hackers into foreign backyards".The Register.2018.Archivedfrom the original on 10 October 2018.Retrieved10 October2018.
- ^Stegner, Isabella (12 November 2019)."Edward Snowden blew the whistle on how Chinese censors scrubbed his book".Quartz.Archivedfrom the original on 15 November 2019.Retrieved12 November2019.
- ^Snowden, Edward (11 November 2019)."The Chinese edition of my new book, #PermanentRecord, has just been censored".Twitter (@Snowden).Archivedfrom the original on 12 November 2019.Retrieved8 December2019.
- ^"Russia Bans More VPN Products and TOR – December 8, 2021".Daily NewsBrief.8 December 2021.Archivedfrom the original on 8 December 2021.Retrieved11 December2021.
- ^"Russia Ratchets up Internet Control by Blocking Privacy Service Tor".U.S. News & World Report.Archivedfrom the original on 8 December 2021.Retrieved8 December2021.
- ^"Tor Project appeals Russian court's decision to block access to Tor".BleepingComputer.Archivedfrom the original on 8 March 2022.Retrieved8 March2022.
- ^Schechner, Sam; Hagey, Keach (12 March 2022)."Russia Rolls Down Internet Iron Curtain, but Gaps Remain".The Wall Street Journal.Archivedfrom the original on 17 March 2022.Retrieved17 March2022.
- ^abBurgess, Matt (28 July 2022)."How Tor Is Fighting—and Beating—Russian Censorship".WIRED.Archivedfrom the original on 8 August 2022.Retrieved30 July2022.
- ^"Russian court lifts block on Tor Project – for now".TechRadar.24 May 2022.Archivedfrom the original on 30 December 2022.Retrieved29 December2022.
- ^"Tor GitLab – [Russia] Some ISPs are blocking Tor".TechRadar.2 December 2021.Archivedfrom the original on 30 December 2022.Retrieved29 December2022.
- ^Browne, Ryan."VPN use skyrockets in Iran as citizens navigate internet censorship under Tehran's crackdown".CNBC.Archivedfrom the original on 10 October 2022.Retrieved11 October2022.
- ^Küchemann, Fridtjof (27 September 2022)."Per Snowflake ins TOR-Netzwerk: Online-Gasse für Menschen in Iran".Frankfurter Allgemeine Zeitung(in German).Archivedfrom the original on 10 October 2022.Retrieved11 October2022.
- ^Schwarzer, Matthias (30 September 2022)."Netzsperre im Iran umgehen: Wie" Snowflake "einen Weg ins freie Internet ermöglicht – so kann der Westen helfen".Redaktions Netzwerk Deutschland(in German). rnd.de.Archivedfrom the original on 10 October 2022.Retrieved10 October2022.
- ^Quintin, Cooper (4 October 2022)."Snowflake Makes It Easy For Anyone to Fight Censorship".Electronic Frontier Foundation.Archivedfrom the original on 10 October 2022.Retrieved11 October2022.
- ^"The Tor Project | Privacy & Freedom Online".torproject.org.Archivedfrom the original on 31 October 2019.Retrieved31 October2019.
- ^ab"Tor: Overview – Staying anonymous".Archivedfrom the original on 6 June 2015.Retrieved21 September2016.
- ^ab"Building a new Tor that can resist next-generation state surveillance".arstechnica.31 August 2016.Archivedfrom the original on 11 September 2016.Retrieved13 September2016.
- ^Groll, Elias; Francis, David (2 September 2016)."FBI: An Account on Clinton's Private Email Server Was Hacked".Foreign Policy.Archivedfrom the original on 31 October 2020.Retrieved28 October2020.
- ^"Aussie cops ran child porn site for months, revealed 30 US IPs".arstechnica.16 August 2016.Archivedfrom the original on 8 September 2016.Retrieved13 September2016.
- ^Ajaz, Shigraf (26 January 2023)."Tor Browser Privacy Setting-How to Setup Properly?".Beencrypted.Archivedfrom the original on 6 February 2023.Retrieved6 February2023.
- ^"SECURITY SETTINGS | Tor Project | Tor Browser Manual".tb-manual.torproject.org.Archivedfrom the original on 6 February 2023.Retrieved6 February2023.
- ^Pavel (Tor blog writer) (23 August 2023)."Introducing Proof-of-Work Defense for Onion Services".
General and cited references
[edit]- Bacard, Andre (1 January 1995).Computer Privacy Handbook.Peachpit Press.ISBN978-1-56609-171-8.
- Lund, Brady; Beckstrom, Matt (2021). "The Integration of Tor into Library Services: An Appeal to the Core Mission and Values of Libraries".Public Library Quarterly.40(1): 60–76.doi:10.1080/01616846.2019.1696078.S2CID214213117.
- Nurmi, Juha (24 May 2019).Understanding the Usage of Anonymous Onion Services: Empirical Experiments to Study Criminal Activities in the Tor Network.ISBN978-952-03-1091-2.
- Schneier, Bruce(1 November 1995).Applied Cryptography.Wiley.ISBN978-0-471-11709-4.
- Schneier, Bruce(25 January 1995).Email Security.Wiley.ISBN978-0-471-05318-7.
External links
[edit]- Official website

- Anonymity Bibliography
- Old website
- Archived: Official List of mirror websites
- "How Tor Browser Protects Your Privacy and Identity Online"—Animated introduction on YouTube
- Tor: Hidden Services and Deanonymisation—Presentation at the 31st Chaos Computer Conference
- TorFlow,a dynamic visualization of data flowing over the Tor network
- Tor onion services: more useful than you thinkin a 2016 presentation at the 32nd AnnualChaos Communication Congress
- A core Tor developer lecturesat theRadboud University Nijmegenin The Netherlands on anonymity systems in 2016
- A technical presentationgiven at theUniversity of Waterlooin Canada: Tor's Circuit-Layer Cryptography: Attacks, Hacks, and Improvements
- A Presentation at the March 2017 BSides Vancouver Conference on security practices on Tor's hidden servicesgiven bySarah Jamie Lewis
- Tor (anonymity network)
- 2002 software
- Application layer protocols
- Computer networking
- Cross-platform free software
- Cross-platform software
- Dark web
- File sharing
- Free network-related software
- Free routing software
- Free software programmed in C
- Free software programmed in Rust
- Hash-based data structures
- Internet privacy software
- Internet properties established in 2002
- Internet protocols
- Internet security
- Internet Standards
- Key-based routing
- Onion routing
- Overlay networks
- Proxy servers
- Software using the BSD license




